Few years ago, heard that 64 bit version of windows is more secure. Expert was told, 64-bit operating systems aren’t immune to malware but security features are stronger.
Address Space Layout Randomization – incorrect guess may result in the program crashing
Mandatory Driver Signing – prevents unsigned drivers provided by malware from running on the system
Kernel Patch Protection – prevents device drivers from patching the kernel
Data Execution Protection – DEP allows an operating system to mark certain areas of memory as “non-executable
It looks that above 4 items of feature capable to protect the OS system infected by malware. Recall cyber incident history, 1st version of the Stuxnet computer virus that was used to attack Iran’s nuclear program in November 2007, being developed as early as 2005, when Iran was still setting up its uranium enrichment facility. SCADA system compatible with windows 32 bit and 64 bit OS. SCADA manufacturer strongly recommend to use 64 Bit operating systems. The 32 Bit operating systems may be used for compatibility reasons within already existing configurations. Seems we can figure out hints of malware weakness. And speculate that Stuxnet virus infect the SCADA system are run on top of windows 32 bit operating system (OS) instead of 64 bits.
Descendant Of The Malware – embedded new DLL injection technique (reflective DLL injection)
A more sophisticated of DLL injection method, so called reflective DLL injection. It loads code without calling the normal Windows API calls, potentially bypassing DLL load monitoring. Conceptual diagram shown as below:
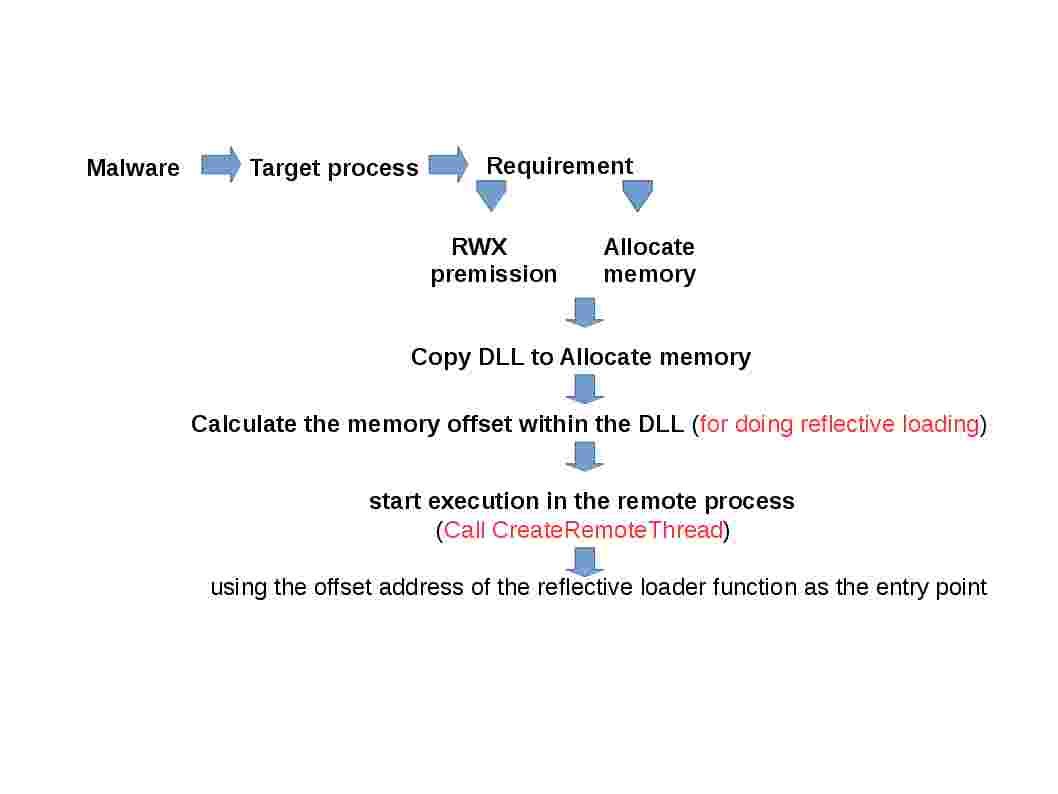
Above reflective loader function will find the following target:
- Process Environment Block (PEB) of the target process
- suitable CPU register
- the address in memory of kernel32.dll
- and other required libraries
Next step: Find the memory addresses of required API functions such as LoadLibraryA, GetProcAddress, and VirtualAlloc. Relies on these API functions to load the DLL (malware) into memory and call its DllMain entry point.
