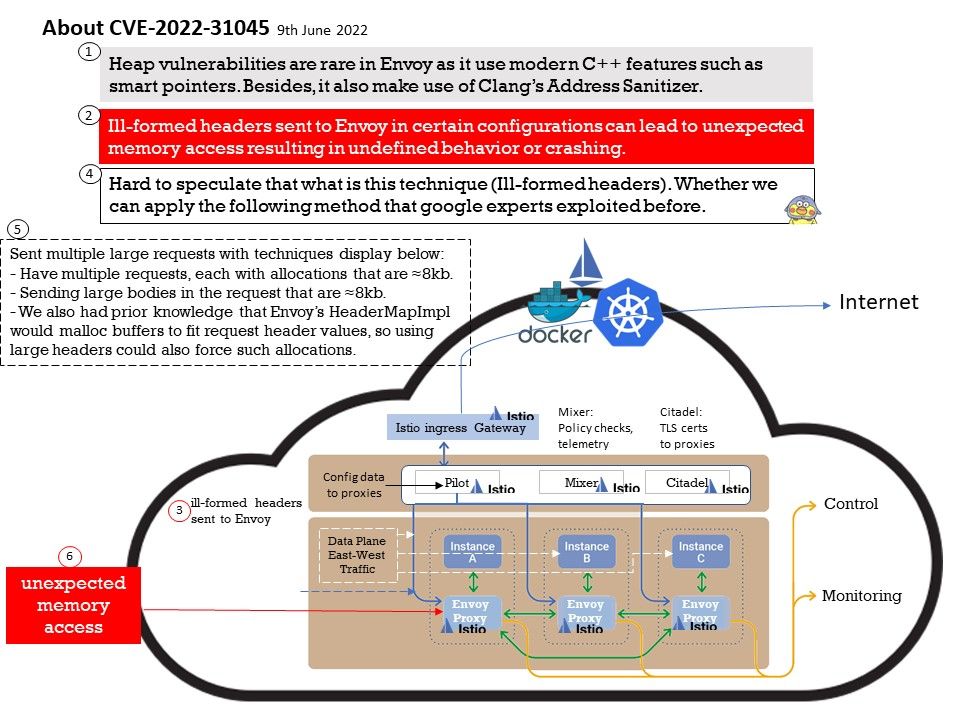
Preface: Hard to speculate that what is this technique (Ill-formed headers). Whether we can apply the following method that google experts exploited before.
Background: Istio enables organizations to secure, connect, and monitor microservices, so they can modernize their enterprise apps more swiftly and securely. Istio manages traffic flows between services, enforces access policies, and aggregates telemetry data, all without requiring changes to application code.
How a service mesh works?
Web services typically exchange data directly through APIs.
A service mesh architecture layer decouples communications from the application logic and uses a proxy or sidecar to manage communication between services and control plane.
Vulnerability details: Ill-formed headers sent to Envoy in certain configurations can lead to unexpected memory access resulting in undefined behavior or crashing.
Reference: Hard to speculate that what is this technique (Ill-formed headers). Whether we can apply the following method that google experts exploited before.
Sent multiple large requests with techniques display below:
- Have multiple requests, each with allocations that are ≈8kb.
- Sending large bodies in the request that are ≈8kb.
- We also had prior knowledge that Envoy’s HeaderMapImpl would malloc buffers to fit request header values, so using large headers could also force such allocations.
Populated with ASCII A (0x41) in the method header and ASCII B (0x42) in the data payload, set a breakpoint on the firing ASSERT and inspected memory contents under gdb.
Remedy: This vulnerability has been resolved in versions 1.12.8, 1.13.5, and 1.14.1.
Workarounds: Users are advised to upgrade. There are no known workarounds for this issue.