As usual, because of vendor decision, vendor not going to release the details of design weakness. From my opinion that understand the details will be enhanced your system and infrastructure defense mechanism. Below is my personal comment according to this specifics vulnerability.
Vulnerability details: CVE-2021-21481 – The MigrationService, which is part of SAP NetWeaver, does not perform an authorization check allowing an unauthorized attacker to access configuration objects, including such that grant administrative privileges.
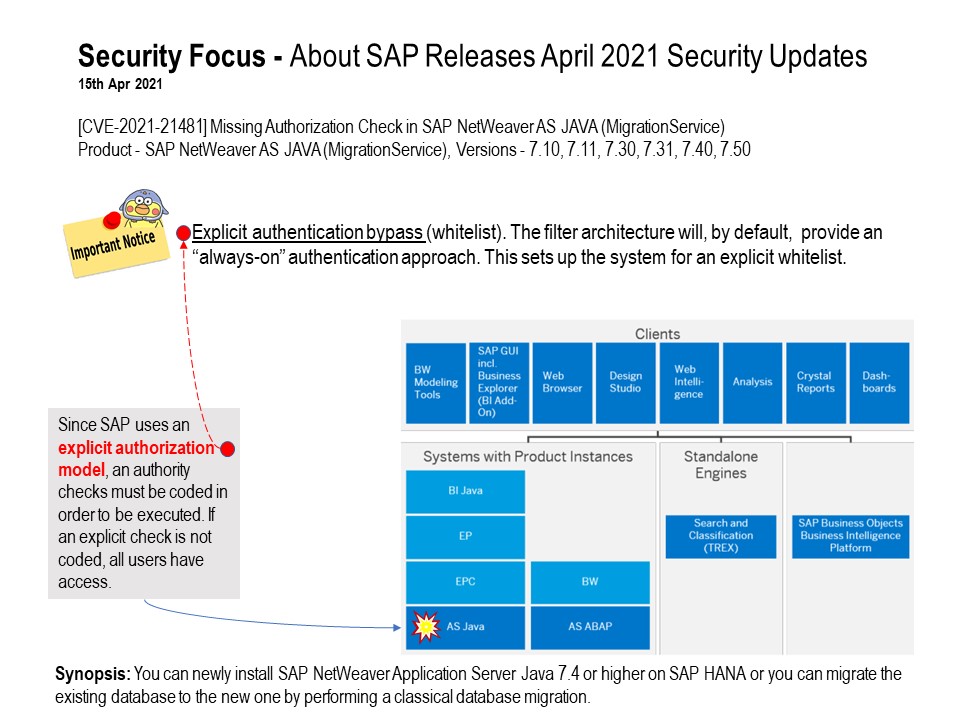
Since SAP uses an explicit authorization model, an authority checks must be coded in order to be executed. If an explicit check is not coded, all users have access.
Reference: Explicit authentication bypass (whitelist). The filter architecture will, by default, provide an “always-on” authentication approach. This sets up the system for an explicit whitelist.
Impact: Since the failure is related to incorrect authorization, the risk will depend on the environment.
Official announcement: Please refer to link – https://wiki.scn.sap.com/wiki/pages/viewpage.action?pageId=573801649