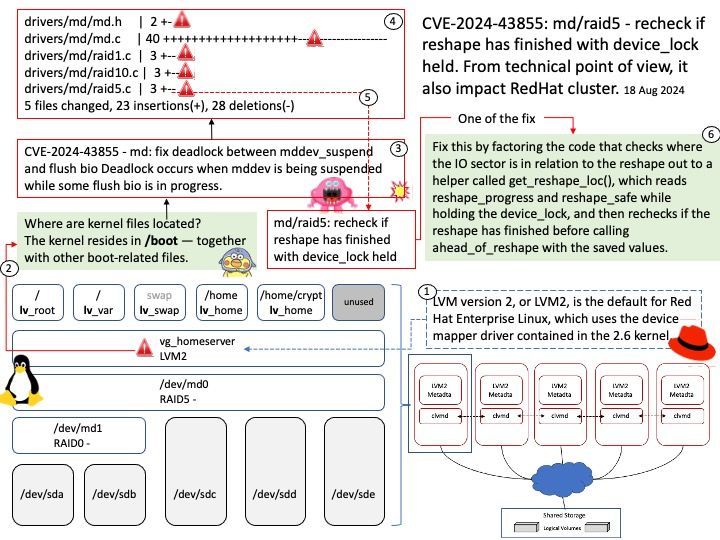
Preface: LVM version 2, or LVM2, is the default for Red Hat Enterprise Linux, which uses the device mapper driver contained in the 2.6 kernel. LVM2, which is almost completely compatible with the earlier LVM1 version, can be upgraded from versions of Red Hat Enterprise Linux running the 2.4 kernel.
The Clustered Logical Volume Manager (CLVM) is a set of clustering extensions to LVM. These extensions allow a cluster of computers to manage shared storage (for example, on a SAN) using LVM.
Background: In the Mutex concept, when the thread is trying to lock or acquire the Mutex which is not available then that thread will go to sleep until that Mutex is available. Whereas in Spinlock it is different. The spinlock is a very simple single-holder lock. If a process attempts to acquire a spinlock and it is unavailable, the process will keep trying (spinning) until it can acquire the lock. This simplicity creates a small and fast lock.
Vulnerability details: Deadlock occurs when mddev is being suspended while some flush bio is in progress. It is a complex issue.
T1. the first flush is at the ending stage, it clears ‘mddev->flush_bio’ and tries to submit data, but is blocked because mddev is suspended by T4.
T2. the second flush sets ‘mddev->flush_bio’, and attempts to queue md_submit_flush_data(), which is already running (T1) and won’t execute again if on the same CPU as T1.
T3. the third flush inc active_io and tries to flush, but is blocked because ‘mddev->flush_bio’ is not NULL (set by T2).
T4. mddev_suspend() is called and waits for active_io dec to 0 which is inc by T3.
The root issue is non-atomic inc/dec of active_io during flush process.
Official announcement: For details, please refer to link –