
Preface
The 21st century is the current century of the Anno Domini era, in accordance with the Gregorian calendar. It began on January 1, 2001 and will end on December 31, 2100. It is the first century of the 3rd millennium.
We can’t tolerate cyber attack happen in election again, President said.
Headline news told that former president Obaman intend to use new technique to reduce other country especially Russia engage the cyber attack to USA during 2016 election of president. The solution is that activate a cyber bomb technique. But this idea did not action yet.
What is a logic bomb?
A logic bomb is a piece of code intentionally inserted into a software system that will set off a malicious function when specified conditions are met. The technical term so called slag code.
What is slag code?
It is not a virus, but works in a similar pattern. From technical point of view, slag code sounds like a set of instructions inserted into a program that are designed to execute the target action (sounds like “explode”).
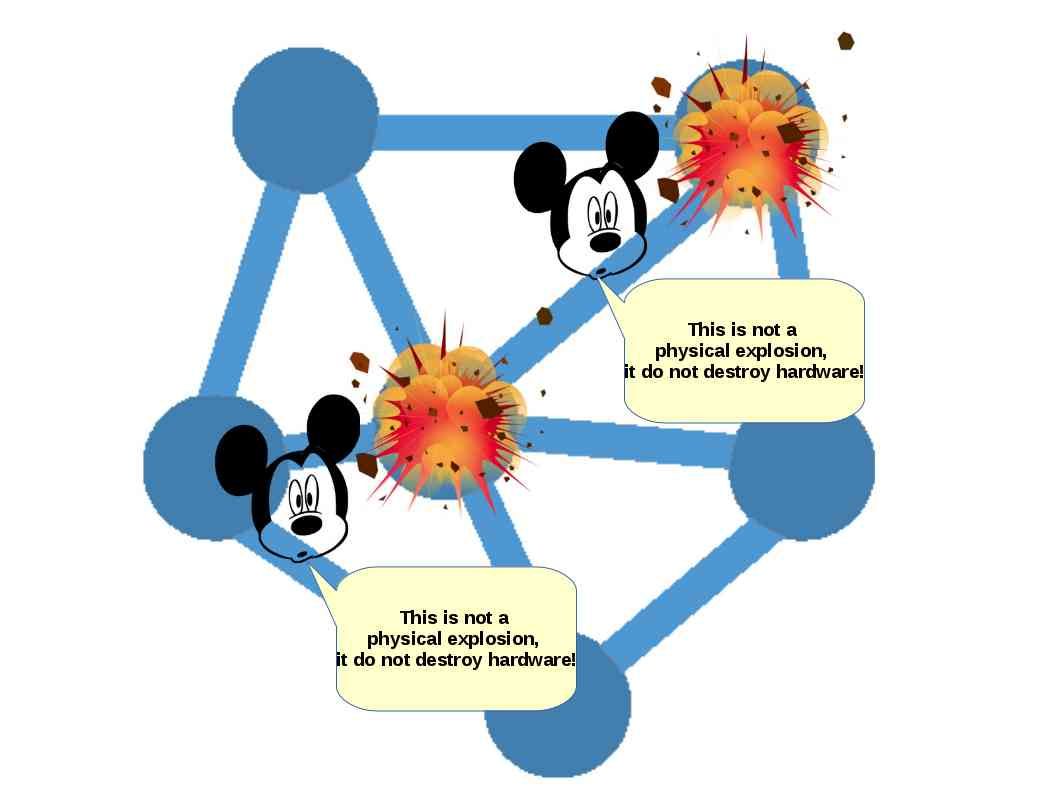
Scenario – The technical term so called network exploded. The result of this explosion contains delete data ,corrupt data or have other harmful effects.
