Preface: The registration of CVE records is largely out of sync with the time of the event. Perhaps the new release of CVE record by today, however it was happened few weeks or months ago. But with reference of these vulnerabilities records. Vulnerability scanner can precisely provide a result to you after scan.
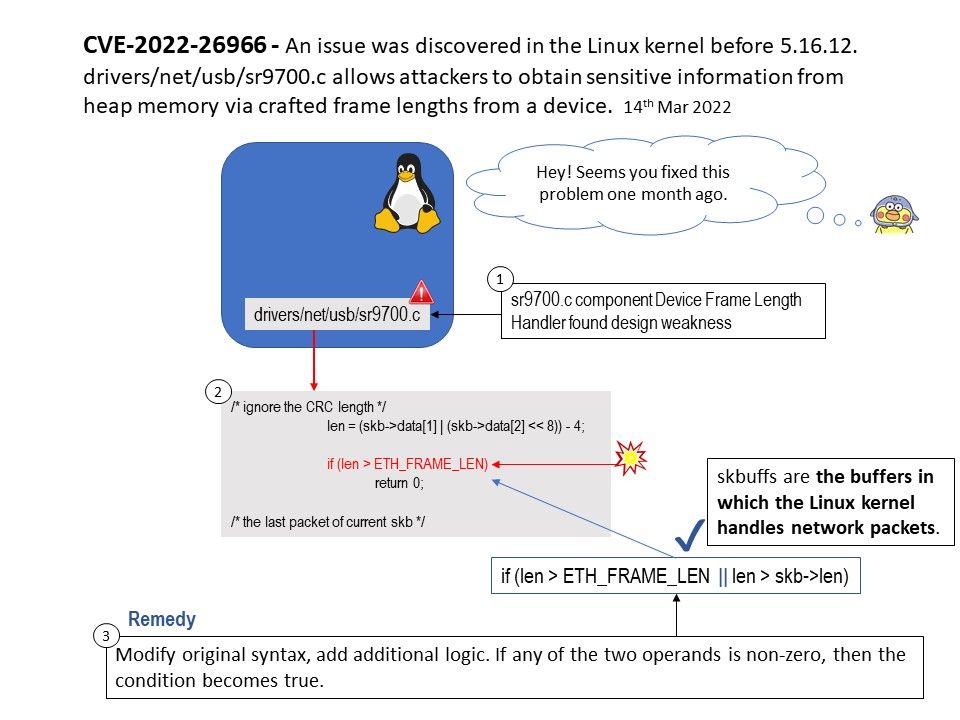
Background: SR9700 is a type of USB to Ethernet Converter and is compatible with USB 1.1 protocol, the design merge SR9700 device driver (sr9700[.]c) into the Linux Kernel. The buffers used by the kernel to manage network packets are referred to as sk_buffs in Linux.
The buffers are always allocated as at least two separate components: a fixed size header of type struct sk_buff; and a variable length area large enough to hold all or part of the data of a single packet.
Vulnerability details: An issue was discovered in the Linux kernel before 5.16.12. drivers/net/usb/sr9700[.]c allows attackers to obtain sensitive information from heap memory via crafted frame lengths from a device.
Remedy: Please refer to the link for details – https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=e9da0b56fe27206b49f39805f7dcda8a89379062
.jpg?width=1920&height=1080&fit=bounds)
.jpg?width=1920&height=1080&fit=bounds)