DNS logs explicitly shown the internet user activities. For instance a malicious network traffic that can be identified in DNS logs. The technical details includes command and control (C2) traffic of the following cyber attacks.
Ransomware, malicious ads and redirects, exploit kits, phishing, typosquatting attacks, DNS hijacking; denial of service (DoS) attacks; and DNS tunneling.
Pi-hole is a Linux network-level advertisement and internet tracker blocking application which acts as a DNS sinkhole. DNS Sinkholing is a mechanism aimed at protecting users by intercepting DNS request attempting to connect to known malicious or unwanted domains and returning a false, or rather controlled IP address. The controlled IP address points to a sinkhole server defined by the DNS sinkhole administrator.
The Sinkhole server can be used to collect event logs, but in such cases the Sinkhole administrator must ensure that all logging is done within their legal boundaries and that there is no breach of privacy.
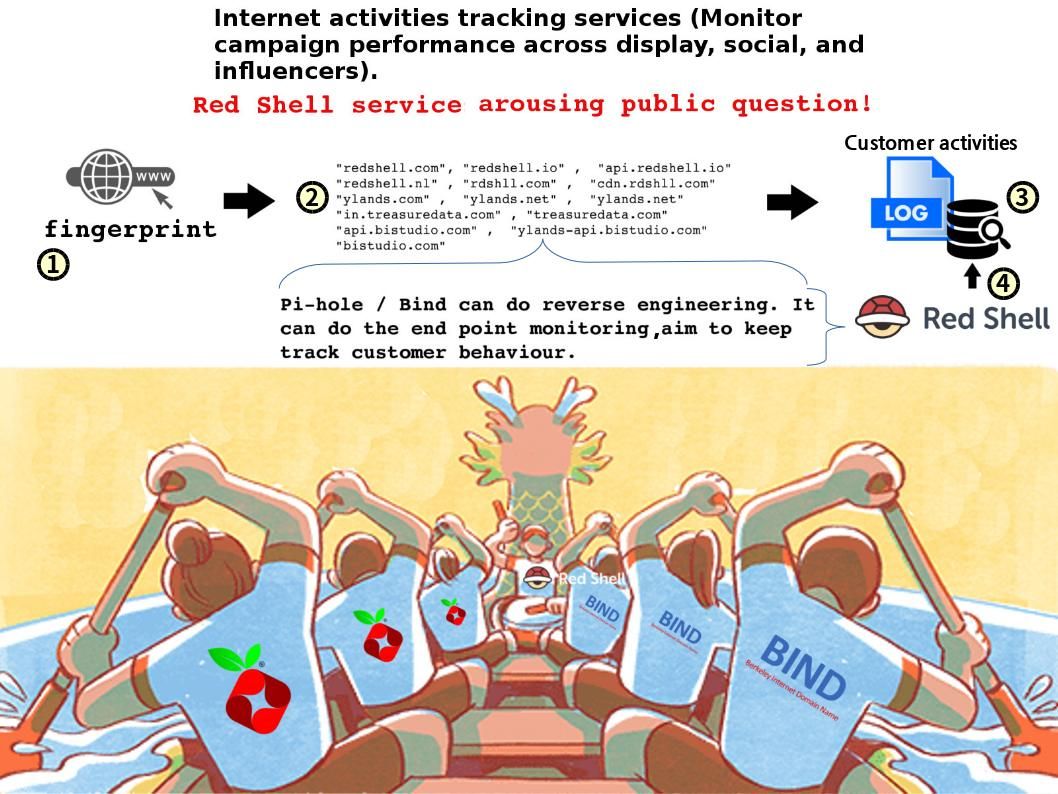
Red Shell helps PC & console games uncover where their players
come from through reliable attribution. Their system architecture build by PI-HOLE and bind opensourece application. Meanwhile PI-HOLE and BIND can do reverse engineering. It can do the end point monitoring, aim to keep track the customer behaviour.
A concerns of public and question the analytics package provided by Innervate, Inc., to game publishers.
Innervate, a Seattle-based company founded to help game makers reach more customers, is launching its new Red Shell service today.
Reference:
European Union Agency for Network and Information Security
What is a “DNS Sinkhole”? – https://www.enisa.europa.eu/topics/csirts-in-europe/glossary/dns-sinkhole
Remark: Administrator must ensure that all logging is done within their legal boundaries and that there is no breach of privacy.
With thanks! Valuable information!
With thanks! Valuable information!
good stuff. I will make sure to bookmark your blog.
Hello. impressive job. I did not anticipate this.
good stuff. I will make sure to bookmark your blog.
sound like you know what you?re talking about! Thanks
good stuff. I will make sure to bookmark your blog.
I got what you mean,saved to fav, very decent site.
good stuff. I will make sure to bookmark your blog.
With thanks! Valuable information!
With thanks! Valuable information!