Preface: Login with key is safer than password login, and password login is easily intercepted.
Background: Net Framework is a software development platform developed by Microsoft for building and running Windows applications. The . Net framework consists of developer tools, programming languages, and libraries to build desktop and web applications. It is also used to build websites, web services, and games.
The .NET as a framework collobrate all the stuff it has under the hood for dealing with network connections. You can do peer to peer, FTP, HTTP, and direct socket connections, along with much more. However, there is no built-in support for is SSH.
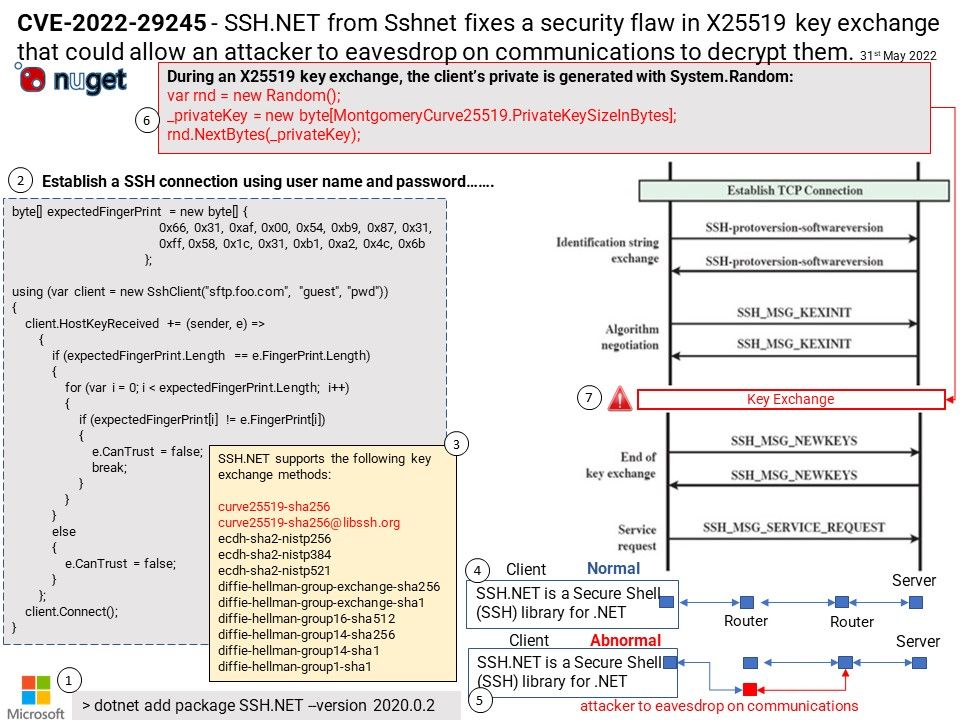
SSH[.]NET is a Secure Shell (SSH) library for [.]NET, optimized for parallelism and with broad framework support.
Vulnerability details: SSH.NET is a Secure Shell (SSH) library for .NET. In versions 2020.0.0 and 2020.0.1, during an X25519 key exchange, the client’s private key is generated with System.Random. System.Random is not a cryptographically secure random number generator, it must therefore not be used for cryptographic purposes. When establishing an SSH connection to a remote host, during the X25519 key exchange, the private key is generated with a weak random number generator whose seed can be brute forced. This allows an attacker who is able to eavesdrop on the communications to decrypt them.
Remedy: Version 2020.0.2 contains a patch for this issue – https://github.com/sshnet/SSH.NET/releases/tag/2020.0.2
Workaround: As a workaround, one may disable support for curve25519-sha256 and curve25519-sha256@libssh.org key exchange algorithms.