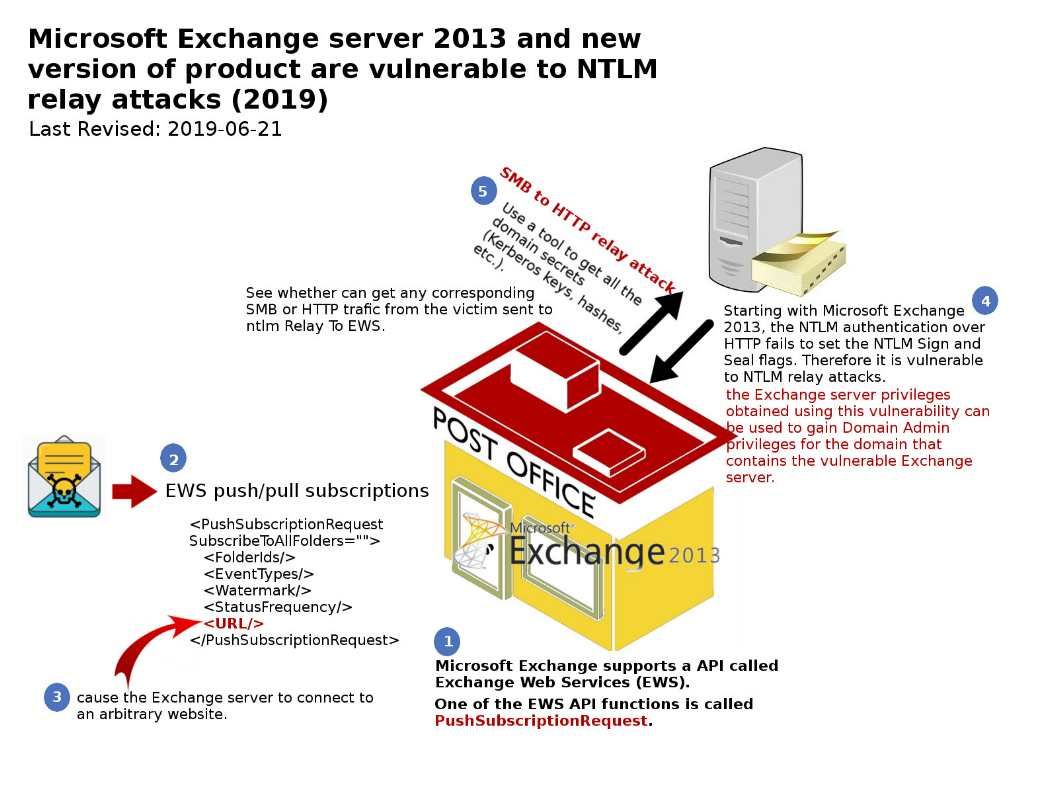
Preface: A privilege escalation is possible from the Exchange Windows permissions (EWP) security group to compromise the entire prepared Active Directory domain.
Vulnerability details: A tool capable for performing ntlm relay attacks on Exchange Web Services (EWS). It spawns an SMBListener on port 445 and an HTTP Listener on port 80, waiting for incoming connection from the victim. Once the victim connects to one of the target, an NTLM negociation occurs and is relayed to the target EWS server.
Hints: Do not contempt the vulnerability on workstation. It is one of the way which assists the hacker to do the privileges escalation. If the compromised workstation is the domain member. Hacker relies on NTLM vulnerability to do the priviliges escalation. That is, they remotely execute malicious code on any Windows machine or authenticate to any HTTP server that supports Windows Integrated Authentication (WIA). For instance, the Exchange server and ADFS (Active Directory Federation Services).
Official announcement:
Apply an update – https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0686
Disable EWS push/pull subscriptions – In an Exchange Management console, execute the following commands:
- New-ThrottlingPolicy -Name NoEWSSubscription -ThrottlingPolicyScope
- Organization -EwsMaxSubscriptions 0
- Restart-WebAppPool -Name MSExchangeServicesAppPool