Background: Wind River’s VxWorks is widely used in communications, military, aerospace, industrial control and other fields for its high reliability and excellent real-time performance. For example, it is used in the US F-16, FA-18 fighters, B-2 stealth bombers and Patriot missiles. The most famous is the Mars probe that landed on the surface of Mars in April 1997 and landed in May 2008. The Phoenix, and the Curiosity Rover, which landed on Mars in August 2012, also used VxWorks 7.
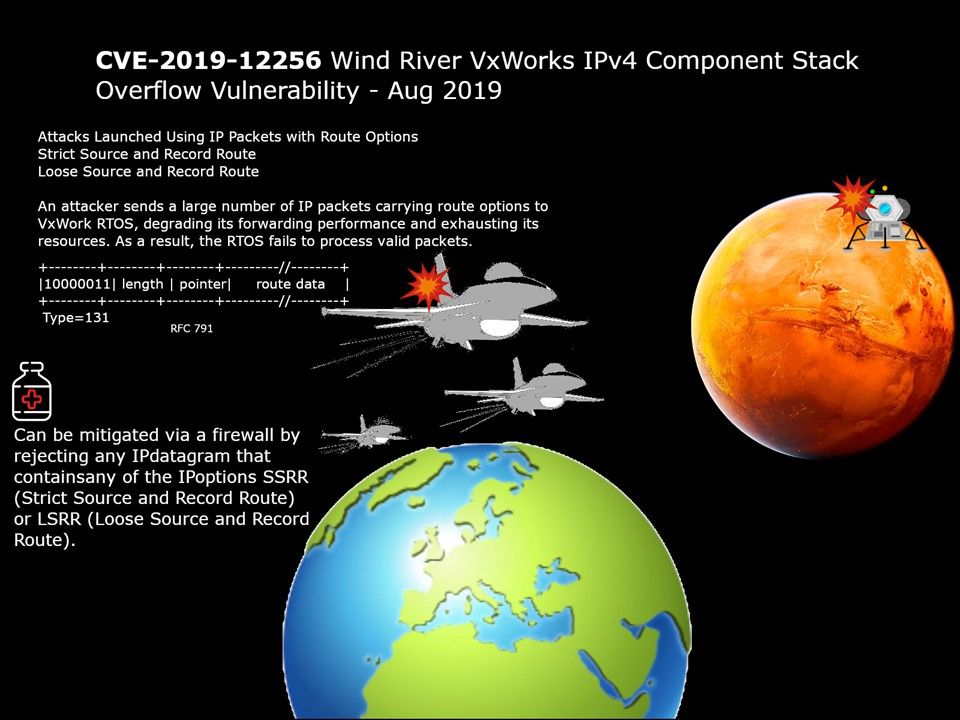
Vulnerability details: Wind River VxWorks 6.9 and vx7 has a Buffer Overflow in the IPv4 component. There is an IPNET security vulnerability: Stack overflow in the parsing of IPv4 packets? IP options.
Official announcement: CVE-2019-12256 Not affected by user-application code, this vulnerability resides in the IPv4 option parsing and may be triggered by IPv4 packets containing invalid options.The most likely outcome of triggering this defect is that the tNet0task crashes. In the worst-case scenario, this vulnerability can potentially lead to RCE.
Remedy: Fixed in Vx7 SR620 .Customers are advised to contact Wind River Customer Support.