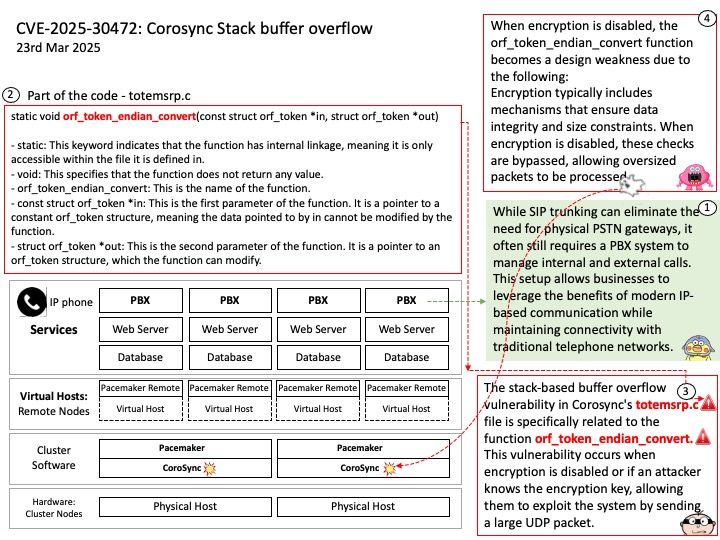
Preface: Even with the popularity of IP phone SIP trunking, the public telephone network still relies on PABX (Private Automatic Branch Exchange) systems in many cases. SIP trunking allows businesses to connect their IP PBX systems to the Public Switched Telephone Network (PSTN) using the Session Initiation Protocol (SIP), which facilitates voice and data communication over the internet.
Background: Gentoo-based clusters are groups of computers running the Gentoo Linux distribution, configured to work together to perform tasks or provide services. These clusters can be designed for various purposes, such as High Availability (HA), High Performance Computing (HPC), High Throughput Computing (HTC), andHigh Efficiency Computing (HEC).
Gentoo’s flexibility and configurability make it well-suited for building clusters. Many modern Gentoo-based clusters use the Corosync messaging layer and the Pacemaker cluster resource manager. The Corosync Cluster Engine is a group communication system with additional features for implementing high availability within applications. The project provides four C API features: A closed process group communication model with virtual synchrony guarantees for creating replicated state machines.
Even with the popularity of IP phone SIP trunking, the public telephone network still relies on PABX (Private Automatic Branch Exchange) systems in many cases. SIP trunking allows businesses to connect their IP PBX systems to the Public Switched Telephone Network (PSTN) using the Session Initiation Protocol (SIP), which facilitates voice and data communication over the internet. While SIP trunking can eliminate the need for physical PSTN gateways, it often still requires a PBX system to manage internal and external calls1. This setup allows businesses to leverage the benefits of modern IP-based communication while maintaining connectivity with traditional telephone networks.
Vulnerability details: Corosync through 3.1.9, if encryption is disabled or the attacker knows the encryption key, has a stack-based buffer overflow in orf_token_endian_convert in exec/totemsrp.c via a large UDP packet.
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2025-30472