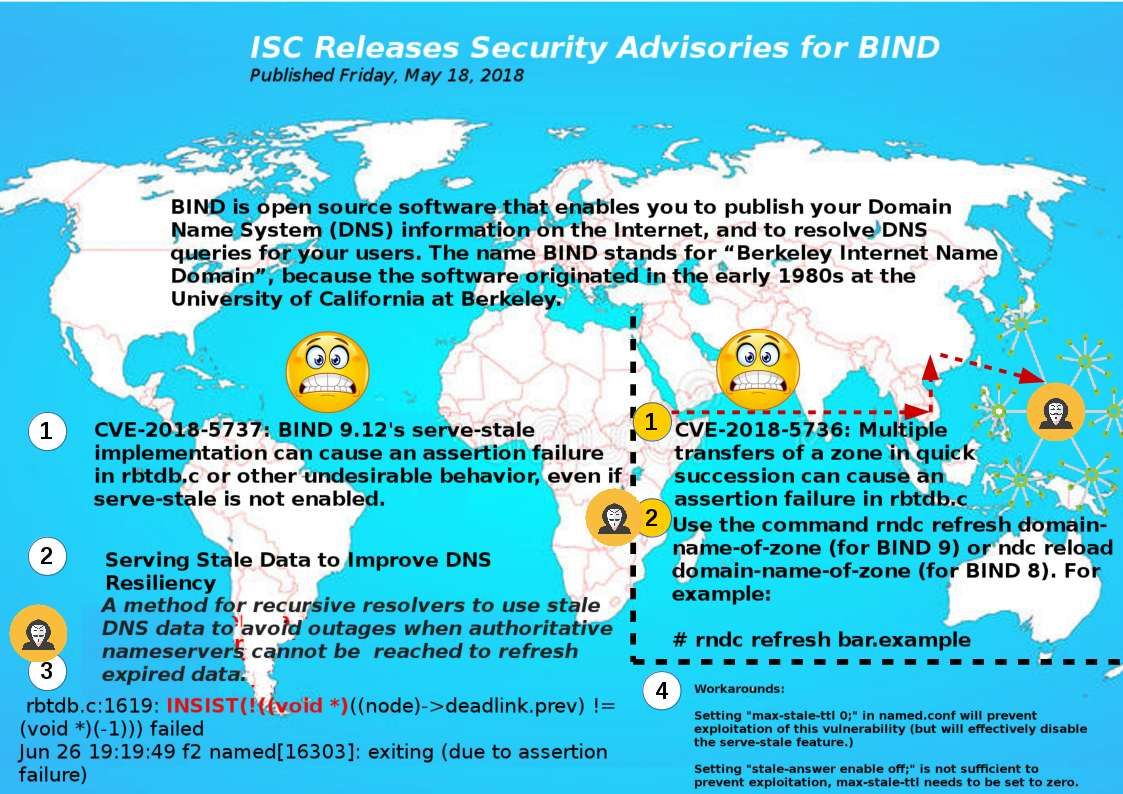
ISC Releases Security Advisories for BIND on May 18, 2018. This alert awaken my defense thinking. I was written few articles about the electronic war and the cyber arsenal. But forgot to contains a scenario which annoucned by ISC today (Security Advisories for BIND). Regarding to to the subject (ISC Releases Security Advisories for BIND) indeed described a hacking scenario who focus to doing bad things to the world (distrubuted deniel of services to worldwide DNS services). It is not difficult to understand the way. The method is CVE-2018-5737 + CVE-2018-5736.
Such cyber attack on phase 1 is one to many distribution (Initiating a Zone Transfer), then execute vulnerability (CVE-2018-5737) . As a result the smartphone, server and workstation all can’t work because no DNS service will be available! You can find hints in attached diagram. For more details about the vulnerabilities, please refer below url for references.
CVE-2018-5737: BIND 9.12’s serve-stale implementation can cause an assertion failure in rbtdb.c or other undesirable behavior, even if serve-stale is not enabled.
https://kb.isc.org/article/AA-01606/0
CVE-2018-5736: Multiple transfers of a zone in quick succession can cause an assertion failure in rbtdb.c