Preface: Some people say that CGI-Bin is a historical site. Today’s onerous security environment, perhaps not people use it. The truth tell us is that CGI-Bin still have space for survival.
Background: About two months ago, the proof of concept for CVE-2021-41773 (Apache 2.4.49 & 2.4.50) vulnerability was released. The remedy solution is modify the configuration of Apache server httpd[.]conf file. As a matter of fact, Apache server has multifunciton, high capability feature. Therefore if software developer and web master do some mistake in this file. It will expand the problem if it has vulnerability occurs.
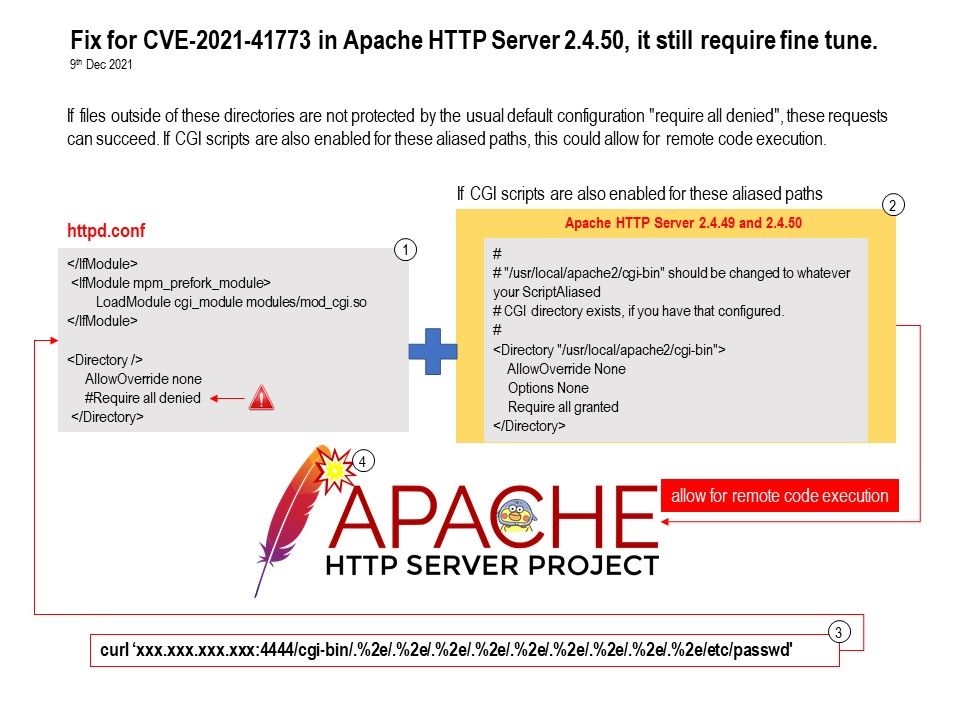
Vulnerability details (CVE-2021-42013): Found that remedy for CVE-2021-41773 in Apache HTTP Server 2.4.50 was insufficient. An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives.
If files outside of these directories are not protected by the usual default configuration “require all denied”, these requests can succeed. If CGI scripts are also enabled for these aliased paths, this could allow for remote code execution.
Reference: In addition to the above-mentioned vulnerabilities, the supplier also discovered new vulnerabilities. For more details, please refer to the link – https://httpd.apache.org/security/vulnerabilities_24.html#2.4.49