Background: sudo command allows you to run programs with the security privileges of another user. All auditors and security expert highly recommend to use. We can say it is a best practices.
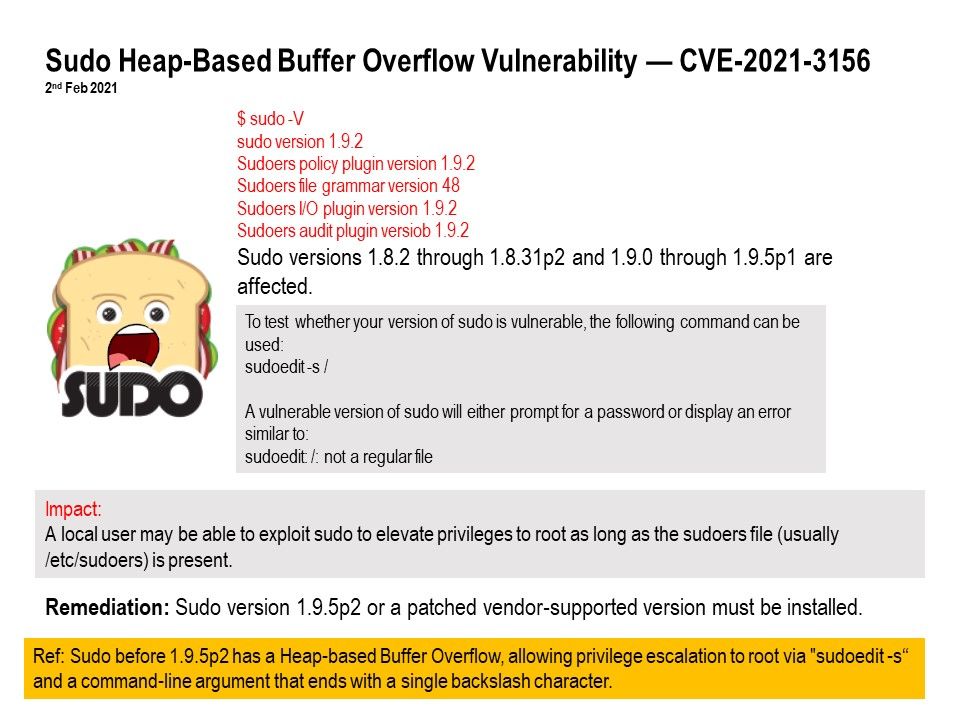
Vulnerability details: Sudo before 1.9.5p2 has a Heap-based Buffer Overflow, allowing privilege escalation to root via “sudoedit -s”
and a command-line argument that ends with a single backslash character.
Impact: Taking control of the Linux system vulnerability version: before 1.9.5p2
Workaround: No
Fix: The bug is fixed in sudo 1.9.5p2.
Immediate action: You should patch immediately.
Security concern: Since system admin will deny to use SSH remotely without VPN connectivity because of security reason.
Therefore this design weakness will be exploit by insider threats. If you cannot patch immediately. You should fine tune your SIEM to monitoring sudo usage.