Preface: REST APIs are stateless. Stateful APIs do not adhere to the REST architectural style.
Background: SOAP is a protocol, and REST is an architectural style. A REST API can actually utilize the SOAP protocol, just like it can use HTTP. The Cisco Fabric Automation REST APIs for third party applications enables you to programmatically control Cisco Fabric Automation. All the REST API operations can also be performed using the DCNM GUI as DCNM uses these REST APIs to render the GUI.
Remark: From Release 10.0(1), by default, the Cisco DCNM supports HTTPS only.
Security Focus: Cisco Data Center Network Manager Authentication Bypass Vulnerabilities
Vulnerability Details:
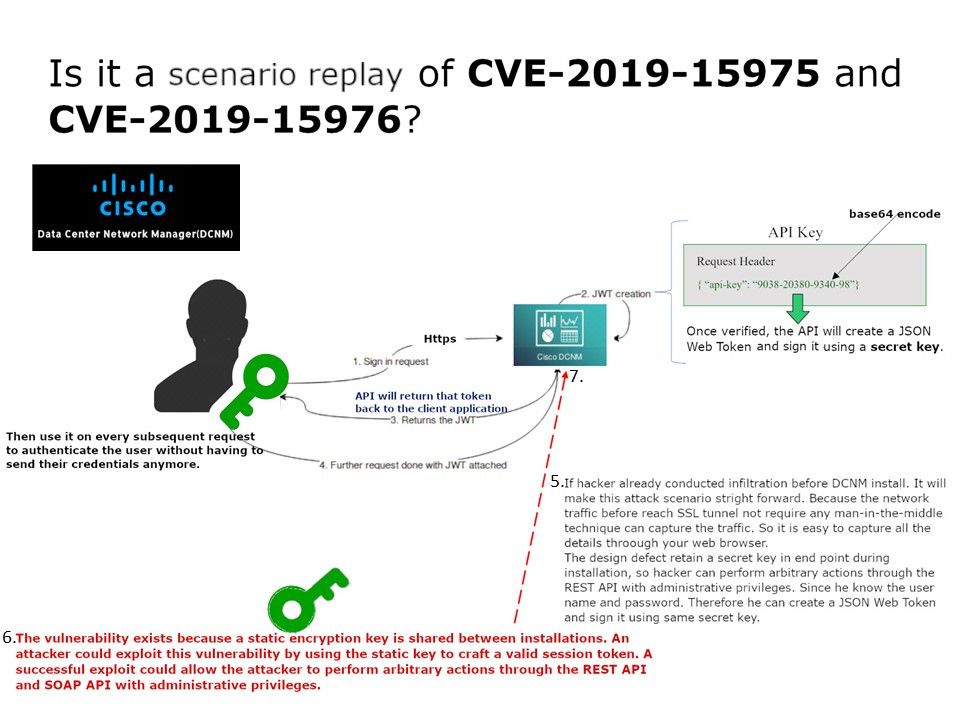
CVE-2019-15975 – Cisco Data Center Network Manager REST API Authentication Bypass Vulnerability
CVE-2019-15976 – Cisco Data Center Network Manager SOAP API Authentication Bypass Vulnerability
If hacker already conducted infiltration to specific workstation before DCNM install. It will make this attack scenario straight forward. Because the network traffic before reach SSL tunnel not require any man-in-the-middle technique can capture the traffic. So it is easy to capture all the details through your web browser.
The design defect retain a secret key in end point during installation, so hacker can perform arbitrary actions through the REST API with administrative privileges. Since he know the user name and password. Therefore he can create a JSON Web Token and sign it using same secret key. Should you be interested, please read the details of attached diagram.
Cisco official announcement – https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20200102-dcnm-auth-bypass