Preface: The Department of Homeland Security (DHS) and FDA are aware that the (URGENT/11) vulnerabilities will be effected medical device and hospital networks. They released announcement to urge specify industry to staying alert.
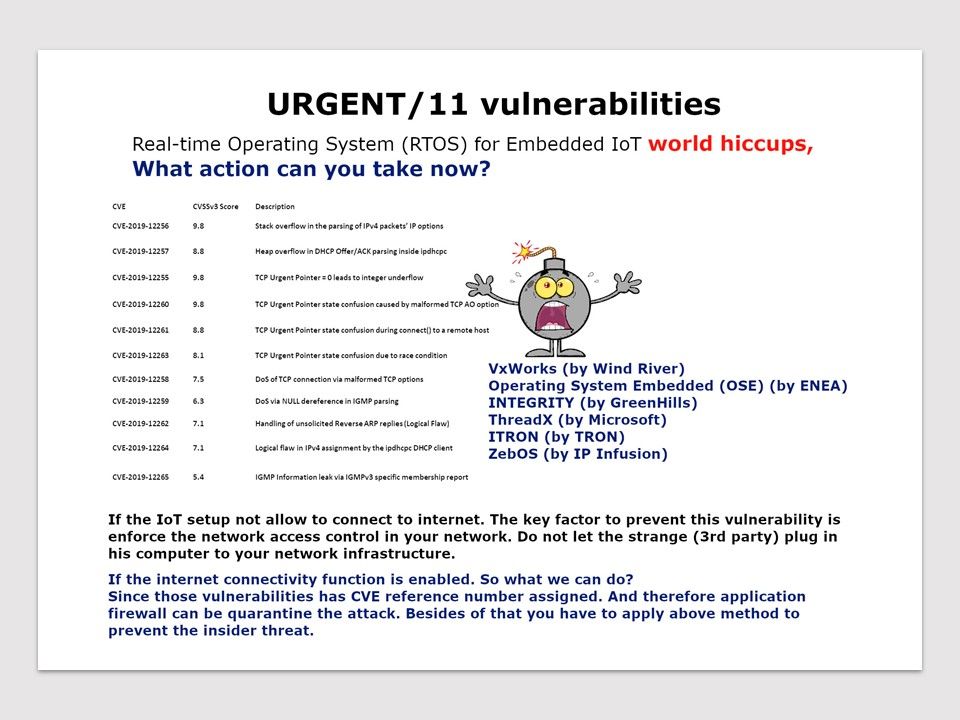
Vulnerability details: So called (URGENT/11) found on Wind River VxWorks on July 2019. Urgent11, it include 6 remote code defects and 5 less serious flaws. The design limitation of TCP/IP (IPnet) network stack let hackers to bypass traditional border and device security. If your IoT settings are integrated with physical LAN and 802.11 (wireless), but the IoT’s does not have internet communication capabilities. Maybe you also have a headache at the moment. See whether below suggestion can help.
- If you do not have SIEM on hand. The primitive interim remediation should do the following.
Turn MAC Filtering on wireless router - Turn on port protection on your network switch. If you are using low end network device which do not provide this function. Perhaps you must disable or use the seal tape to block the ethernet port not in used.
The key factor to prevent this vulnerability is enforce the network access control in your network. Do not let the strange (3rd party) plug in his computer to your network infrastructure.
If the internet connectivity function is enabled. So what we can do?
Since those vulnerabilities has CVE reference number assigned. And therefore application firewall can be quarantine the attack. Besides of that you have to apply above method to prevent the insider threat.
Reference: FDA announcement – https://www.fda.gov/news-events/press-announcements/fda-informs-patients-providers-and-manufacturers-about-potential-cybersecurity-vulnerabilities