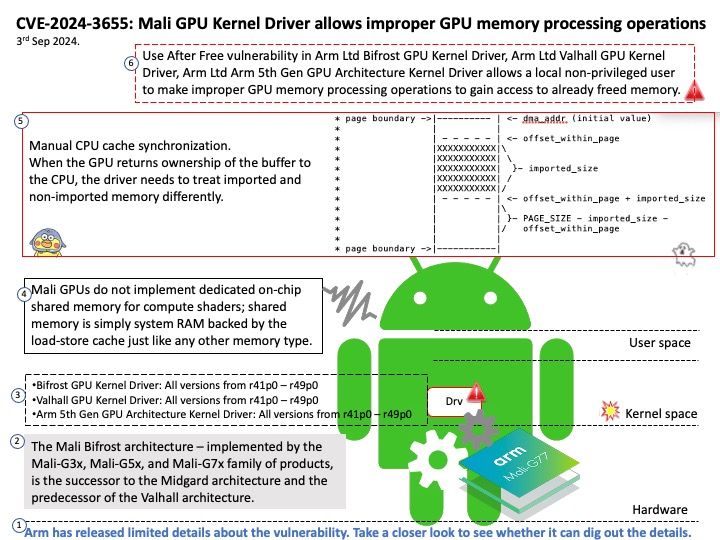
Preface: Use after free errors sometimes have no effect and other times cause a program to crash. While it is technically feasible for the freed memory to be re-allocated and for an attacker to use this reallocation to launch a buffer overflow attack.
Background: When the GPU returns ownership of the buffer to the CPU, the driver needs to treat imported and non-imported memory differently. The first case to consider is non-imported sub-regions at the beginning of the first page and at the end of last page. For these sub-regions: CPU cache shall be committed with a clean+invalidate, in order to keep the last CPU write. Imported region prefers the opposite treatment: this memory has been legitimately mapped and used by the GPU, hence GPU writes shall be committed to memory, while CPU cache shall be invalidated to make sure that CPU reads the correct memory content.
Vulnerability details: Use After Free vulnerability in Arm Ltd Bifrost GPU Kernel Driver, Arm Ltd Valhall GPU Kernel Driver, Arm Ltd Arm 5th Gen GPU Architecture Kernel Driver allows a local non-privileged user to make improper GPU memory processing operations to gain access to already freed memory.
Impact: This issue affects Bifrost GPU Kernel Driver: from r43p0 through r49p0; Valhall GPU Kernel Driver: from r43p0 through r49p0; Arm 5th Gen GPU Architecture Kernel Driver: from r43p0 through r49p0.
Official announcement: Please refer to the link for details – https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities