Preface: The main difference is that FreeRTOS has traditionally been completely open source (MIT license) whereas ThreadX has traditionally been completely commercial / proprietary. Therefore, FreeRTOS is dominating the embedded RTOS market, with something like 20% of new projects using it.
Background: Azure RTOS USBX is a high-performance USB host, device, and on-the-go (OTG) embedded stack. Azure RTOS USBX is fully integrated with Azure RTOS ThreadX and available for all Azure RTOS ThreadX–supported processors.
Azure RTOS USBX has a remarkably small minimal footprint of 10.5 KB of FLASH and 5.1 KB RAM for Azure RTOS USBX Device CDC/ACM support. Azure RTOS USBX Host requires a minimum of 18 KB of FLASH and 25 KB of RAM for CDC/ACM support.
The CDC-ACM class provides a serial interface for connecting devices such as modems to an embedded system. The package provides a CDC-ACM host class driver for a USB stack. The system allows a USB serial port device to be plugged into the host and recognized as a remote serial port.
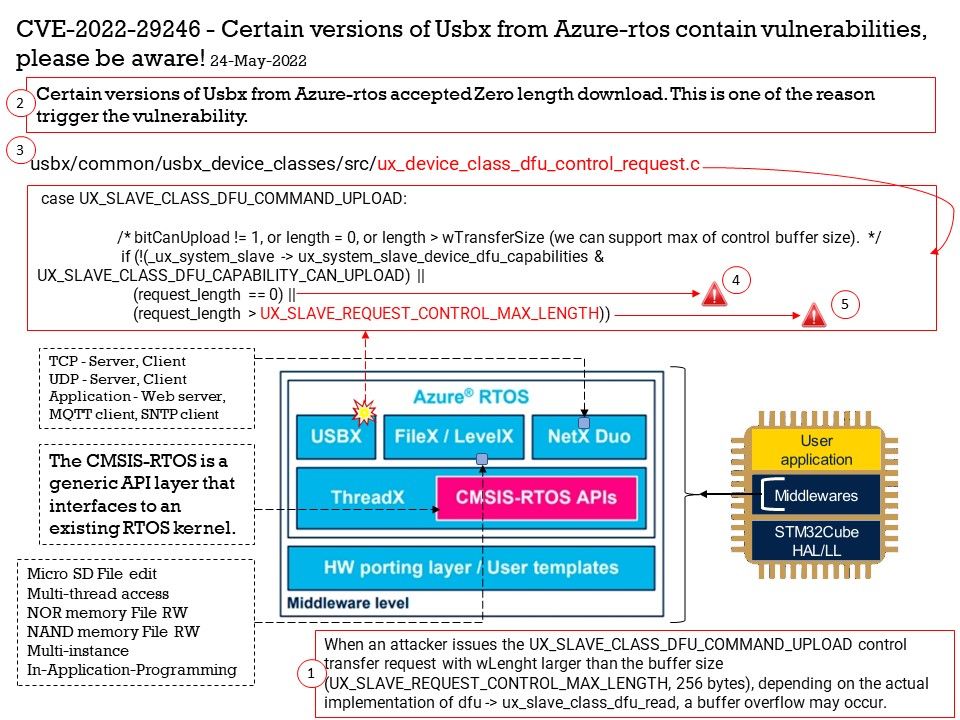
Vulnerability details: The implementation of ux_device_class_dfu_control_request function does not assure that a buffer overflow will not occur during handling of the DFU UPLOAD command. When an attacker issues the UX_SLAVE_CLASS_DFU_COMMAND_UPLOAD control transfer request with wLenght larger than the buffer size (UX_SLAVE_REQUEST_CONTROL_MAX_LENGTH, 256 bytes), depending on the actual implementation of dfu -> ux_slave_class_dfu_read, a buffer overflow may occur. In example ux_slave_class_dfu_read may read 4096 bytes (or more up to 65k) to a 256 byte buffer ultimately resulting in an overflow. Furthermore in case an attacker has some control over the read flash memory – in example DFU is used with an external SPI flash chip or the DFU DOWNLOAD command may be used – this may result in execution of arbitrary code and platform compromise.
Remedy: This fix has been included in USBX release 6.1.11.
Official announcement: Please refer to the link for details – https://github.com/azure-rtos/usbx/security/advisories/GHSA-hh5p-x584-j8hv