Concept:
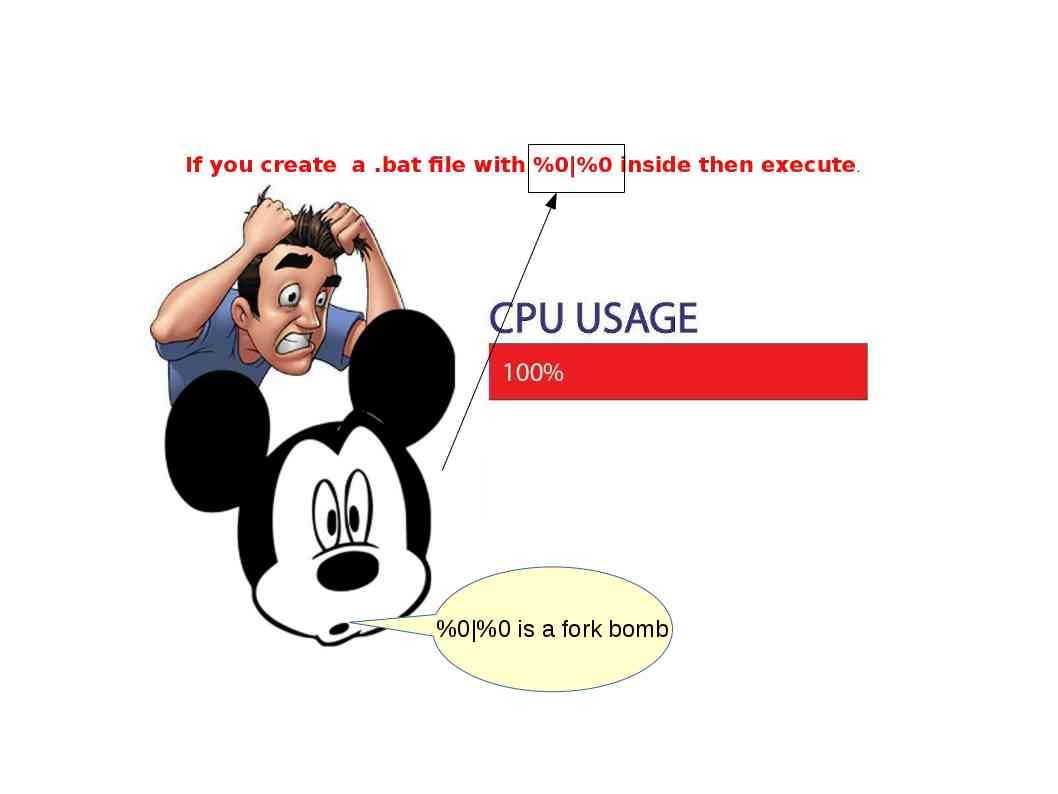
Below example (Picture A) shown that only implement a simple command syntax to a windows workstation. The process will consume all the CPU resources until windows OS shutdown. This is the concept idea of a slag code. Do you think similar attack concept can whether be affect the services provider network equipment?
Picture A – slag code
How powerful of the cyber bomb, is it possible?
Above concept can show you that your workstation execute a slag code and result not operation properly. The service get back normal until reboot. What if, the telecommunication services provider receive the slav code crafted by expert. What’s the worst situation is?
Logic Bomb
Logic Bomb 1 – infectious media (malware)
The logic bomb goal to achieve a destructive result. The infectious media relies on malware. The malware structure will be consists of a executable file ( Agent.exe ). This file is for triggered the wiping function. Besides this file contains a hex string. For example – a hex string display 65B417D8. When we convert the hex code to numeric value, it indicate that this is the date and time of the attack to begin (June 30, 2017 at 2pm local time (2017-6-30 14:00:00)). As soon as the internal system clock on the machine hit 14:00:01, the wiper (agent) was triggered to overwrite the hard drive and master boot record on Microsoft OS of machines and then reboot the system. The malicious code can access and compromise Windows-based systems inside the industrial control network. After a Windows system has been infected, the weapon would be stealthy enough to evade IT security controls while it searches for a target system
Logic Bomb 2 – A persistent attack (the packets being constantly injected)
A persistent attack occurs when the attacker would put bad packets into a router and it would lead to vulnerabilities being exploited/revealed during the process. Significant damage can occur during this attack because packets would be flooded into the router and can end up suspend the routing function.
Remark: These attacks are very complicated to detect.
Logic Bomb 3 – The mistrating attacks
The mistreating attacks can be caused indirectly by directing an irresistible number of packers to the target victim address. Let the victim (router and network) isolated. In the means that the network services will be suspended.
Cyber warfare arsenal (major weapon)
Ransomware
Since this topic we discussed in past , for more details, please see below URL for reference.
The other side of the story on cyber attack (Electronic war between countries)
Informaiton Supplement – BGP hijack attack
Below idea show a rogue AS falsely advertises a shorter path to reach a prefix P, which causes other AS’es to route traffic destined to the prefix P through the shorter path.
There are four AS’s: AS1, AS2, AS3 and AS4 (rogue).
