US-Cert urge that there are total five publicly available tools, which have been used for malicious purposes in recent cyber incidents around the world (see below):
Remote Access Trojan: JBiFrost
Webshell: China Chopper
Credential Stealer: Mimikatz
Lateral Movement Framework: PowerShell Empire
C2 Obfuscation and Exfiltration: HUC Packet Transmitter
RSA found a malware in 2017 and explore remote access Trojan (RAT) feature with advanced invisible feature.
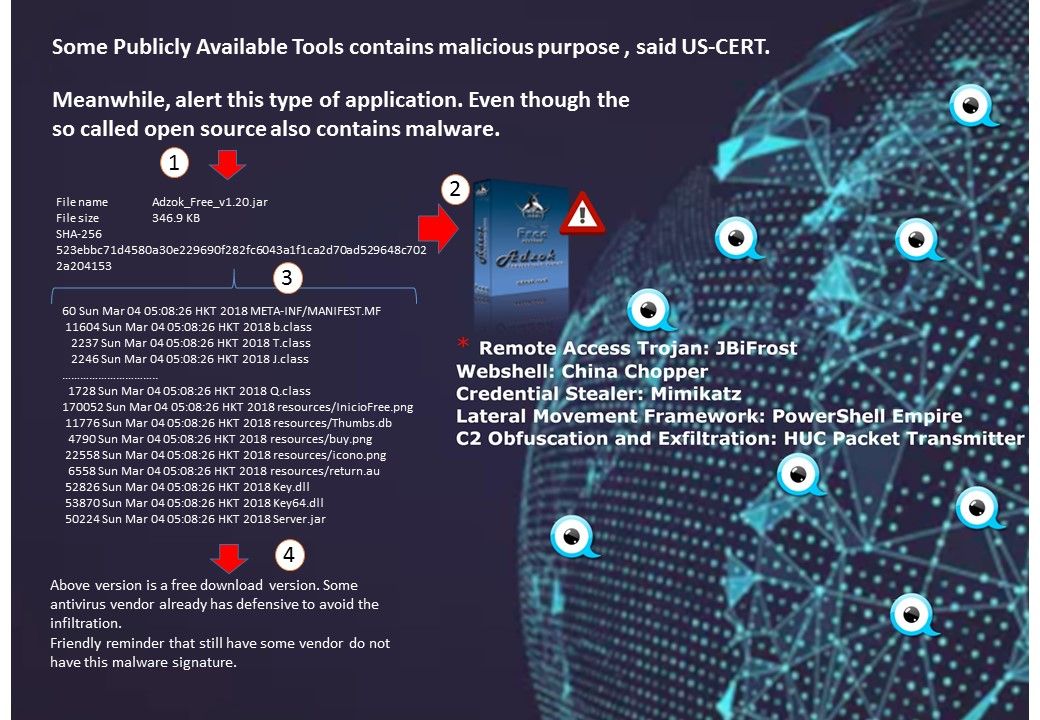
In this short discussion, I am going to focus the RAT (JBiFrost). Adzok is famous in dark web.
We seen malware exploits the Java archives.
A JAR (Java archive) is a package file format. It can be used as Java library or as standalone application. He is easy to change the shape to evade the detection.
Adzok proviced free download version. Some antivirus vendor already has defensive to avoid the infiltration.
Friendly reminder that still have some vendor do not have this malware signature.