Preface: Heard that estimated total of 1,000,000 SAP production systems could currently be at risk of being hacked.
Technical details:
When you configure sap router (saprouter) to allow remote (from the Internet) connections via the SAP GUI. The original design will add entries to the route tables for TCP port 3300, 3301, and 3303 the external application they are using (a gateway connection on these ports).
Default TCP gateway port exploit by hacker:
Since a default pathway built, so the hacker might have a channel to compromise the system. For example, send the malicious code try to conduct remote code execution. As a matter of fact, a proof of concept shown that SAP backend response with malicious code.
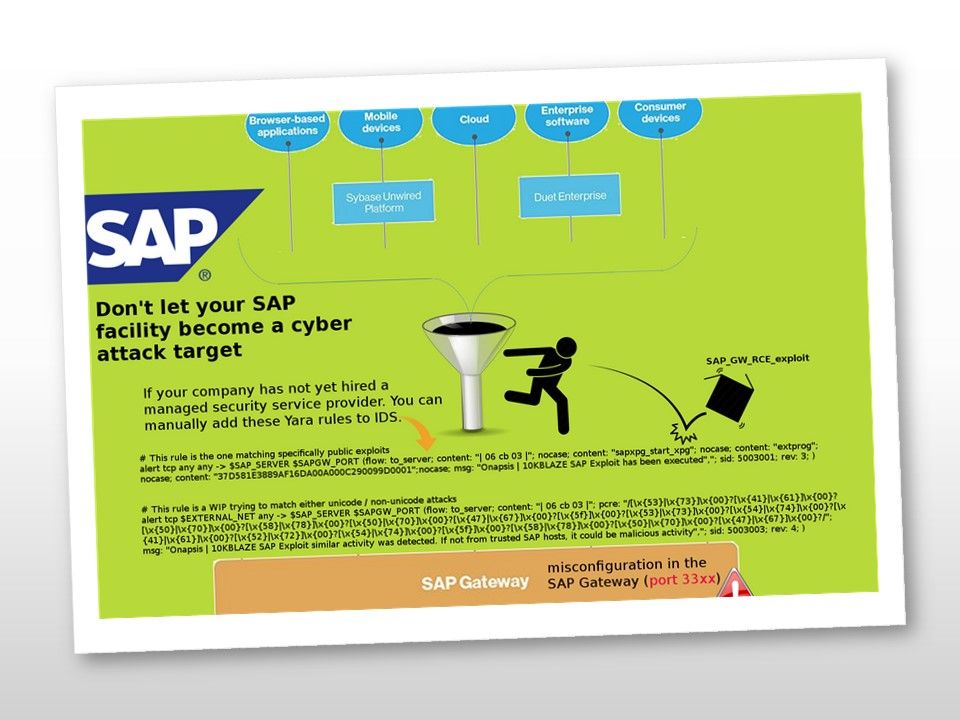
Remedy: If you outsource your cyber security watch guard responsibility to managed security services provider. They will create the yara rules to deny such malicious activities.
If not, you are require to create yara rules by yourself on IDS system. For more details, please refer to diagram.