Preface: Vulnerability management is included in the security development life cycle. Maybe you’ll be concerned about vulnerabilities. In fact, computer products (software and hardware) are hard to avoid without design flaws. This is the reality.
Background: Fastjson is Alibaba’s open source JSON parsing library, based on the Java language, which supports the conversion between JSON-formatted strings and JavaBeans. It uses an “assumed ordered fast matching” algorithm to maximize the performance of JSON Parse. Furthermore, fastjson is a Java library that can be used to convert Java Objects into their JSON representation. It can also be used to convert a JSON string to an equivalent Java object.
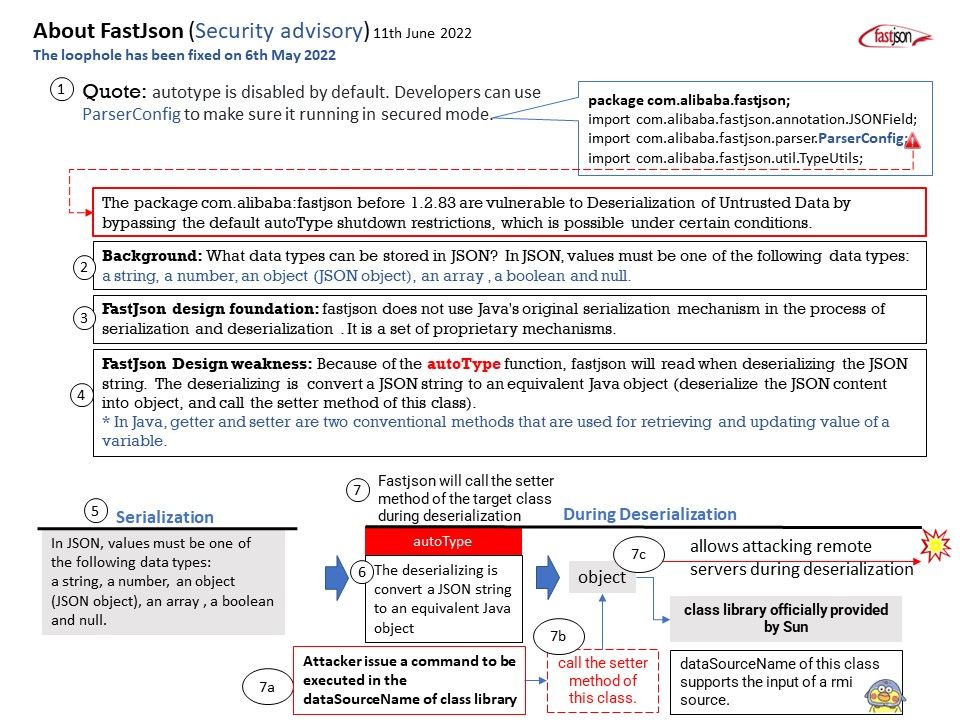
The fastjson does not use Java’s original serialization mechanism in the process of serialization and deserialization . It is a set of proprietary mechanisms.
Because the interface is simple and easy to use, it has been widely used in various application scenarios such as cache serialization, protocol interaction, and web output.
Vulnerability details: The package com.alibaba:fastjson before 1.2.83 are vulnerable to Deserialization of Untrusted Data by bypassing the default autoType shutdown restrictions, which is possible under certain conditions. Exploiting this vulnerability allows attacking remote servers.
Workaround: If upgrading is not possible, you can enable [safeMode] – https://github.com/alibaba/fastjson/wiki/fastjson_safemode
Official announcement: Autotype bug fix, please refer to the link – https://github.com/alibaba/fastjson/commit/8f3410f81cbd437f7c459f8868445d50ad301f15