Preface: Software Development Life Cycle is the application of standard business practices to building software applications. It’s typically divided into six to eight steps: Planning, Requirements, Design, Build, Document, Test, Deploy, Maintain.
Background: The SAP NetWeaver development infrastructure combines the features and advantages of a local development environment (usually provided in a Java environment) and a server-based development environment, which can provide development teams with a consistent development environment and support software throughout its life cycle Development.
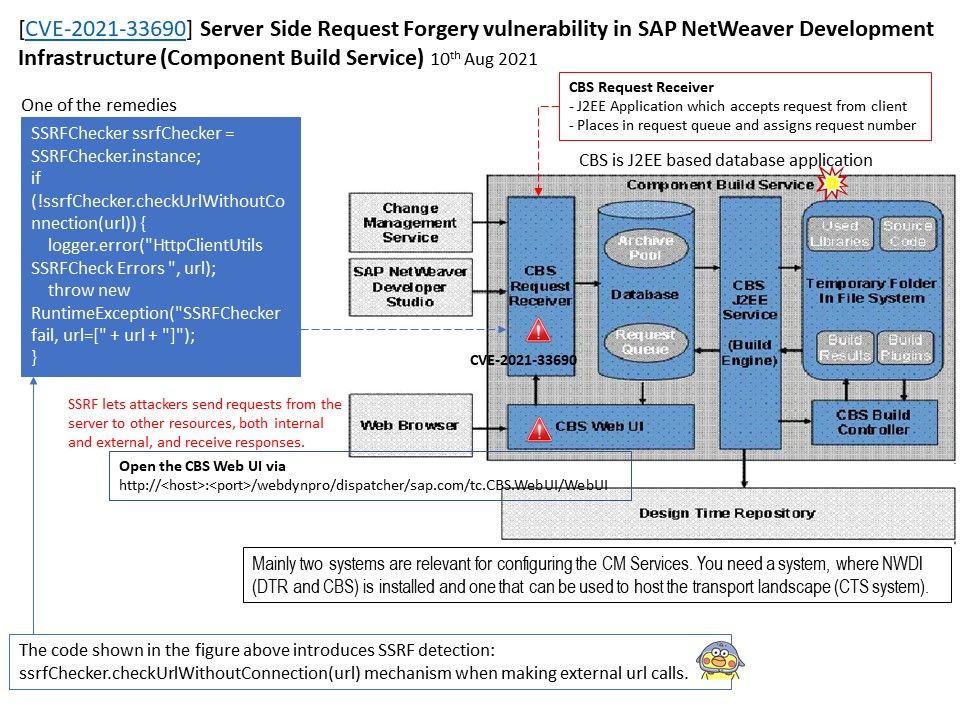
Component Build Service (CBS): Central build of the source files in the DTR based on the component model.
Vulnerability details: CVE-2021-33690 – Server Side Request Forgery vulnerability in SAP NetWeaver Development Infrastructure (Component Build Service)
Affected Products – SAP NetWeaver Development Infrastructure (Component Build Service), Versions – 7.11, 7.20, 7.30, 7.31, 7.40, 7.50.
Description: SSRF lets attackers send requests from the server to other resources, both internal and external, and receive responses.
Reference: If you are interested in knowing my understanding of this matter. Please refer to the picture above. The official details can be found in the link – https://wiki.scn.sap.com/wiki/pages/viewpage.action?pageId=582222806