Preface: If an attacker used our hypothetical race condition above to perform malicious operations and help bypass secured mechanisms, it then becomes “Race Condition Vulnerability.” This vulnerability commonly occurs when threads use the same shared memory to update the values of variables.
Technical background to the file named pipe[.]c: New pipe buffers will be restricted to this size while the user is exceeding their pipe buffer quota. The general pipe use case needs at least two buffers: one for data yet to be read, and one for new data. If this is less than two, then a write to a non-empty pipe may block even if the pipe is not full.
Users can reduce their pipe buffers with F_SETPIPE_SZ below this at their own risk, namely: pipe writes to non-full pipes may block until the pipe is emptied.
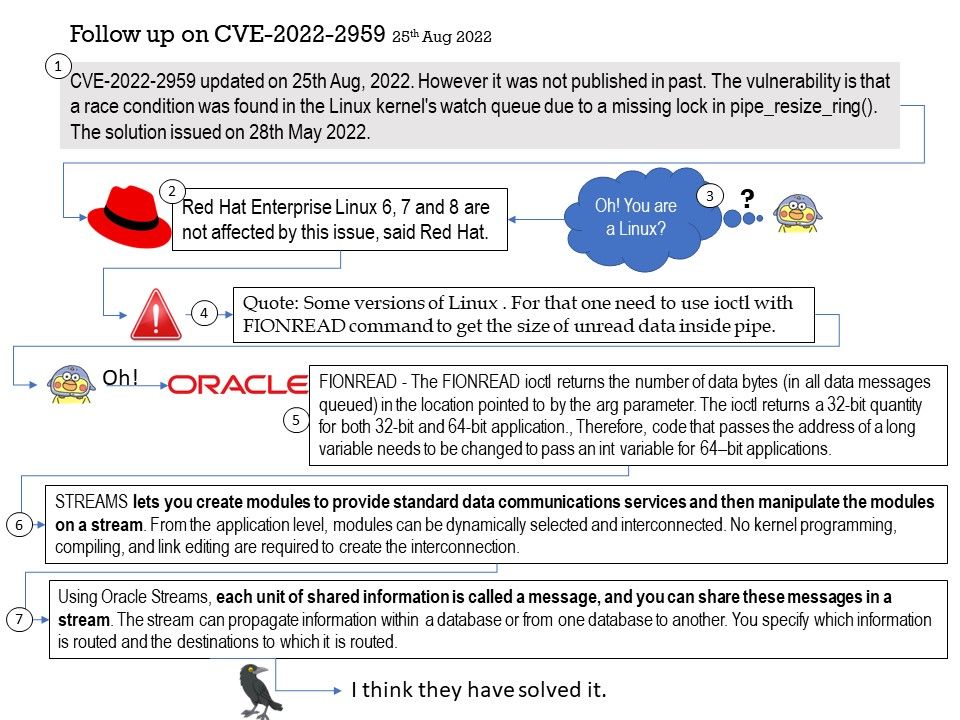
Vulnerability details: CVE-2022-2959 updated on 25th Aug, 2022. However it was not published in past. The vulnerability is that a race condition was found in the Linux kernel’s watch queue due to a missing lock in pipe_resize_ring(). The solution issued on 28th May 2022.
Description: A race condition was found in the Linux kernel’s watch queue due to a missing lock in the pipe_resize_ring(). The race condition occurs when a thread uses ioctl(IOC_WATCH_QUEUE_SET_SIZE) to resize the pipe buffer and free the old pipe buffer, while another thread uses keyctl() to trigger a notification in the watch queue, calling post_one_notification() and accessing the freed pipe buffer. This flaw allows a local user to crash the system or escalate their privileges on the system.
Red Hat Enterprise Linux 6, 7 and 8 are not affected by this issue. Some versions of Linux . For that one need to use ioctl with FIONREAD command to get the size of unread data inside pipe.
If you are interested in this topic, please see the details of my speculation from the attached picture.
Official details (CVE-2022-2959): See the link for details – https://nvd.nist.gov/vuln/detail/CVE-2022-2959