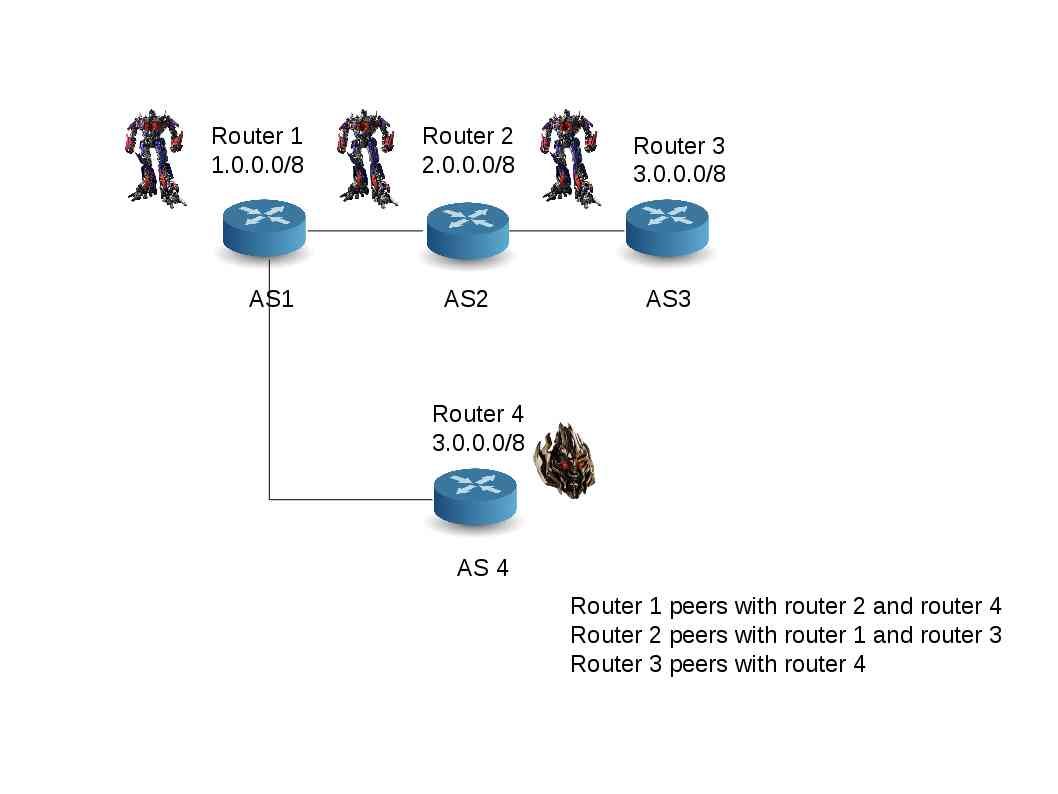
Each routing daemon’s peers are shown using connections:
- Router 1 peers with router 2 and router 4.
- Router 2 peers with router 1 and router 3.
- Router 3 peers with router 4.
1 – Show router 1 routing entries
BGP table version is 0, local router ID is 9.0.0.1 Network Next Hop Metric LocPrf Weight Path 1.0.0.0 0.0.0.0 0 32768 i 2.0.0.0 9.0.0.2 0 0 2 i 3.0.0.0 9.0.0.2 0 2 3 i
Reminder A: On AS1, the chosen AS path to reach 3.0.0.0/8 is “2 3” (i.e., via AS2 and AS3).
2: Start the rogue AS, the rogue AS will connect to AS1 and advertise a route to 3.0.0.0/8 using a shorter path (i.e., a direct path from AS1 to AS4). Thus, AS1 will choose this shorter path by default.
3. Show router 1 routing entries again
BGP table version is 0, local router ID is 9.0.0.1 Network Next Hop Metric LocPrf Weight Path 1.0.0.0 0.0.0.0 0 32768 i 2.0.0.0 9.0.0.2 0 0 2 i 3.0.0.0 9.0.4.2 0 0 4 i 9.0.0.2 0 2 3 i
We can see AS4’s chosen path and also AS3’s path in the routing information base of AS1.
Since the AS path length to reach 3.0.0.0/8 is smaller through AS4, router 1 chooses AS4 as its next hop.
From technical point of view, it successfully hijack the traffic in BGP network. We known internet routing protocol is using BGP. No suprise, this is only a basic theory. More complex and advance technique is under develop by different countries.
See who show his power to the world.
Observation:
On our discussion of this topic, I am not going to input key word conclusion on the end of page this time. As we know, above items is my speculation. Believed it or not , the cyber attack atmosphere looks similar with discussion in past.
But bear in mind that any product includes cyber weapon require test and pilot run. These rehearsal looks mandatory since it is hard to foreseen the overall damage effect (including the response of the countries). On the other hand it is a test to know the actual system specification in hostile country. It compared to traditional way become more effective! Hire a spy infiltrate to hostile country is not the way today. Do you agree?
I am going to write more interested topics. Hope you will be interest. See you. Have a nice weekend.
What theme is this? Love it!
