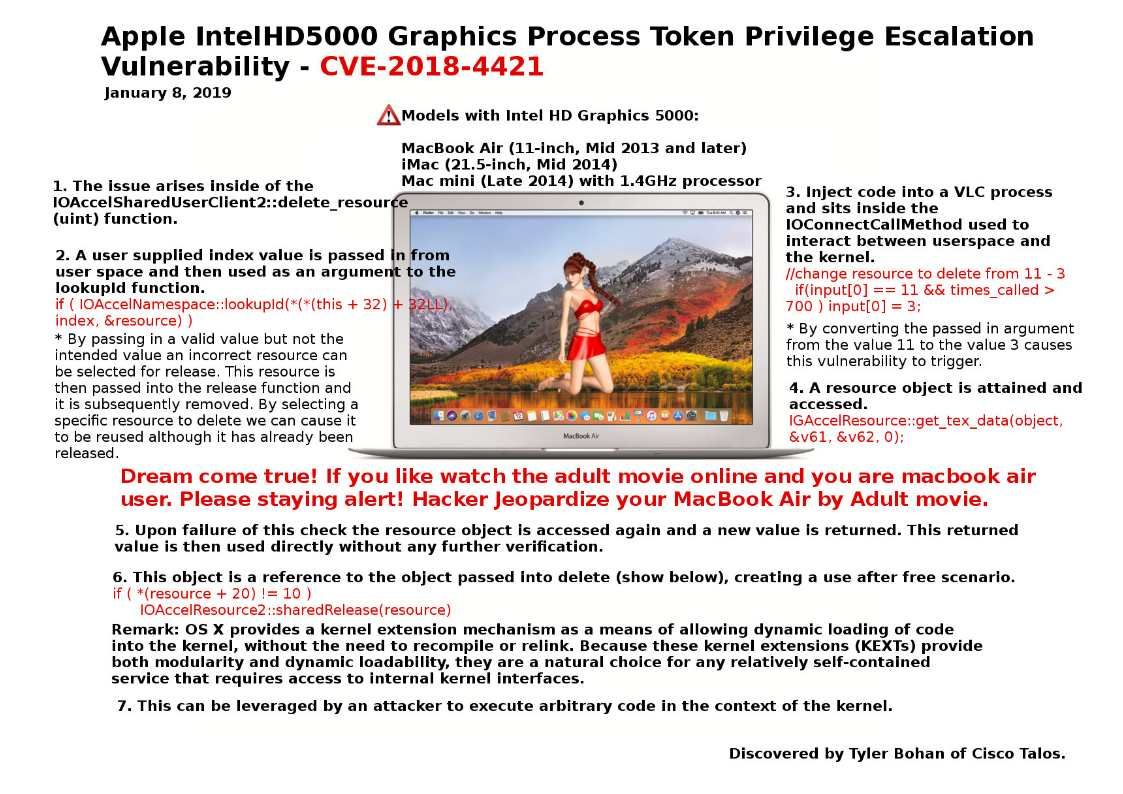
Preface: A third of people have a virus on their device from porn, said Dailymail.co.uk
Description: If you like watch the adult movie online and you are Mac book air user. Please staying alert! Hacker Jeopardize your Mac Book Air by Adult movie.
Impact: An application may be able to execute arbitrary code with kernel privileges.
OS X provides a kernel extension mechanism as a means of allowing dynamic loading of code into the kernel, without the need to recompile or relink. Because these kernel extensions (KEXTs) provide both modularity and dynamic loadability, they are a natural choice for any relatively self-contained service that requires access to internal kernel interfaces. A memory corruption vulnerability exists in the IntelHD5000 kernel extension when dealing with graphics resources inside of OSX 10.13.4. A library inserted into the VLC media application can cause an out-of-bounds access inside of the KEXT leading to a use after free and invalid memory access in the context of the kernel. This can be used for privilege escalation.
Official announcement: https://support.apple.com/en-il/HT209341