Preface: The product of MatrixSSL is used by many companies. Since MatrixSSL design in low memory footprint.
Whereby, they can partner with smart city infrastructure and IoT devices.
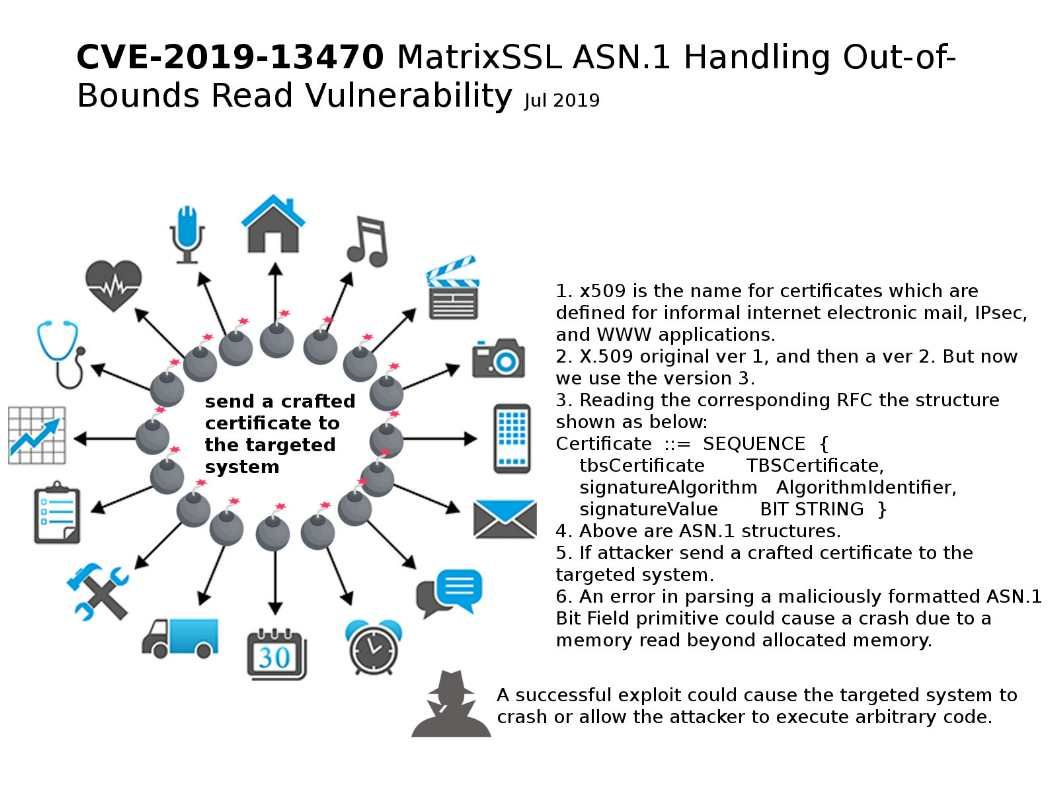
Vulnerability details: A vulnerability in MatrixSSL could allow an unauthenticated, remote attacker to execute arbitrary code or cause a denial of service (DoS) condition.
Our speculation:
- x509 is the name for certificates which are defined for informal internet electronic mail, IPsec, and WWW applications.
- X.509 original ver 1, and then a ver 2. But now we use the version 3.
- Reading the corresponding RFC the structure shown as below:
Certificate ::= SEQUENCE {
tbsCertificate TBSCertificate,
signatureAlgorithm AlgorithmIdentifier,
signatureValue BIT STRING } - Above are ASN.1 structures.
- If attacker send a crafted certificate to the targeted system.
- An error in parsing a maliciously formatted ASN.1 Bit Field primitive could cause a crash due to a memory read beyond allocated memory.
Vendor release software updates – https://github.com/matrixssl/matrixssl/releases