Thank you for another excellent article. Where else may just anybody get that type of info in such an ideal way of writing? I’ve a presentation next week, and I am on the look for such info.
heyhello there and thank you for your informationinfo – I’veI have definitelycertainly picked up anythingsomething new from right here. I did however expertise somea fewseveral technical issuespoints using this web sitesitewebsite, sinceas I experienced to reload the siteweb sitewebsite manya lot oflots of times previous to I could get it to load properlycorrectly. I had been wondering if your hostingweb hostingweb host is OK? Not that I amI’m complaining, but sluggishslow loading instances times will very frequentlyoftensometimes affect your placement in google and cancould damage your high qualityqualityhigh-quality score if advertisingads and marketing with Adwords. AnywayWell I’mI am adding this RSS to my e-mailemail and cancould look out for a lotmuch more of your respective intriguingfascinatinginterestingexciting content. Make sureEnsure that you update this again soonvery soon.
I have been checking out many of your posts and i must say pretty nice stuff. I will surely bookmark your site.
I simply could not leave your web site before suggesting that I actually enjoyed the usual information an individual supply on your guests? Is gonna be again regularly to inspect new posts.
hello!,I love your writing so a lot! percentage we keep up a correspondence extra approximately your article on AOL? I require an expert in this space to resolve my problem. May be that is you! Looking forward to peer you.
I conceive this internet site holds some real good info for everyone :D. “Do not go where the path may lead, go instead where there is no path and leave a trail.” by Ralph Waldo Emerson.
As soon as I found this website I went on reddit to share some of the love with them.
excellent put up, very informative. I wonder why the opposite specialists of this sector don’t understand this. You should proceed your writing. I am confident, you’ve a great readers’ base already!
I’ve recently started a website, the info you offer on this website has helped me tremendously. Thanks for all of your time & work.
Undeniably believe that which you said. Your favorite justification appeared to be on the web the simplest thing to be aware of. I say to you, I certainly get irked while people think about worries that they just don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side effect , people can take a signal. Will probably be back to get more. Thanks
I enjoy, result in I found exactly what I was looking for. You’ve ended my four day long hunt! God Bless you man. Have a nice day. Bye
As I web site possessor I believe the content material here is rattling great , appreciate it for your efforts. You should keep it up forever! Best of luck.
Great site! I am loving it!! Will be back later to read some more. I am taking your feeds also
Thanks, I have recently been searching for information approximately this subject for a long time and yours is the best I have discovered so far. But, what about the conclusion? Are you sure in regards to the supply?
Hi my loved one! I want to say that this article is amazing, great written and come with almost all important infos. I’d like to see extra posts like this.
I like what you guys are up too. Such smart work and reporting! Carry on the superb works guys I’ve incorporated you guys to my blogroll. I think it’ll improve the value of my website :).
I want to show some appreciation to the writer just for rescuing me from such a issue. Just after checking throughout the online world and getting views that were not productive, I figured my entire life was gone. Being alive devoid of the solutions to the difficulties you have resolved by way of this blog post is a serious case, as well as the kind which could have badly damaged my career if I had not noticed your web page. Your good skills and kindness in taking care of the whole thing was important. I don’t know what I would have done if I hadn’t come upon such a point like this. I can at this point relish my future. Thank you very much for your high quality and results-oriented guide. I will not be reluctant to recommend your web site to anyone who would like counselling about this issue.
Great site. Lots of helpful information here. I¡¦m sending it to several buddies ans also sharing in delicious. And of course, thank you to your effort!
Someone necessarily help to make significantly articles I would state. This is the first time I frequented your website page and so far? I surprised with the research you made to make this actual publish incredible. Wonderful job!
Fantastic site. A lot of useful info here. I’m sending it to several buddies ans also sharing in delicious. And certainly, thank you to your effort!
Thanks for your blog post. Some tips i would like to contribute is that computer memory must be purchased in case your computer cannot cope with whatever you do with it. One can mount two random access memory boards containing 1GB each, for example, but not one of 1GB and one of 2GB. One should look for the maker’s documentation for own PC to make certain what type of memory is required.
I’m impressed, I must say. Seldom do I encounter a blog that’s both equally educative and amusing, and without a doubt, you have hit the nail on the head. The issue is something which not enough people are speaking intelligently about. Now i’m very happy I came across this during my search for something regarding this.
Hello, Neat post. There’s an issue along with your website in internet explorer, may test this… IE nonetheless is the marketplace leader and a big component to people will pass over your magnificent writing because of this problem.
My brother suggested I might like this blog. He was totally right. This post actually made my day. You can not imagine just how much time I had spent for this information! Thanks!
