Preface: Perhaps we still remember a denial of service tool so called slow http attack. It can easily to make a Apache server out of resources less than minute. UTM firewall contains many components. For example, SSL VPN gateway. From technical point of veiw, this module also similar a HTTPS web server. If it contain application filter function, it will be included regular expression function installed.
Background: While analyzing traffic, FortiWeb’s HTTP parser must extract and buffer each part in the request or response. The buffer allows FortiWeb to scan and/or rewrite it before deciding to block or forward the finished traffic.
Buffers are not infinite due to the physical limitations inherent in all RAM, they are allocated a maximum size. If the part of the request or
response is too large to fit the buffer, FortiWeb must either pass or block the traffic without further analysis of that part.
For example, if your web applications require HTTP POST requests with unusually large parameters, you would adjust the HTTP body buffer size. For details, see http-cachesize in the FortiWeb CLI Reference.
Vulnerability details: An uncontrolled resource consumption vulnerability [CWE-400] in FortiWeb may allow an unauthenticated attacker to cause a Denial of Service to the FortiWeb’s HTTP daemon via sending a large amount of crafted HTTP requests.
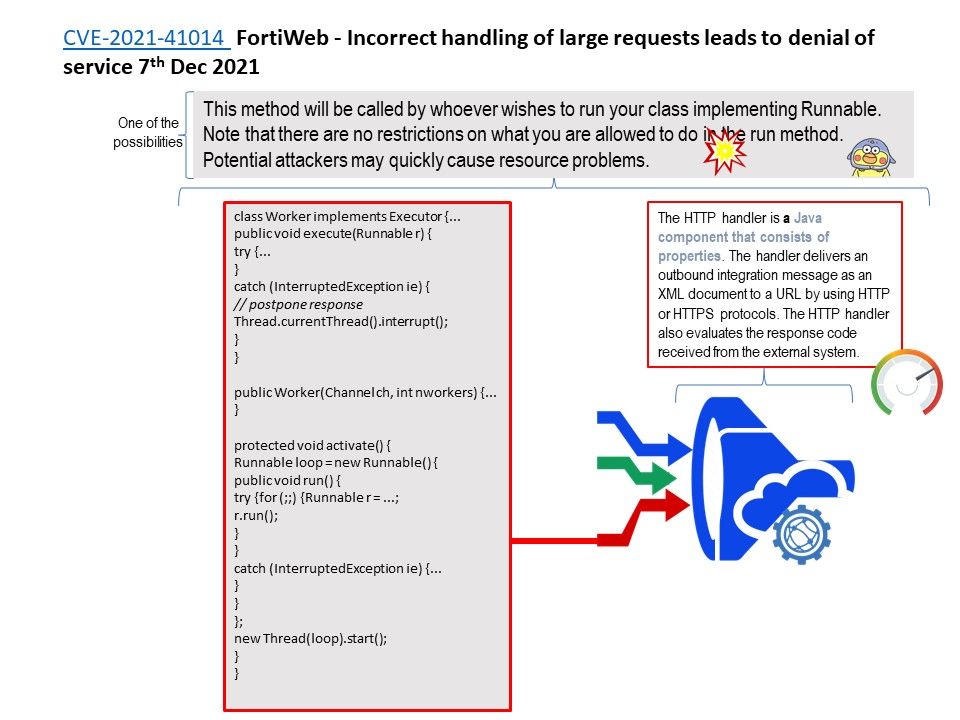
My observation: If this design weakness given by http handler. Think it over, HTTP handler is a Java component that consists of properties. The handler delivers an outbound integration message as an XML document to a URL by using HTTP or HTTPS protocols. The HTTP handler also evaluates the response code received from the external system. If this is the exact vulnerable component. Maybe one of the possibilities looks like scenario shown on attached diagram.
Official details: Please refer to the link – https://www.fortiguard.com/psirt/FG-IR-21-131