Background: You can refer to Amazon’s Creating an IAM User in Your AWS Account page to create this IAM user. Once this is done, you can add new credentials of type Aws Credentials (specifying your Access key ID and a Secret access key).Whereby it can store Amazon IAM access keys (AWSAccessKeyId and AWSSecretKey) within the Jenkins Credentials.
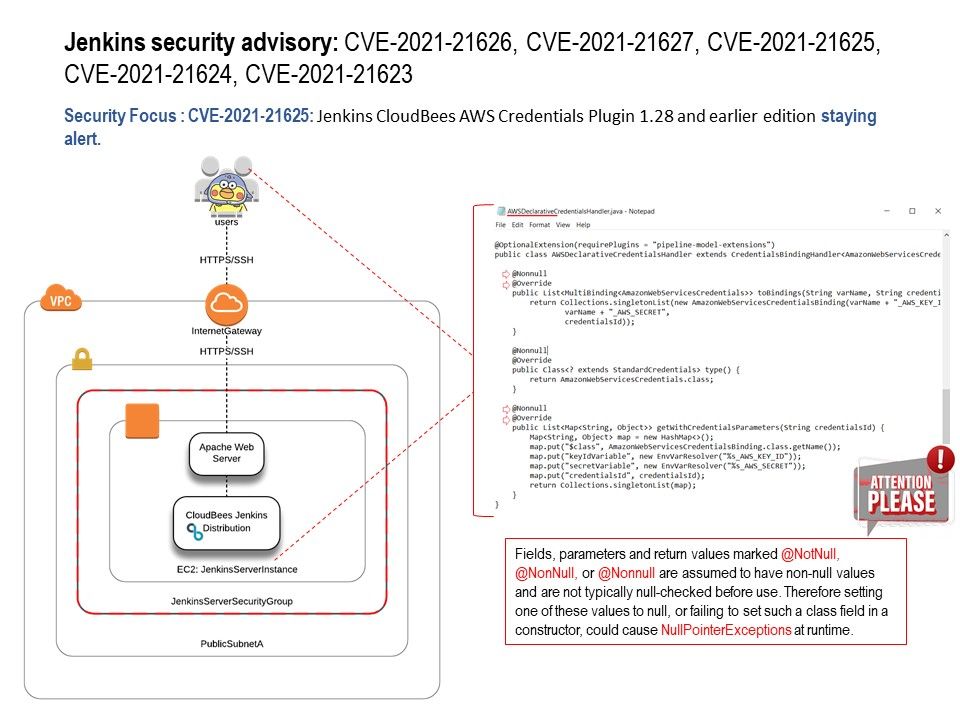
Vulnerability details: Jenkins CloudBees AWS Credentials Plugin 1.28 and earlier does not perform a permission check in a helper method for HTTP endpoints, allowing attackers with Overall/Read permission to enumerate credentials IDs of AWS credentials stored in Jenkins in some circumstances.
One of the possible reasons: In Java, the java. lang. NullPointerException is thrown when a reference variable is accessed (or de-referenced) and is not pointing to any object. This error can be resolved by using a try-catch block or an if-else condition to check if a reference variable is null before dereferencing it.
Impact: the attacker might be able to use the resulting exception to bypass security logic.
Official announcement – https://www.jenkins.io/security/advisory/2021-03-18/#SECURITY-2032