I would like to express some thanks to this writer for bailing me out of this type of trouble. Just after exploring through the world wide web and meeting ideas which are not powerful, I assumed my life was gone. Being alive without the presence of solutions to the issues you’ve solved by way of your good blog post is a crucial case, as well as the kind which could have badly damaged my entire career if I hadn’t come across the website. Your good training and kindness in touching all the stuff was tremendous. I don’t know what I would have done if I had not encountered such a subject like this. I can at this moment look ahead to my future. Thanks so much for this reliable and sensible help. I won’t be reluctant to refer the blog to anybody who would like direction about this problem.
Some genuinely prime articles on this site, saved to my bookmarks .
My brother suggested I might like this web site. He was totally right. This post truly made my day. You can not imagine simply how much time I had spent for this info! Thanks!
I actually wanted to make a quick note to express gratitude to you for those stunning suggestions you are writing at this website. My extended internet lookup has at the end been recognized with beneficial ideas to go over with my friends and family. I would declare that most of us readers are very blessed to exist in a remarkable community with very many wonderful professionals with beneficial suggestions. I feel very much blessed to have seen your webpage and look forward to really more entertaining moments reading here. Thanks a lot once more for all the details.
Thanks for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such magnificent information being shared freely out there.
Wonderful goods from you, man. I’ve understand your stuff previous to and you are just too magnificent. I really like what you have acquired here, really like what you’re stating and the way in which you say it. You make it enjoyable and you still care for to keep it smart. I cant wait to read far more from you. This is actually a wonderful web site.
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again!
whoah this blog is excellent i really like studying your articles. Keep up the great paintings! You recognize, lots of persons are looking around for this info, you can aid them greatly.
Very interesting subject, appreciate it for putting up.
Hi my loved one! I wish to say that this article is awesome, nice written and include almost all vital infos. I¡¦d like to peer more posts like this .
I wish to express some appreciation to the writer just for rescuing me from such a incident. After searching through the internet and meeting suggestions that were not pleasant, I was thinking my life was done. Existing without the presence of answers to the difficulties you’ve resolved all through your entire site is a critical case, as well as those that would have negatively affected my entire career if I had not discovered your blog post. Your personal knowledge and kindness in dealing with a lot of stuff was crucial. I don’t know what I would’ve done if I hadn’t come across such a solution like this. I’m able to now look ahead to my future. Thanks so much for your high quality and effective guide. I won’t be reluctant to refer your blog to any individual who needs to have tips on this problem.
I¡¦ve learn several just right stuff here. Definitely worth bookmarking for revisiting. I surprise how much attempt you place to create this kind of magnificent informative web site.
Great work! That is the kind of info that are supposed to be shared around the web. Disgrace on the seek engines for no longer positioning this publish higher! Come on over and seek advice from my website . Thank you =)
Hi there, You’ve done an incredible job. I’ll certainly digg it and personally suggest to my friends. I’m confident they’ll be benefited from this web site.
Thanks , I have recently been searching for information approximately this topic for ages and yours is the greatest I’ve found out so far. But, what about the conclusion? Are you sure about the source?
Someone essentially lend a hand to make significantly articles I’d state. This is the very first time I frequented your website page and to this point? I surprised with the analysis you made to make this particular publish incredible. Magnificent activity!
You have brought up a very excellent details , thankyou for the post.
Pretty section of content. I just stumbled upon your website and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your augment and even I achievement you access consistently rapidly.
fantastic points altogether, you simply gained a brand new reader. What would you suggest in regards to your submit that you made a few days ago? Any positive?
I want to show my gratitude for your kindness giving support to people who need guidance on your idea. Your real dedication to passing the message across ended up being particularly good and have in every case made ladies just like me to attain their pursuits. Your entire insightful facts signifies much to me and substantially more to my fellow workers. Regards; from everyone of us.
Wonderful beat ! I wish to apprentice while you amend your web site, how could i subscribe for a blog web site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
I in addition to my guys were found to be digesting the nice tips and tricks on the website and then instantly came up with a horrible feeling I had not expressed respect to the blog owner for those strategies. The young men ended up for this reason joyful to see them and already have surely been having fun with those things. Appreciation for indeed being very kind and then for making a choice on such awesome issues millions of individuals are really desperate to be aware of. My very own sincere apologies for not expressing gratitude to sooner.
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I’ll be subscribing to your feeds and even I achievement you access consistently rapidly.
I just couldn’t leave your website before suggesting that I actually loved the standard info an individual supply to your guests? Is gonna be back continuously to inspect new posts.
Some genuinely good information, Gladiolus I discovered this. “We go where our vision is.” by Joseph Murphy.