Remark: What is DllMain Entry point – An optional entry point into a dynamic-link library (DLL). When the system starts or terminates a process or thread, it calls the entry-point function for each loaded DLL using the first thread of the process. The system also calls the entry-point function for a DLL when it is loaded or unloaded using the LoadLibrary and FreeLibrary functions.
In the DllMain function, you can perform only a very limited set of actions. The thing is that some DLL may be not loaded yet, and you cannot call functions from them.
Does it mean that the 64-bit operating systems not easy to implant malware?
All applications except malware would use the standard main memory. The copy (shadow memory) is designed to be used by malware. Shell code might have difficulties to pass though parameters on shadow memory space. The fact is that there are differences between x86 and x64 operating system. The 64-bit addressing capability and a flat set of 16 64-bit registers for general use. If that “shadow space” on the stack was not allocated by the caller, the function may not work as expected.
Remark: In 64 bit OS environment, the allocates pages in the shadow region on demand. That is only when page contains tag information. As every byte of tracked program data need four more bytes for its tag, part of the physical memory footprint of a process increase by a factor of four.
Speculation:
Believe that nuclear power facility still have 32 bit SCADA application in operation. But no harm to keep, the fact is that even though you upgrade to 64 bit OS. It is hard to guarantee you can avoid malware silently implant to your environment.
Below url is the malware attack nuclear power facilities historical information for your reference.
https://www.google.com.hk/url?sa=t&rct=j&q=&esrc=s&source=web&cd=1&cad=rja&uact=8&ved=0ahUKEwj72tfKnN_QAhVIGpQKHTdgBywQFggaMAA&url=http%3A%2F%2Fwww.antihackingonline.com%2Fnetwork-protocol-topology-standard%2Fmalware-vs-nuclear-power-do-you-think-scada-system-is-the-culprit-of-attack-on-nuclear-power-system%2F&usg=AFQjCNGDNhe7wFJgFQSDK7V3QDnWqiB99A
I must convey my affection for your kind-heartedness for those people that must have help on this issue. Your special commitment to getting the solution all over was particularly functional and has without exception permitted professionals just like me to achieve their goals. This important tutorial signifies so much a person like me and even further to my mates. Best wishes; from each one of us.
I simply want to mention I am just newbie to blogging and honestly enjoyed you’re website. Most likely I’m planning to bookmark your site . You amazingly have beneficial articles. With thanks for sharing with us your blog.
Keep working ,terrific job!
I’ve been absent for a while, but now I remember why I used to love this site. Thanks , I will try and check back more frequently. How frequently you update your site?
I am continuously invstigating online for ideas that can aid me. Thank you!
As I web-site possessor I believe the content material here is rattling great , appreciate it for your efforts. You should keep it up forever! Good Luck.
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your website is magnificent, let alone the content!
I’m really impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you customize it yourself? Anyway keep up the nice quality writing, it’s rare to see a nice blog like this one today..
Excellent read, I just passed this onto a colleague who was doing some research on that. And he just bought me lunch since I found it for him smile Therefore let me rephrase that: Thanks for lunch!
Magnificent beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog website? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
It¡¦s truly a nice and useful piece of information. I¡¦m happy that you simply shared this helpful info with us. Please keep us informed like this. Thank you for sharing.
Fantastic beat ! I would like to apprentice while you amend your website, how could i subscribe for a blog website? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear concept
Hi, Neat post. There’s a problem with your website in web explorer, would test this¡K IE nonetheless is the market leader and a large portion of folks will pass over your excellent writing due to this problem.
I just wanted to write down a brief note so as to express gratitude to you for those amazing tricks you are posting at this site. My considerable internet search has now been honored with wonderful know-how to share with my classmates and friends. I would mention that we website visitors actually are unquestionably endowed to live in a notable website with very many brilliant professionals with interesting points. I feel somewhat happy to have discovered the website and look forward to so many more awesome minutes reading here. Thank you once more for all the details.
My brother suggested I might like this website. He was entirely right. This post actually made my day. You can not imagine simply how much time I had spent for this information! Thanks!
I think other website proprietors should take this web site as an model, very clean and magnificent user friendly style and design, as well as the content. You’re an expert in this topic!
Definitely, what a splendid blog and educative posts, I definitely will bookmark your website.Have an awsome day!
Hi there, just became aware of your blog through Google, and found that it is truly informative. I am going to watch out for brussels. I will be grateful if you continue this in future. Lots of people will be benefited from your writing. Cheers!
Awsome info and straight to the point. I am not sure if this is really the best place to ask but do you folks have any ideea where to get some professional writers? Thx 🙂
Hello, you used to write magnificent, but the last several posts have been kinda boring¡K I miss your super writings. Past several posts are just a bit out of track! come on!
