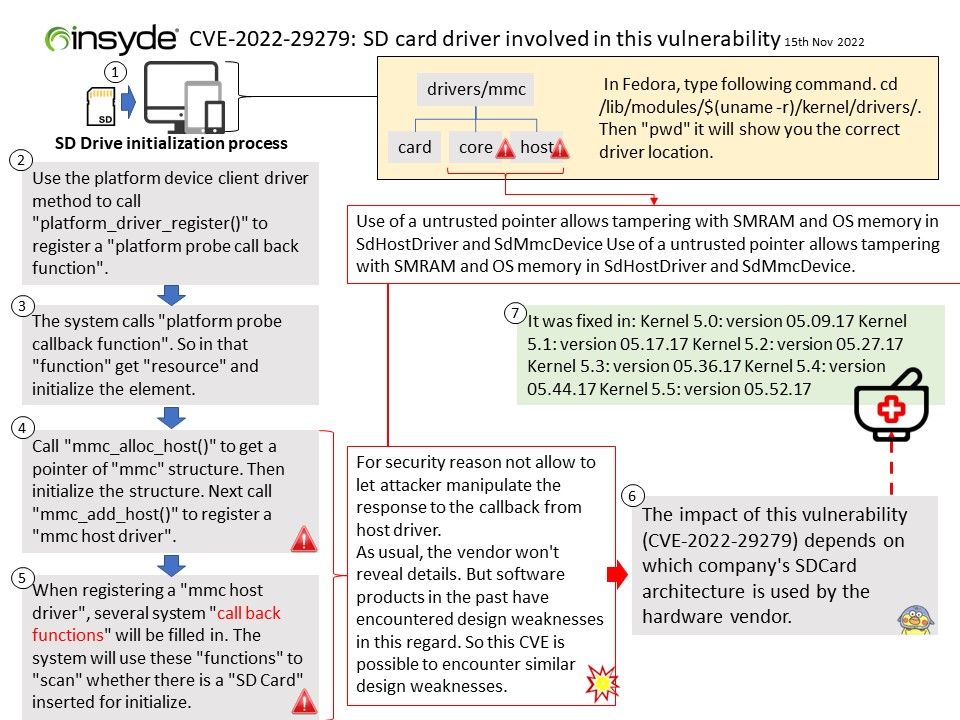
Preface: The impact of this flaw (CVE-2022-29279) depends on hardware vendor including smartphone, workstation and using which company SDCard architecture design.
Background: Insyde Software is leading worldwide provider of UEFI firmware systems management (BMC firmware) solutions, and custom engineering services for companies in the mobile, desktop, server, embedded and IoT (Internet-of-Things) computing industries.
SD/SDIO/MMC driver currently supports SD memory, SDIO cards, and eMMC chips. This protocol level driver builds on top of SDMMC and SD SPI host drivers.
SDMMC protocol layer handles specifics of SD protocol such as card initialization and data transfer commands.
Linux kernel has mmc subsystem which provides implementation of host cpu SPI/SDIO implementation, mmc/sd card physical implementation and Linux Block driver implementation based on gendisk.
- /drivers/mmc/core – consists of MMC/SD card related CSD, SID and other commands and responses.
- /drivers/mmc/host – consists of host cpu SPI/ SDIO related implementation.
- /drivers/mmc/card – consists of Linux block driver for MMC card and integration with Linux Block I/O layer.
In Fedora, type following command. cd [/]lib[/]modules[/]$(uname -r)[/]kernel[/]drivers[/].
Then “pwd” it will show you the correct driver location.
A host can communicate with SD/MMC card using a set of commands, and for each command host gets response from the MMC/SD card. These commands and responses have defined format. Each MMC/SD card command has 48 bits (6 bytes).
Vulnerability details: Use of a untrusted pointer allows tampering with SMRAM and OS memory in SdHostDriver and SdMmcDevice Use of a untrusted pointer allows tampering with SMRAM and OS memory in SdHostDriver and SdMmcDevice.
Solution: It was fixed in: Kernel 5.0: version 05.09.17 Kernel 5.1: version 05.17.17 Kernel 5.2: version 05.27.17 Kernel 5.3: version 05.36.17 Kernel 5.4: version 05.44.17 Kernel 5.5: version 05.52.17
Official announcement: Please refer to the link for details – https://www.insyde.com/security-pledge/SA-2022062