I will right away clutch your rss as I can not find your email subscription link or e-newsletter service. Do you have any? Please allow me recognize in order that I may just subscribe. Thanks.
Valuable info. Lucky me I found your site by chance, and I am shocked why this accident didn’t took place in advance! I bookmarked it.
Needed to post you the very little note just to thank you over again for your personal remarkable advice you have discussed in this case. This is tremendously generous with people like you to supply openly just what a number of people could possibly have offered for an electronic book to end up making some dough for themselves, primarily considering that you might well have done it if you wanted. Those things additionally acted as the fantastic way to recognize that the rest have the identical interest just as mine to figure out a good deal more with regard to this condition. I am certain there are thousands of more pleasurable occasions ahead for individuals that go through your website.
I genuinely enjoy looking through on this internet site , it contains fantastic content . “Those who complain most are most to be complained of.” by Matthew Henry.
You are my intake , I have few web logs and infrequently run out from to brand.
Good ¡V I should certainly pronounce, impressed with your site. I had no trouble navigating through all tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your customer to communicate. Nice task..
Perfectly composed written content , appreciate it for selective information .
Hi, i think that i saw you visited my website so i came to “return the favor”.I am trying to find things to improve my site!I suppose its ok to use a few of your ideas!!
I really enjoy reading on this website , it holds great articles . “Heavier-than-air flying machines are impossible.” by Lord Kelvin.
Wow! This can be one particular of the most useful blogs We have ever arrive across on this subject. Basically Fantastic. I’m also a specialist in this topic so I can understand your hard work.
I as well as my friends were found to be following the excellent techniques located on your site while at once got a horrible feeling I had not thanked the site owner for those tips. My young men became as a consequence thrilled to learn them and have pretty much been having fun with them. I appreciate you for truly being quite helpful and then for deciding on varieties of incredible subjects millions of individuals are really wanting to know about. Our own sincere apologies for not expressing gratitude to sooner.
Thank you, I have recently been searching for info about this topic for ages and yours is the greatest I’ve came upon so far. But, what in regards to the bottom line? Are you certain concerning the supply?
Some really choice articles on this internet site , saved to fav.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how could we communicate?
Just want to say your article is as astounding. The clarity in your post is simply great and i can assume you are an expert on this subject. Well with your permission allow me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please continue the enjoyable work.
I genuinely enjoy reading through on this site, it contains superb articles . “Sometime they’ll give a war and nobody will come.” by Carl Sandburg.
of course like your website however you have to test the spelling on several of your posts. Several of them are rife with spelling problems and I find it very bothersome to tell the truth nevertheless I¡¦ll surely come back again.
You could certainly see your expertise within the work you write. The sector hopes for more passionate writers such as you who are not afraid to say how they believe. All the time follow your heart. “We may pass violets looking for roses. We may pass contentment looking for victory.” by Bern Williams.
You are my breathing in, I own few web logs and sometimes run out from to brand.I conceive this internet site has some really great information for everyone. “The human spirit needs to accomplish, to achieve, to triumph to be happy.” by Ben Stein.
This is really interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your great post. Also, I’ve shared your web site in my social networks!
Whats Taking place i am new to this, I stumbled upon this I’ve found It absolutely useful and it has helped me out loads. I’m hoping to contribute & aid other users like its helped me. Great job.
I’ve been browsing online more than three hours today, yet I by no means discovered any fascinating article like yours. It is beautiful price enough for me. In my view, if all site owners and bloggers made just right content as you did, the internet will probably be much more helpful than ever before. “When you are content to be simply yourself and don’t compare or compete, everybody will respect you.” by Lao Tzu.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how can we communicate?
I was recommended this blog by my cousin. I am not sure whether this post is written by him as no one else know such detailed about my difficulty. You’re incredible! Thanks!
Definitely believe that which you said. Your favorite reason appeared to be on the internet the simplest thing to be aware of. I say to you, I definitely get irked while people think about worries that they just do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people could take a signal. Will probably be back to get more. Thanks
We’re a group of volunteers and starting a new scheme in our community. Your site provided us with valuable info to work on. You have done a formidable job and our entire community will be grateful to you.
Heya i am for the first time here. I came across this board and I find It really useful & it helped me out much. I hope to give something back and help others like you helped me.
Very wonderful information can be found on weblog . “Time discovers truth.” by Lucius Annaeus Seneca.
Very interesting topic , thanks for putting up. “The great aim of education is not knowledge but action.” by Herbert Spencer.
I got what you mean , appreciate it for posting .Woh I am lucky to find this website through google. “Do not be too timid and squeamish about your actions. All life is an experiment.” by Ralph Waldo Emerson.
