Preface: IoT Enterprise runs on 32-bit and 64-bit x86 chipsets with support for Universal Windows Platform (UWP) apps as well as Classic Windows(e.g. Win32 and .NET) applications. Perhaps you will discover plenty of medical devices still use 32 bit windows application.
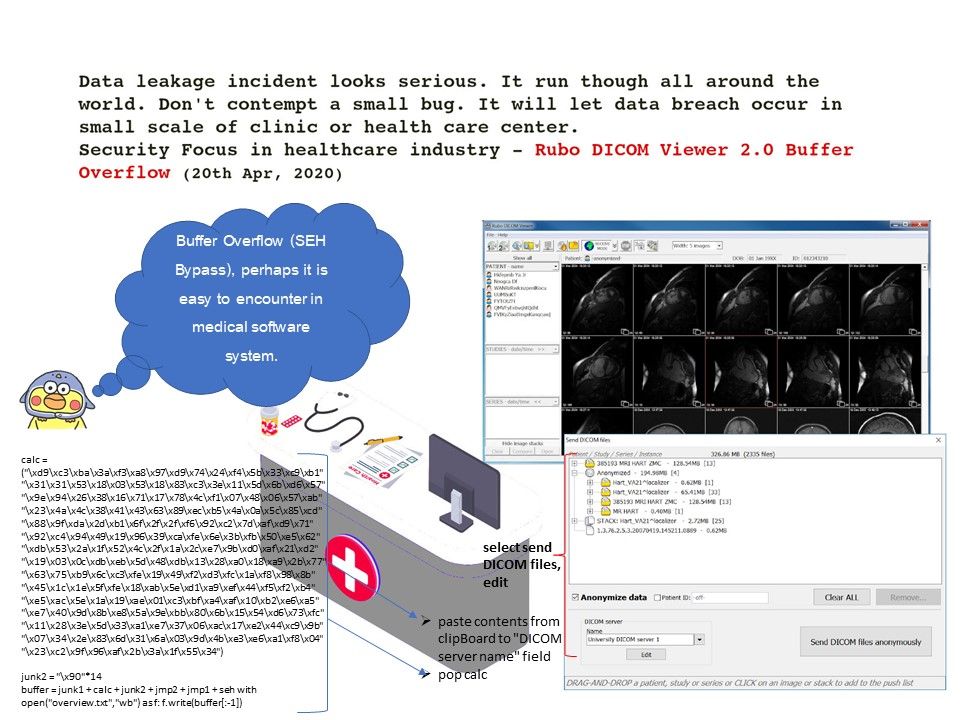
Recent security alert on medical product: The ‘DICOM Viewer 2.0’ capable of handling all DICOM files of any modality (X-Ray angiogram, ultrasound, CT, MRI, Nuclear, waveform etc.), compression (lossless and lossy Jpeg, Jpeg200, RLE), depth or color. The proof of concept shown that software encountered buffer overflow (SEH) in specify circumstances.
What is Buffer overflow (SEH): An exception handler is a portion of code contained within an application, designed to handle an exception that may occur during runtime. Windows contains an exception handler by default (SEH) which is designed to catch an exception and generate an error. If the buffer is overflown and data is written to the SEH (located eight bytes after ESP), then all of the CPU registers are set to zero (0) and this prevents us from executing our shellcode successfully. If attacker can removing the eight additional bytes from the stack, and returning execution to the top of the stack, thus allowing execution of the shellcode.
Status: Waiting for official information update.
Reference: https://www.rubomedical.com/