.jpg)
Preface: Sometimes, a low to medium risk rating vulnerability will be transformed into potential risk.
Background: Aruba’s ClearPass Policy Manager, part of the Aruba 360 Secure Fabric, provides role- and device-based secure network access control for IoT, BYOD & corporate devices.
The ClearPass Policy Manager is the only policy solution that centrally enforces all aspects of enterprise-grade mobility and NAC for any industry. Granular network access enforcement is based on a user’s role, device type and role, authentication method, EMM/MDM attributes, device health, location, and time-of-day.
Vulnerability details: Publication Date: 2021-Oct-12 (see below):
CVE-2021-37736, CVE-2021-37737, CVE-2021-37738, CVE-2021-37739, CVE-2021-40986, CVE-2021-40987, CVE-2021-40988, CVE-2021-40989, CVE-2021-40990, CVE-2021-40991, CVE-2021-40992, CVE-2021-40993, CVE-2021-40994, CVE-2021-40995, CVE-2021-20996, CVE-2021-40997, CVE-2021-40998, CVE-2021-40999.
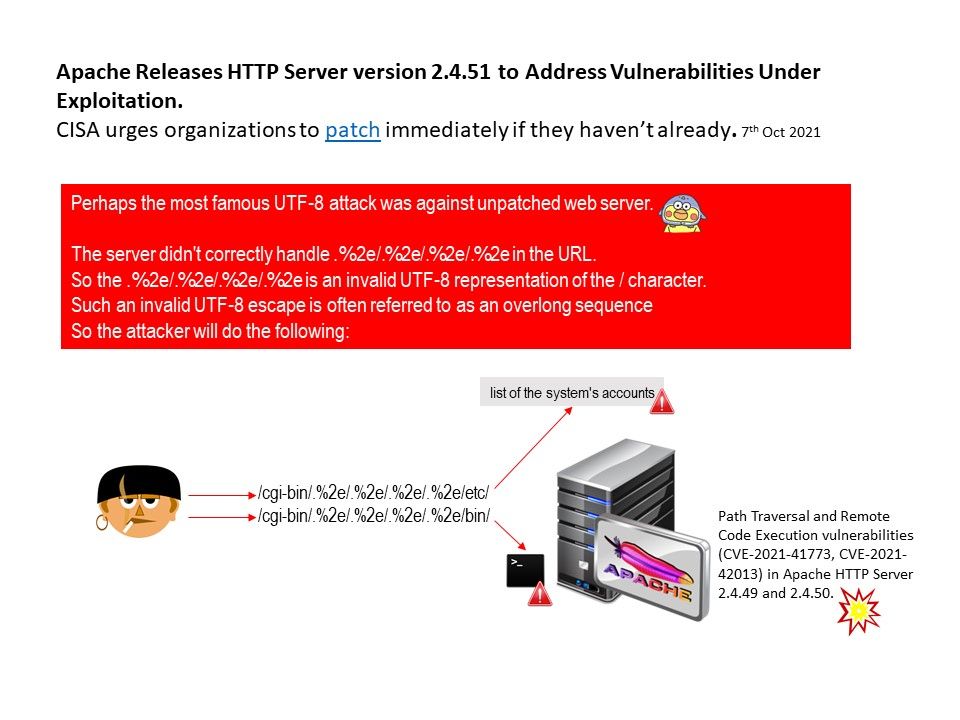
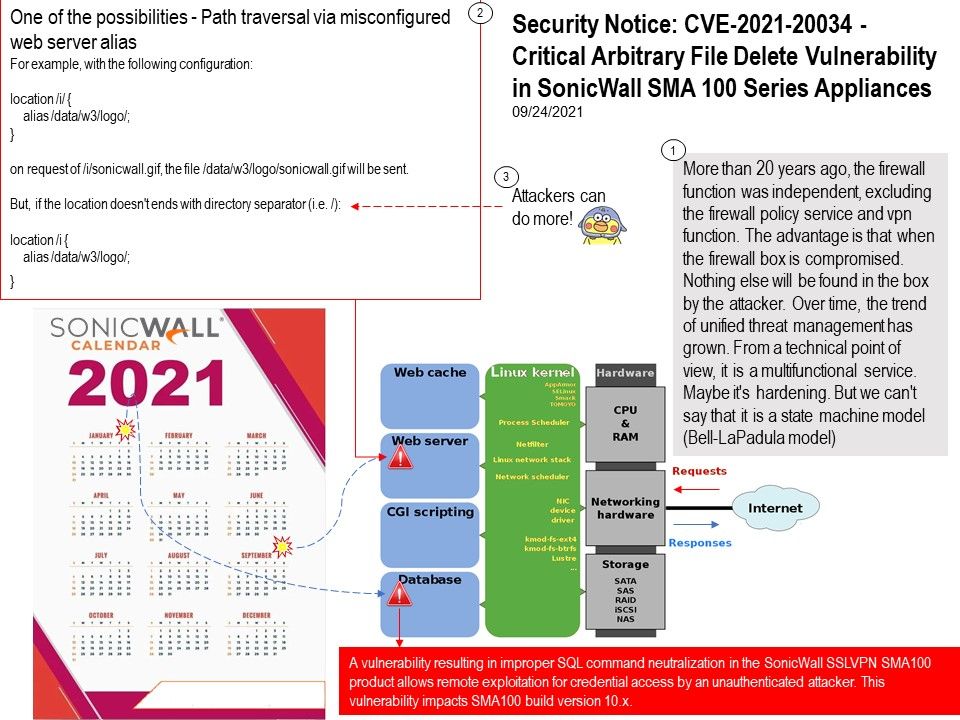
Multiple vulnerabilities have occurred. The focus area of this topic will focus on CVE-2021-40988 (path traversal). From a technical point of view, once this type of vulnerability persists. It will amplify other potential risks. Perhaps our description is one of the possibilities. The goal is to provide you with tips for consideration.
Images are loaded via some HTML, the loadImage URL takes a filename parameter and returns the contents of the specified file. The image files themselves are stored on disk. Thus, attacker allow the application reads from the web page reachable file path. If the web application has path traversal vulnerability encounters, so an attacker can request additional path to retrieve an arbitrary file from the server’s filesystem. See the attached drawings for details.
Official announcement: ClearPass Policy Manager Multiple Vulnerabilities – https://www.arubanetworks.com/assets/alert/ARUBA-PSA-2021-018.txt
.jpg)
.jpg)
.jpg)