Terrific work! That is the kind of information that are meant to be shared across the internet. Shame on the search engines for now not positioning this submit upper! Come on over and discuss with my website . Thanks =)
Hello, Neat post. There’s a problem with your web site in web explorer, could test this… IE nonetheless is the marketplace chief and a big element of other folks will leave out your great writing because of this problem.
Some really quality posts on this website , saved to my bookmarks .
I do not even know how I finished up here, but I believed this put up was once great. I don’t understand who you are but certainly you’re going to a well-known blogger in the event you aren’t already 😉 Cheers!
I must convey my passion for your kind-heartedness in support of individuals that really need guidance on this one area of interest. Your real commitment to passing the message around became amazingly invaluable and have frequently enabled guys and women much like me to arrive at their endeavors. Your personal invaluable key points means much a person like me and even further to my office workers. Thanks a lot; from all of us.
Magnificent goods from you, man. I’ve understand your stuff previous to and you are just extremely great. I actually like what you have acquired here, certainly like what you are saying and the way in which you say it. You make it entertaining and you still care for to keep it wise. I cant wait to read much more from you. This is really a great web site.
I think other web-site proprietors should take this web site as an model, very clean and wonderful user genial style and design, let alone the content. You’re an expert in this topic!
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again!
Some really superb posts on this internet site , thanks for contribution.
Unquestionably believe that which you said. Your favorite justification appeared to be on the net the simplest thing to be aware of. I say to you, I definitely get irked while people consider worries that they plainly don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people can take a signal. Will likely be back to get more. Thanks
Hello there! This is my first comment here, so I just wanted to give a quick shout out and say I genuinely enjoy reading your articles. Can you recommend any other blogs/websites/forums that deal with the same subjects? Thanks.
My brother suggested I might like this website. He was totally right. This post actually made my day. You cann’t imagine just how much time I had spent for this information! Thanks!
Great remarkable issues here. I am very happy to look your article. Thanks so much and i am taking a look ahead to touch you. Will you please drop me a e-mail?
Lovely website! I am loving it!! Will come back again. I am bookmarking your feeds also
Hello there, I discovered your blog by means of Google at the same time as looking for a similar subject, your site came up, it looks good. I have bookmarked it in my google bookmarks.
I am continually browsing online for tips that can assist me. Thanks!
Good read, enjoyed it!
Whats Taking place i am new to this, I stumbled upon this I’ve found It absolutely useful and it has aided me out loads. I hope to contribute & aid different customers like its aided me. Good job.
Very well written story. It will be beneficial to anyone who employess it, including myself. Keep up the good work – for sure i will check out more posts.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how could we communicate?
Just want to say your article is as astonishing. The clearness in your post is simply excellent and i can assume you are an expert on this subject. Well with your permission let me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the gratifying work.
I have not checked in here for a while since I thought it was getting boring, but the last several posts are great quality so I guess I¡¦ll add you back to my everyday bloglist. You deserve it my friend 🙂
magnificent issues altogether, you simply received a brand new reader. What may you suggest about your publish that you simply made a few days in the past? Any sure?
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but definitely you’re going to a famous blogger if you aren’t already 😉 Cheers!
Thanks a bunch for sharing this with all folks you really understand what you’re talking approximately! Bookmarked. Please also visit my web site =). We may have a hyperlink change contract among us!
Normally I don’t learn article on blogs, however I wish to say that this write-up very pressured me to try and do it! Your writing style has been surprised me. Thanks, very great article.
I am glad for commenting to let you be aware of what a terrific experience my girl enjoyed viewing your blog. She learned lots of things, which included how it is like to possess an ideal coaching style to let the mediocre ones without hassle fully understand a number of extremely tough subject areas. You undoubtedly exceeded our own desires. I appreciate you for rendering these great, dependable, educational and in addition cool thoughts on that topic to Sandra.
Whats Going down i am new to this, I stumbled upon this I’ve found It positively helpful and it has helped me out loads. I hope to give a contribution & help other customers like its helped me. Good job.
You completed certain fine points there. I did a search on the theme and found mainly persons will consent with your blog.
experiencing some small security issues with my latest blog, and I’d like to find something safer. Do you have any suggestions?
As I site possessor I believe the content matter here is rattling magnificent , appreciate it for your efforts. You should keep it up forever! Good Luck.
I just want to tell you that I am newbie to weblog and certainly liked you’re web blog. Probably I’m planning to bookmark your blog post . You absolutely have amazing well written articles. Bless you for sharing with us your web site.
