Preface: Bluetooth mesh is ideal for industrial IoT use cases—especially lighting—that require the relatively low-cost and low-power scalability, reliability, and performance of Bluetooth technology. It enables many-to-many device communications and is optimized for creating large-scale device networks.
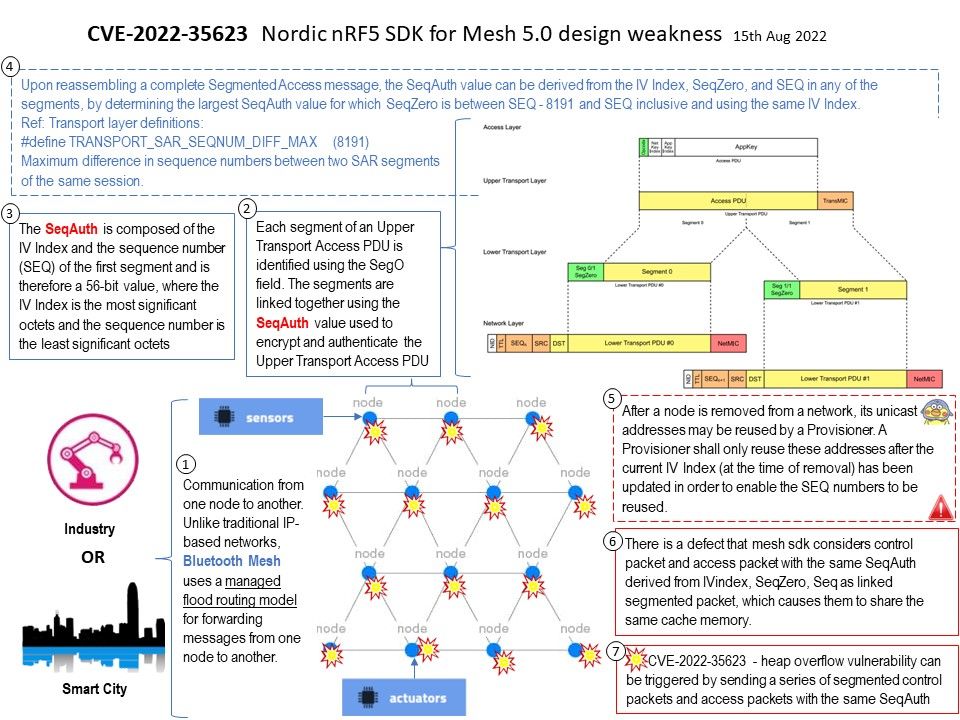
Background: Bluetooth mesh networks – Communication from one node to another. Unlike traditional IP-based networks, Bluetooth Mesh uses a managed flood routing model for forwarding messages from one node to another. In this model, messages are broadcast to each node in the vicinity and a time-to-live (TTL) is used to address the potential of a routing loop.
The nRF5 SDK for mesh is ideal for developing applications that use Bluetooth mesh networks .
Heap is a region of processes’s memory which is used to store dynamic variables. These variables are allocated using malloc() and calloc() functions and resize using realloc() function, which are inbuilt functions of C.
The function memcpy() is used to copy a memory block from one location to another. One is source and another is destination pointed by the pointer. This is declared in “string.h” header file in C language. It does not check overflow.
Vulnerability details: CVE-2022-35623 – In Nordic nRF5 SDK for Mesh 5.0, a heap overflow vulnerability can be triggered by sending a series of segmented control packets and access packets with the same SeqAuth. The vulnerable function is trs_seg_packet_in in mesh/core/src/transport[.]c.
Official details: https://docs.google.com/document/d/1Y3sB5JbyrTIOgvA1h9X6o8pJQBG4PjWF/edit
Additional: CVE-2022-35624 – In Nordic nRF5 SDK for Mesh 5.0, a heap overflow vulnerability can be triggered by sending a series of segmented packets with SegO > SegN.
https://docs.google.com/document/d/1BrgB1bQiL-cMXQGaXJWSSyaZY51Zxomp/edit
The vulnerable function is trs_seg_packet_in in mesh/core/src/transport[.]c.