Preface: According to the Android Security Bulletin, it releases a security bulletin once a month in the traditional way. However, if design limitations are related to other suppliers. The conclusion of the vulnerability details will be included the responses from relevant manufacturers. Therefore, Qualcomm also released its assessment of the severity of these problems.
I was not paying attention to this vulnerability in August 2023. Out of personal interest, maybe I’ll take this opportunity to dig into the details of this vulnerability. If you are interested, please become my guest.
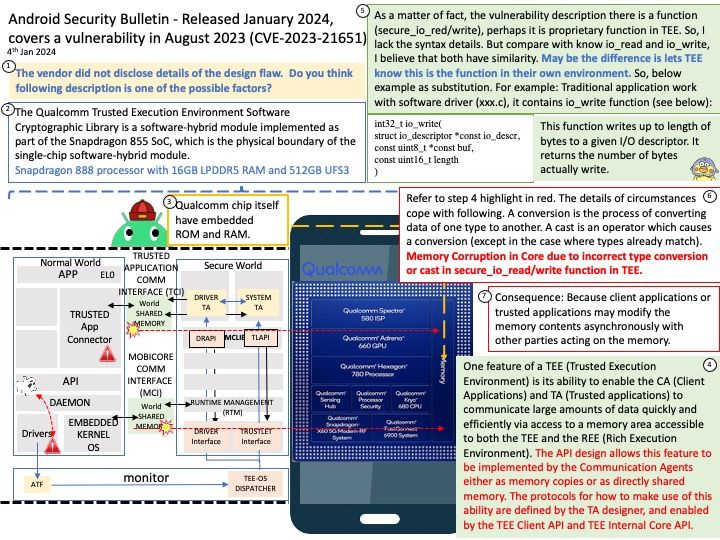
Background: The full name of TEE is trusted execution environment, which is an area on the CPU of mobile devices (smart phones, tablets, smart TVs). The role of this area is to provide a more secure space for data and code execution, and to ensure their confidentiality and integrity.
Other TEE operating systems are traditionally supplied as binary blobs by third-party vendors or developed internally. Developing internal TEE systems or licensing a TEE from a third-party can be costly to System-on-Chip (SoC) vendors and OEMs.
Trusty is a secure Operating System (OS) that provides a Trusted Execution Environment (TEE) for Android. A Trusty application is defined as a collection of binary files (executables and resource files), a binary manifest, and a cryptographic signature. At runtime, Trusty applications run as isolated processes in unprivileged mode under the Trusty kernel
The Qualcomm Trusted Execution Environment software cryptographic library is part of the implemented software hybrid module. As part of the Snapdragon SoC architecture. It is the physical boundary of a single-chip software hybrid module.
Vulnerability details: Memory Corruption in Core due to incorrect type conversion or cast in secure_io_read/write function in TEE.
Official announcement: Please refer to the link for details –
Android: https://source.android.com/docs/security/bulletin/2024-01-01
Qualcomm: https://docs.qualcomm.com/product/publicresources/securitybulletin/august-2023-bulletin.html