Preface: ROCm open source software platform is AMD’s core strategy. This platform supports deep learning frameworks such as PyTorch 2.0 and TensorFlow.
Nvidia’s CUDA cores are indispensable for training and deploying neural networks and deep learning models, taking advantage of their parallel processing capabilities. To put that into perspective, a dozen Nvidia H100 GPUs can provide the same deep learning equivalent as 2,000 midrange CPUs.
Background: NVIDIA CUDA provides a simple C/C++ based interface. The CUDA compiler leverages parallelism built into the CUDA programming model as it compiles your program into code.
CUDA is a parallel computing platform and programming interface model created by Nvidia for the development of software which is used by parallel processors. It serves as an alternative to running simulations on traditional CPUs.
The CUDA Toolkit targets a class of applications whose control part runs as a process on a general purpose computing device, and which use one or more NVIDIA GPUs as coprocessors for accelerating single program, multiple data (SPMD) parallel jobs. Such jobs are self-contained, in the sense that they can be executed and completed by a batch of GPU threads entirely without intervention by the host process, thereby gaining optimal benefit from the parallel graphics hardware.
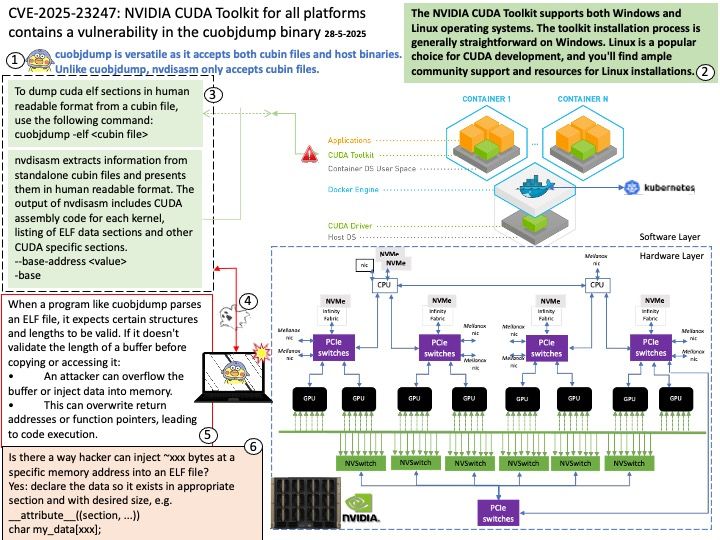
When a program like cuobjdump parses an ELF file, it expects certain structures and lengths to be valid. If it doesn’t validate the length of a buffer before copying or accessing it:
• An attacker can overflow the buffer or inject data into memory.
• This can overwrite return addresses or function pointers, leading to code execution.
Vulnerability details: NVIDIA CUDA Toolkit for all platforms contains a vulnerability in the cuobjdump binary, where a failure to check the length of a buffer could allow a user to cause the tool to crash or execute arbitrary code by passing in a malformed ELF file. A successful exploit of this vulnerability might lead to arbitrary code execution.
Official announcement: Please refer to the supplier announcement –https://nvidia.custhelp.com/app/answers/detail/a_id/5643