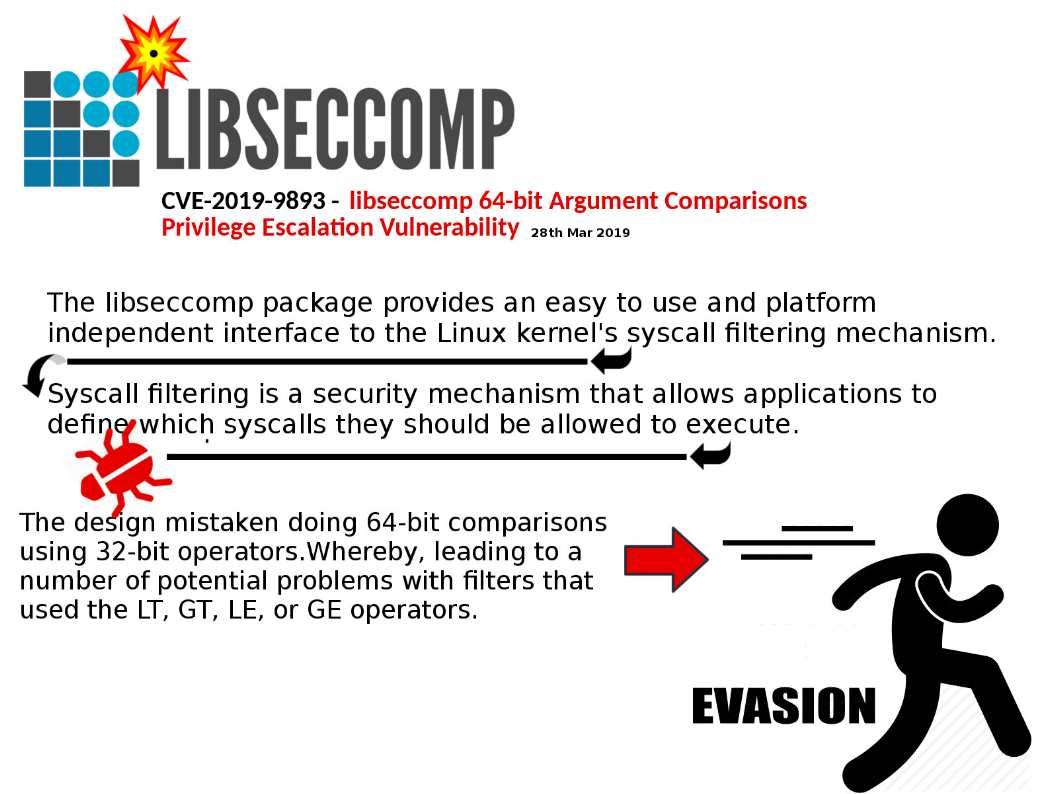
Preface: The libseccomp package provides an easy to use and platform independent interface to the Linux kernel’s syscall filtering mechanism.
Technical background: Syscall filtering is a security mechanism that allows applications to define which syscalls they should be allowed to execute.
Vulnerability detail: The design mistaken doing 64-bit comparisons using 32-bit operators.Whereby, leading to a number of potential problems with filters that used the LT, GT,
LE, or GE operators.
LT(less than)
GT(greater than)
LE(less than or equal to)
GE(greater than or equal to)
Impact: allow an unauthenticated, remote attacker to bypass restrictions and gain elevated privileges on a targeted system.
Fixed Software: https://github.com/seccomp/libseccomp/releases/tag/v2.4.0