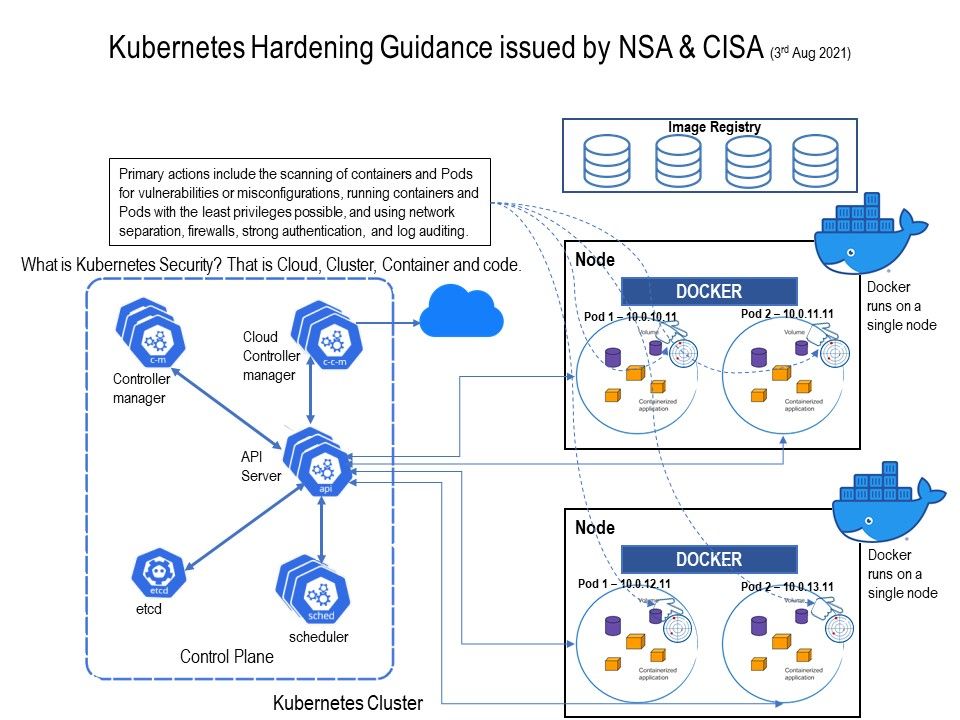
Preface: Docker helps to “create” containers, and Kubernetes allows you to “manage” them at runtime. What is Kubernetes Security? That is Cloud, Cluster, Container and code.
Background: Kubernetes is commonly targeted for three reasons observing by NSA and CISA. They are data theft, computational power theft, or denial of service. Cyber attacks encountered in the Kubernetes environment in 2020. Details are as follow:
Capital One – Occurring in 2019, this breach saw 30GB of credit application data affecting about 106 million people being exfiltrated.
A mis-configured firewall that allowed an attacker to query internal metadata and gain credentials of an Amazon Web Services
Docker hub – Attackers managed to plant malicious images in the Docker hub. unknowingly deployed cryptocurrency miners in the form of Docker
containers that then diverted compute resources toward mining cryptocurrency for the attacker.
Microsoft Azure – Microsoft is another organization that’s been seeing a lot of cryptojacking woes of its own. After disclosing that there was a large-scale cryptomining attack against Kubernetes cluster in Azure in April 2020.
Telsa – Automaker Tesla was one of the earlier victims of cryptojacking when a Kubernetes cluster was compromised due to an administrative
console not being password protected.(Mis-configuration)
Jenkins – Hackers managed to exploit a vulnerability in Jenkins to cryptomine to the tune of about $3.5 million, or 10,800 Monero in 18 months. In Docker’s operation environment, it was discovered that six malicious images had been collectively pulled over 2 million times, that’s 2 million users potentially mining Monero for the attacker.
To avoid similar incidents from happening – The National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA) released a Cybersecurity Technical Report, “Kubernetes Hardening Guidance,” Primary actions include the scanning of containers and Pods for vulnerabilities or mis-configurations, running containers and Pods with the least privileges possible, and using network separation, firewalls, strong authentication, and log auditing. Please refer to the link for details – https://www.nsa.gov/News-Features/Feature-Stories/Article-View/Article/2716980/nsa-cisa-release-kubernetes-hardening-guidance/