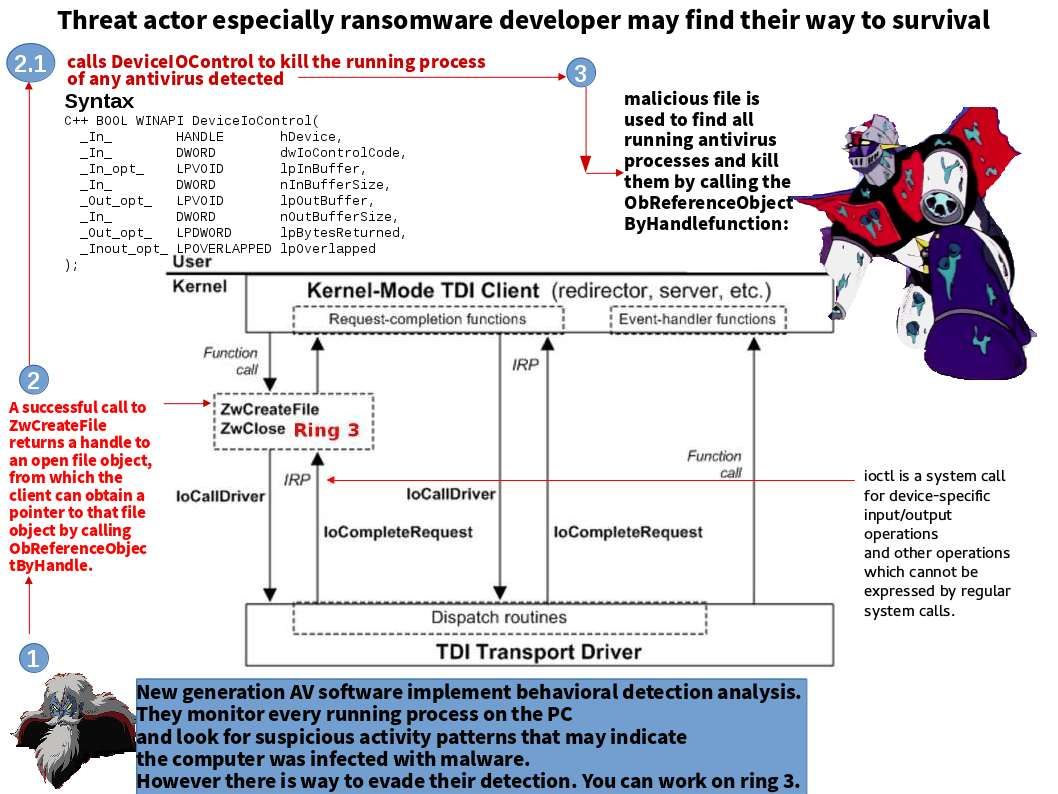
Just heard that there is a new attack method use by ransomware. The malware intend to stop and disable your workstation antivirus process. Since no antivirus protection, threat actor is free to do their task. Perhaps the defense vendor pay the focus on Ring 0 attack (kernel). Meanwhile new generation AV software implement behavioral detection analysis. So is there any space for threat actor?Yes, the ring 3 looks provides space to threat actor. They may find a way to evade the detection.
For instance:
- List all loaded DLL libraries in current process.
- Find entry-point address of every imported API function of each DLL library.
- Remove the injected hook JMP instruction by replacing it with the API’s original bytes.
Should you have interest to receive a high level understanding, please refer above diagram for reference.
Hello my loved one! I wish to say that this post is amazing, great written and include almost all vital infos. I would like to peer extra posts like this .|