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Yeah bookmaking this wasn at a bad determination outstanding post!
Yeah bookmaking this wasn at a bad determination outstanding post!
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Major thanks for the article.Really thank you! Will read on
Some truly prime content on this website , saved to my bookmarks .
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
Say, you got a nice article post.Really looking forward to read more. Will read on
Some truly prime content on this website , saved to my bookmarks .
I just want to say I am all new to blogging and site-building and certainly enjoyed your web site. Very likely I’m planning to bookmark your blog post . You absolutely have outstanding posts. Kudos for sharing your blog site.
Very good article post.Really thank you! Will read on.
I gotta favorite this internet site it seems very helpful very useful
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
I gotta favorite this internet site it seems very helpful very useful
Thanks a lot for the article post.Really looking forward to read more.
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
I gotta favorite this internet site it seems very helpful very useful
Thanks a lot for the article post.Really looking forward to read more.
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
pretty valuable material, overall I believe this is worth a bookmark, thanks
Some truly prime content on this website , saved to my bookmarks .
pretty valuable material, overall I believe this is worth a bookmark, thanks
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
I gotta favorite this internet site it seems very helpful very useful
Yeah bookmaking this wasn at a bad determination outstanding post!
Yeah bookmaking this wasn at a bad determination outstanding post!
Thanks a lot for the article post.Really looking forward to read more.
Major thanks for the article.Really thank you! Will read on
Some truly prime content on this website , saved to my bookmarks .
Some truly prime content on this website , saved to my bookmarks .
Say, you got a nice article post.Really looking forward to read more. Will read on
Some truly prime content on this website , saved to my bookmarks .
Yeah bookmaking this wasn at a bad determination outstanding post!
I gotta favorite this internet site it seems very helpful very useful
Major thanks for the article.Really thank you! Will read on
Very good article post.Really thank you! Will read on
I just want to say I am very new to blogging and site-building and really enjoyed your web blog. Very likely I’m planning to bookmark your blog post . You really have good writings. Appreciate it for sharing your website page.
Thanks a lot for the article post.Really looking forward to read more.
Keep on workingthis going pleaseon writing, great job!
No one seems to know what’s going on with that pot of noodles on the stove. I know not a least one of you have looked at them.
“Hello there, You’ve done an incredible job. I’ll certainly digg it and personally suggest to my friends. I’m sure they’ll be benefited from this web site.”
Keep functioning ,remarkable job!
I haven’t checked in here for some time as I thought it was getting boring, but the last several posts are good quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
Simply wanna input that you have a very nice website , I like the design it really stands out.
(Existing without the answers to the difficulties you’ve sorted out through this guide is a critical case, as well as the kind which could have badly affected my entire career if I had not discovered your website.
What a fantabulous post this has been. Never seen this kind of useful post. I am grateful to you and expect more number of posts like these. Thank you very much.
Your writing taste has been amazed me. Thank you, very nice article.)
Someone essentially assist to make critically posts I might state. This is the very first time I frequented your web page and to this point? I amazed with the research you made to create this actual submit extraordinary. Excellent job!
I simply want to tell you that I am just very new to blogging and certainly savored you’re web-site. Almost certainly I’m likely to bookmark your blog post . You certainly come with wonderful stories. Many thanks for sharing with us your blog site.
What’s Taking placeHappeningGoing down i’mi am new to this, I stumbled upon this I haveI’ve founddiscovered It positivelyabsolutely helpfuluseful and it has helpedaided me out loads. I am hopingI hopeI’m hoping to give a contributioncontribute & assistaidhelp otherdifferent userscustomers like its helpedaided me. GoodGreat job.
GreatVery niceInformativePeculiar article, exactlyjusttotally what I neededwanted to findwas looking for.
This is veryreally interesting, You areYou’re a very skilled blogger. I haveI’ve joined your feedrss feed and look forward to seeking more of your greatwonderfulfantasticmagnificentexcellent post. Also, I haveI’ve shared your siteweb sitewebsite in my social networks!
I hardly create remarks, however i did a few searching and wound up here . And I actually do have some questions for you if you tend not to mind. Is it just me or does it look like some of these comments appear like written by brain dead individuals? 😛 And, if you are writing at other social sites, I would like to follow anything new you have to post. Would you make a list of the complete urls of your community sites like your Facebook page, twitter feed, or linkedin profile?
Do you mind if I quote a few of your posts as long as I provide credit and sources back to your blog? My site is in precisely the same market as yours, and my customers would benefit from some of the information you provide here. Please let me know if this okay with you. Thank you. {
It is great to come across a site every once in a while which is not exactly the same out of date rehashed material. Fantastic read.