Preface: An attacker with normal access to a virtual machine may exploit this issue by placing a malicious file renamed as `openssl[.]cnf’ in an unrestricted directory which would allow code to be executed with elevated privileges,” VMware said.
Background:
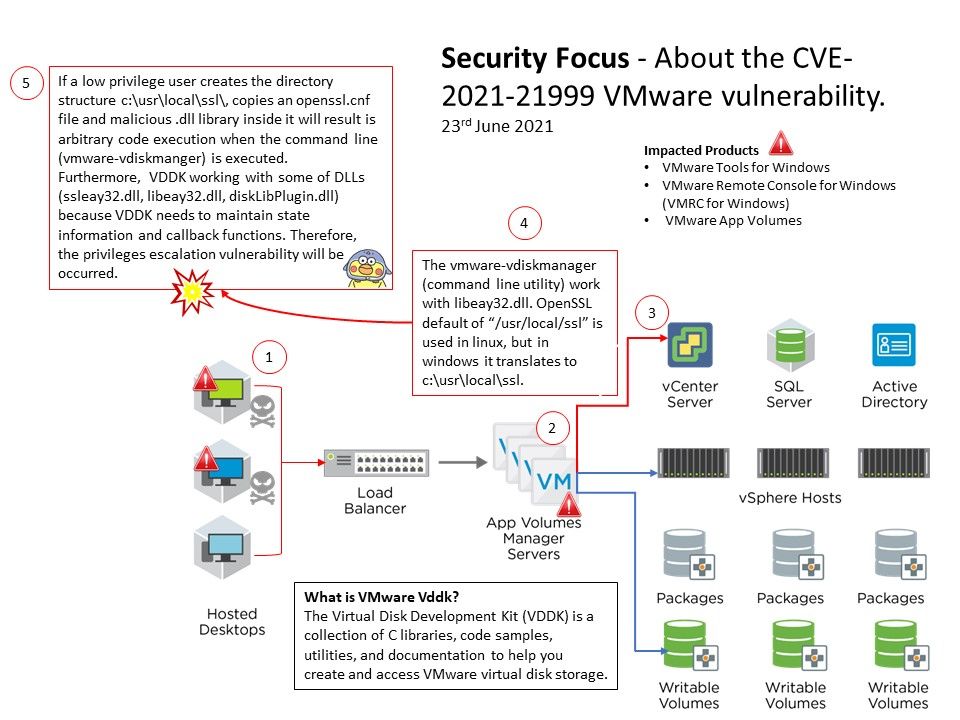
VMware App Volumes provides a system to deliver applications to desktops through virtual disks. Installing App Volumes involves installing the App Volumes Manager, App Volumes agents, and related components.
The installers for VMware Tools for Windows is built into VMware Workstation as ISO image files. The new features of VMware Tools for Windows (11.2.6) including OpenSSL version has been updated to 1.1.1k.
VMware Remote Console Open-source components have been updated, including jansson 2.10, libjpeg-turbo 2.0.5, libgksu 2.0.13, openssl 1.1.1h, pcre 8.44, sqlite 3.23.3, and rsvg 2.40.21.
Vulnerability details: VMware Tools for Windows (11.x.y prior to 11.2.6), VMware Remote Console for Windows (12.x prior to 12.0.1) , VMware App Volumes (2.x prior to 2.18.10 and 4 prior to 2103) contain a local privilege escalation vulnerability.
One of the possibilities: The vmware-vdiskmanager (command line utility) work with libeay32.dll[.] OpenSSL default of “[/]usr[/]local[/]ssl” is used in linux, but in windows it translates to c:[\]usr[\]local[\]ssl.
If a low privilege user creates the directory structure c:[\]usr[\]local[\]ssl[\], copies an openssl.cnf file and malicious .dll library inside it will result is arbitrary code execution when the command line (vmware-vdiskmanger) is executed. Furthermore, VDDK working with some of DLLs (ssleay32.dll, libeay32.dll, diskLibPlugin.dll) because VDDK needs to maintain state information and callback functions. Therefore, the privileges escalation vulnerability will be occurred.
Official announcement (CVE-2021-21999) – https://www.vmware.com/security/advisories/VMSA-2021-0013.html
Ref: There is another vulnerability on other products. VMware Carbon Black App Control update address authentication bypass (CVE-2021-21998) – https://www.vmware.com/security/advisories/VMSA-2021-0012.html