Preface: Xen is an open-source hypervisor that allows the simultaneous development, execution, and management of multiple virtual machines on one physical computer. Xen offers two types of virtualization: paravirtualization and full virtualization.
Background: XenServer is a Citrix product the company acquired from XenSource in 2007. Citrix’s XenServer provides 7 Network interface cards and 16 virtual disks.
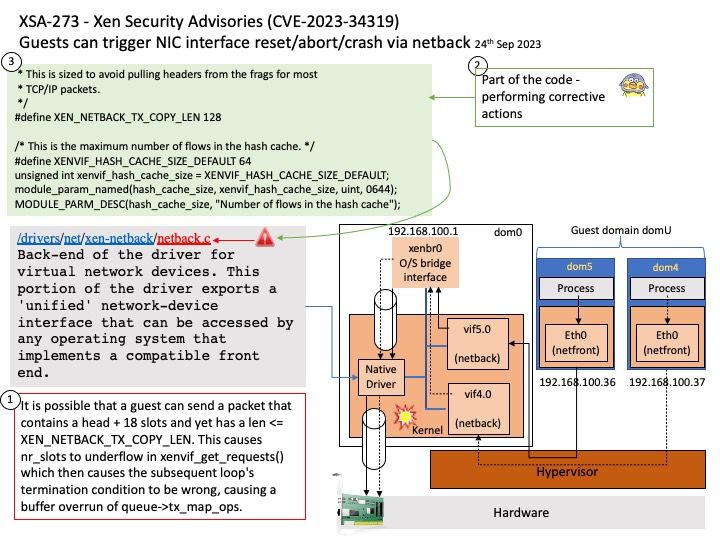
The network I/O virtualization architecture in Xen can be a significant source of overhead for networking performance in guest domains. Xen provides each guest domain with a number of virtual network interfaces, which is used by the guest domain for all its network communications. Corresponding to each virtual interface in a guest domain, a `backend’ interface is created in the driver domain, which acts as the proxy for that virtual interface in the driver domain. All the backend interfaces in the driver domain (corresponding to the virtual interfaces) are connected to the physical NIC and to each other through a virtual network bridge.
Vulnerability details: The fix for XSA-423 added logic to Linux’es netback driver to deal with a frontend splitting a packet in a way such that not all of the headers would come in one piece. Unfortunately the logic introduced there didn’t account for the extreme case of the entire packet being split into as many pieces as permitted by the protocol, yet still being smaller than the area that’s specially dealt with to keep all (possible) headers together. Such an unusual packet would therefore trigger a buffer overrun in the driver.
Official announcement: For details, please refer to the link – https://xenbits.xenproject.org/xsa/advisory-423.html