Preface: Ray Tomlinson sent the first email across a network, initiating the use of the “@” sign to separate the names of the user and the user’s machine in 1971, when he sent a message from one DEC-10 computer to another DEC-10.
Synopsis: An SMTP relay is a protocol that allows email to be transmitted through the internet. OpenSMTPD design goals include security, reliability & easy of configuration. If you are OpenBSD ( open-source Unix-like operating system ) user, you can setup OpenSMTPD to relay local emails to Gmail.
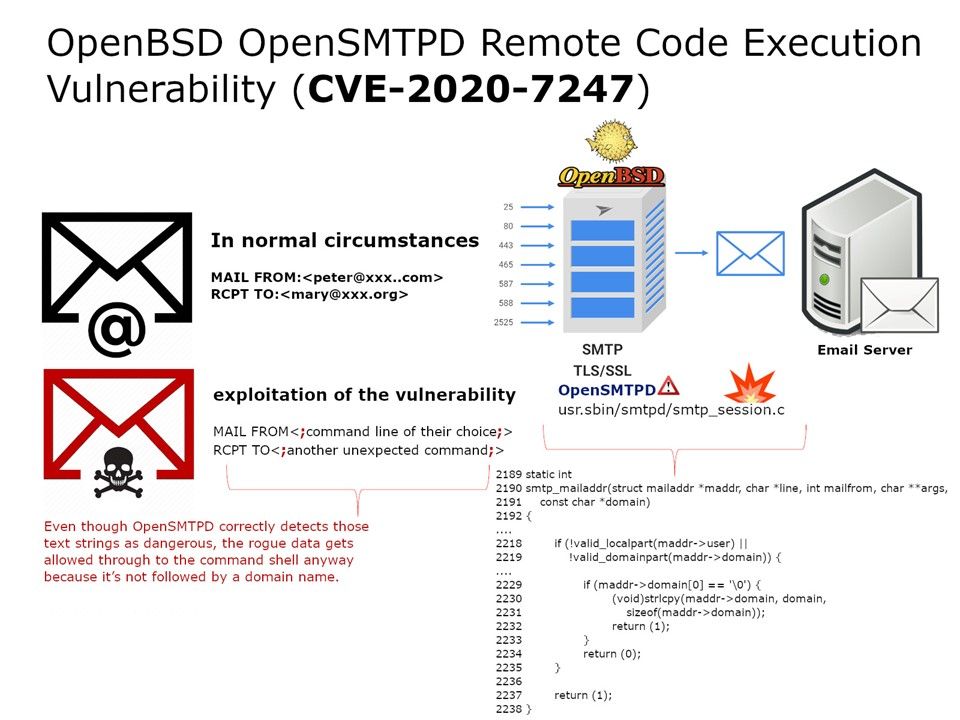
Vulnerability details: So called the code blew a hole in relay server.
Privileges escalation: When mail is received by server, it uses the root (superuser account) to deal with it. And therefore anyone who’s can exploit this vulnerability. It similar to “promote” themselves to root.
This vulnerability exists in OpenBSD’s mail server OpenSMTPD’s “smtp_mailaddr()” function, and affects OpenBSD version 6.6. This allows an attacker to execute arbitrary shell commands like “sleep 66” as root user.
Remedy: To remediate this vulnerability, affected OpenBSD users are recommended to install patches for OpenBSD 6.6. See reference 019 in https://www.openbsd.org/errata66.html.