What is BIND 9? BIND is open source software that enables you to publish your Domain Name System (DNS) information on the Internet, and to resolve DNS queries for your users.
On 2006, named.conf parser design limitation found by Anonymous Monk. He list out the following.
- BIND::Conf_Parser – doesn’t deal with 9.x
- BIND::Config::Parser – bails out with ‘Bad text’ on my named.conf
- Cpanel – near to impossible to cut out something usable outside cpanel
- Webmin – seems to deal only with bind 8.x
- the /usr/sbin/named-checkconf utility packed with bind.9 – gives just an OK/not ok verdict upon named.conf, no way to store the underlying structure.
Announce design flaw – Sep 2018
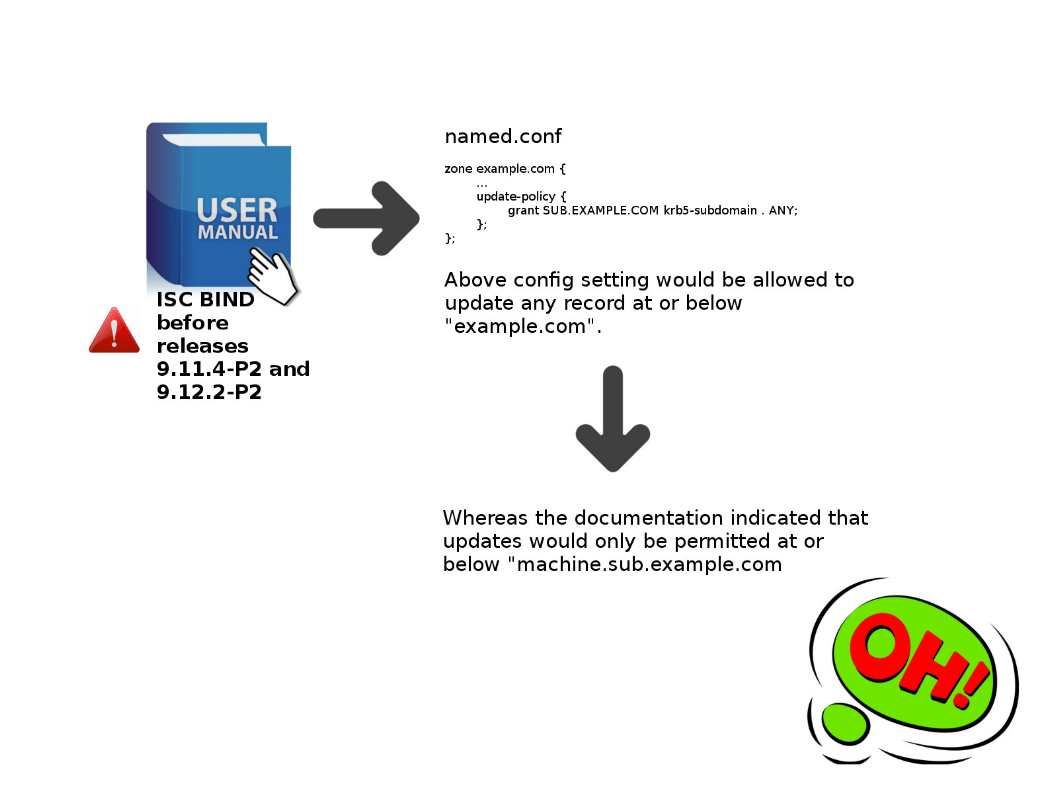
The krb5-subdomain and ms-subdomain update policy rule types permit updates from any client authenticated with a valid Kerberos or Windows machine principal from the REALM specified in the identity field, to modify records in the zone at or below the name specified in the name field.
Remark: A Kerberos realm is a set of managed nodes that share the same Kerberos database.
CVE-2018-5741: Update policies krb5-subdomain and ms-subdomain – https://kb.isc.org/docs/cve-2018-5741
Summary:
ISC BIND before releases 9.11.4-P2 and 9.12.2-P2 does not properly document the behaviour of the krb5-subdomain and ms-subdomain update policies.
Reference – Vulnerabilities announced last few months