Botnet from earlier phase relies on workstations engage the attack convert to smartphones in last few years. Most likely the security enhancement in workstations and smartphones improved. The threat actors found the new victims today.It is a low-end wireless router.
So below items are the guidance:
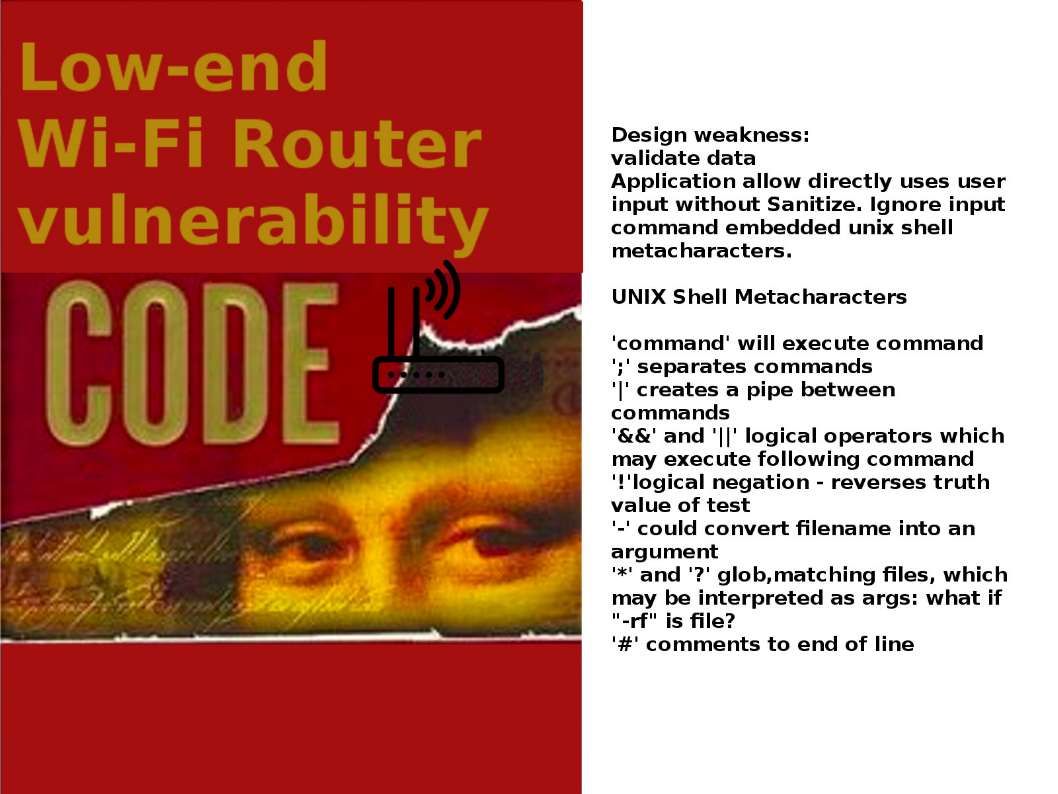
- Never trust input
- Prefer rejecting data to filtering data
- Every component should validate data
Whereby the way to validate the input are:
- Indirect selection – application never directly uses user input
- Whitelist
- Blacklist
If required input, do the validation actions:
- Sanitize – Attempt to fix input by removing dangerous parts
- Refuse to use invalid input
- Record invalid input in log file
- Alert – send notification to related personnel
The devices which could be affected by new malware (vpnfilter). Below is the checklist for reference.
LINKSYS DEVICES:
E1200
E2500
WRVS4400N
MIKROTIK ROUTEROS VERSIONS FOR CLOUD CORE ROUTERS:
1016
1036
1072
NETGEAR DEVICES:
DGN2200
R6400
R7000
R8000
WNR1000
WNR2000
TP-LINK DEVICES:
R600VPN
Special Item: QNAP DEVICES (Network-attached storage)
TS251
TS439 Pro
Other QNAP NAS devices running QTS software