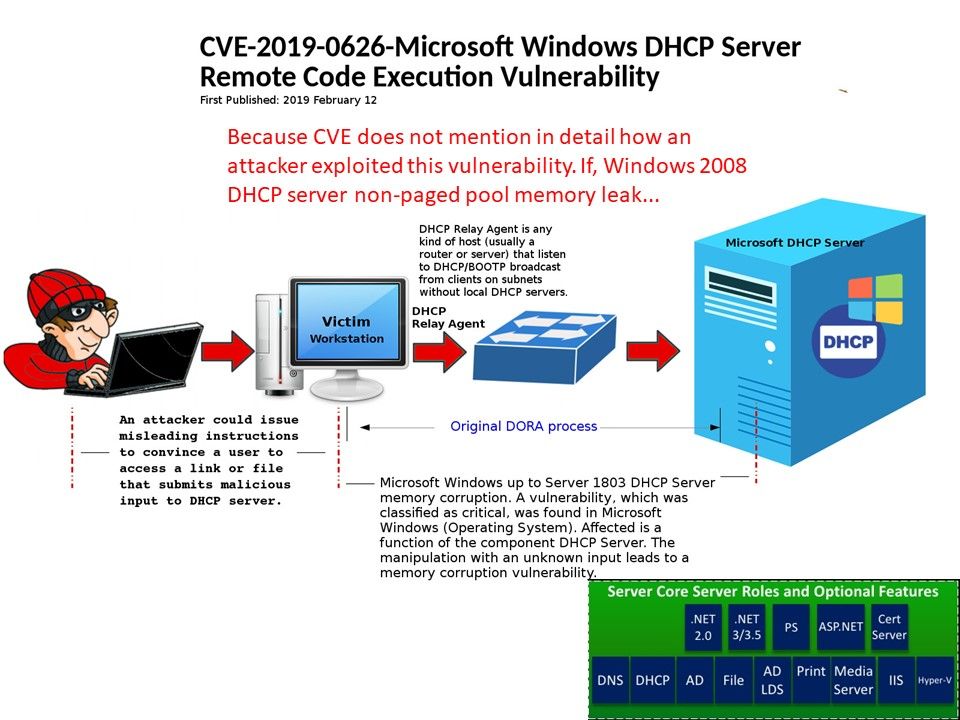
Preface: This vulnerability is included in MS Patch Tue this week. However the vulnerability is more critical than others. Since threat actor can be conduct a remote code execution through social engineering.
Technical highlight: The official announcement told that attacker could exploit the vulnerability by sending a DHCP packet that submits malicious input to the affected software because a design weakness occurs in software (DHCP server) which has a flaw of handles objects in memory. A successful exploit could allow the attacker to execute arbitrary code and compromise the system completely.
My observation: We did not found additional details of this vulnerability. My speculation is that whether windows 2008 DHCP server has non page memory leak flaw which causes this problem. What do you think?
Official remediation: CVE-2019-0626 | Windows DHCP Server Remote Code Execution Vulnerability
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0626
Greate article. Keep writing such kind of info on your page. Im really impressed by it.