Preface: Cybersecurity is always critical. Business operations define cost efficiency. Simply put, reduce costs in cyber defense is not a good idea. Because it might lost your company reputation.
Background: The details in today’s vulnerability bulletin are not detailed. Perhaps the reason for vendor not disclosed details is let their customer have schedule enough time do the patching. Since enterprise firm especially finance industry cannot do the patch immediately. But how to do the defense in this period of time? If you believe your company information security policy is compliance. As a result, Insider threat will be reduced. But in terms of zero-day, Attack vectors enable hackers to exploit system vulnerabilities, including the human element. So, virtual patching is a must in cyber security world today.
An intrusion detection system is a device or software application that monitors a network or systems for malicious activity or policy violations. IDS is one of the key components in virtual patching. Since the cyber defense involves a lot of labor resources and information. So it is recommend to assist by MSSP.
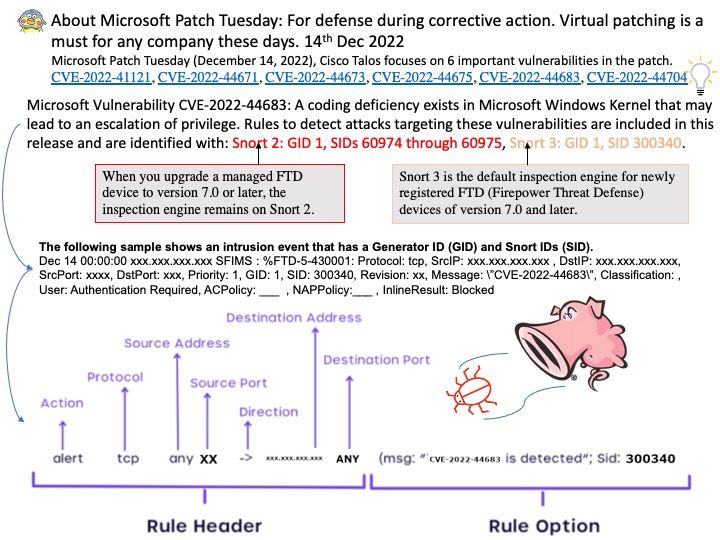
Vulnerability details: Microsoft Patch Tuesday (December 14, 2022), Cisco Talos focuses on 6 important vulnerabilities in the patch.
CVE-2022-41121, CVE-2022-44671, CVE-2022-44673, CVE-2022-44675, CVE-2022-44683 and CVE-2022-44704.
- CVE-2022-41121: Windows Graphics Component Elevation of Privilege Vulnerability
- CVE-2022-44671: Windows Graphics Component Elevation of Privilege Vulnerability
- CVE-2022-44673: Windows Client Server Run-Time Subsystem (CSRSS) Elevation of Privilege Vulnerability
- CVE-2022-44675: Windows Bluetooth Driver Elevation of Privilege Vulnerability
- CVE-2022-44683: Windows Kernel Elevation of Privilege Vulnerability
- CVE-2022-44704: Microsoft Windows Sysmon Elevation of Privilege Vulnerability
Official announcement: For details, see the link – https://msrc.microsoft.com/update-guide/en-us