Preface: VMware Aria Operations™ for Logs (formerly VMware vRealize® Log Insight™) analyzes complex log management through dashboards to provide shortest path to identify the problem.
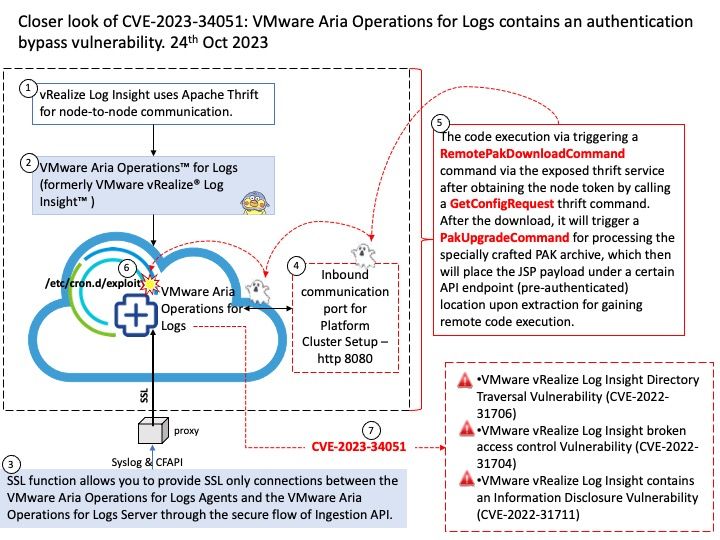
Background: What is aria operations for logs? Centralized Log Management VMware Aria Operations for Logs. Manage data at scale with centralized log management, deep operational visibility, and intelligent analytics for troubleshooting and auditing across environments. Protocol that the agent uses to send log events to the Aria Operations for Logs server. The possible values are cfapi and syslog. The default is cfapi. Ingestion API (CFAPI) The ingestion API provides several advantages over the syslog protocol including the ability to collect statistical and operational information about the agents directly in the server UI and also allows for server-side configurations to be pushed to agents. vRealize Log Insight uses Apache Thrift for node-to-node communication.
Vulnerability details: VMware Aria Operations for Logs contains an authentication bypass vulnerability. An unauthenticated, malicious actor can inject files into the operating system of an impacted appliance which can result in remote code execution.
Additional: The code execution via triggering a RemotePakDownloadCommand command via the exposed thrift service after obtaining the node token by calling a GetConfigRequest thrift command. After the download, it will trigger a PakUpgradeCommand for processing the specially crafted PAK archive, which then will place the JSP payload under a certain API endpoint (pre-authenticated) location upon extraction for gaining remote code execution.
Official announcement: Please refer to the link for details –https://nvd.nist.gov/vuln/detail/CVE-2023-34051