I¡¦ll right away snatch your rss as I can not in finding your email subscription link or e-newsletter service. Do you have any? Kindly allow me realize in order that I may subscribe. Thanks.
Thanks for any other informative website. Where else may just I am getting that kind of info written in such an ideal way? I have a mission that I’m simply now operating on, and I have been at the look out for such info.
Hello. fantastic job. I did not imagine this. This is a excellent story. Thanks!
I’m just writing to make you know what a fantastic experience my cousin’s girl encountered studying your web site. She discovered numerous issues, most notably how it is like to possess a great teaching character to make men and women without problems fully grasp some impossible things. You really did more than her desires. I appreciate you for rendering such warm and friendly, dependable, educational and even unique guidance on your topic to Janet.
I do agree with all the ideas you’ve presented in your post. They’re very convincing and can definitely work. Still, the posts are too quick for novices. May you please prolong them a bit from subsequent time? Thank you for the post.
This is really interesting, You’re a very skilled blogger. I have joined your feed and look forward to seeking more of your wonderful post. Also, I’ve shared your site in my social networks!
My wife and i have been absolutely fulfilled when Michael managed to conclude his investigations from the ideas he made out of your blog. It’s not at all simplistic just to possibly be giving for free secrets and techniques which often other people may have been making money from. And we do understand we now have you to appreciate because of that. The entire illustrations you made, the straightforward blog navigation, the relationships you make it possible to instill – it’s got all powerful, and it’s making our son and our family recognize that that topic is entertaining, and that is really serious. Thanks for everything!
Valuable information. Fortunate me I found your website accidentally, and I am surprised why this twist of fate did not happened earlier! I bookmarked it.
I think this is one of the most important info for me. And i am glad reading your article. But want to remark on few general things, The site style is ideal, the articles is really nice : D. Good job, cheers
I do accept as true with all the ideas you’ve offered to your post. They’re very convincing and can certainly work. Still, the posts are too brief for starters. May just you please prolong them a little from subsequent time? Thank you for the post.
Wow, fantastic weblog structure! How lengthy have you been blogging for? you make running a blog look easy. The total glance of your website is magnificent, as neatly as the content material!
We are a group of volunteers and opening a new scheme in our community. Your site offered us with valuable information to work on. You have done a formidable job and our whole community will be grateful to you.
I have been absent for some time, but now I remember why I used to love this web site. Thank you, I will try and check back more often. How frequently you update your website?
I was suggested this website by my cousin. I am not sure whether this post is written by him as nobody else know such detailed about my problem. You are incredible! Thanks!
I enjoy you because of your own efforts on this web site. My aunt enjoys making time for investigations and it’s really simple to grasp why. Almost all learn all about the compelling tactic you give functional techniques via this blog and welcome contribution from others on this subject matter then our own simple princess is without a doubt understanding a great deal. Take advantage of the rest of the year. You’re doing a first class job.
Wow, incredible blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your website is fantastic, let alone the content!
I’ve been surfing on-line more than three hours as of late, but I by no means discovered any fascinating article like yours. It is beautiful value sufficient for me. In my view, if all website owners and bloggers made just right content as you did, the web might be a lot more useful than ever before.
Keep functioning ,great job!
Thanks for any other informative blog. Where else may I am getting that kind of info written in such a perfect manner? I’ve a venture that I’m just now running on, and I have been on the glance out for such info.
Simply desire to say your article is as surprising. The clarity in your post is simply great and i can assume you’re an expert on this subject. Well with your permission allow me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please carry on the enjoyable work.
Great work! That is the kind of info that should be shared around the web. Disgrace on the seek engines for not positioning this publish upper! Come on over and discuss with my site . Thanks =)
magnificent put up, very informative. I wonder why the other specialists of this sector don’t realize this. You must continue your writing. I’m sure, you’ve a huge readers’ base already!
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your web site is excellent, as well as the content!
fantastic publish, very informative. I ponder why the other specialists of this sector do not realize this. You must continue your writing. I’m confident, you’ve a great readers’ base already!
I¡¦ve read some just right stuff here. Definitely price bookmarking for revisiting. I surprise how so much effort you put to create this sort of fantastic informative website.
I have been surfing online more than 3 hours lately, but I by no means found any interesting article like yours. It¡¦s lovely price sufficient for me. Personally, if all site owners and bloggers made good content as you did, the net will be a lot more useful than ever before.
You made some clear points there. I did a search on the issue and found most individuals will go along with with your website.
Great article and right to the point. I am not sure if this is truly the best place to ask but do you folks have any ideea where to hire some professional writers? Thanks in advance 🙂
I’m still learning from you, but I’m trying to reach my goals. I absolutely liked reading everything that is written on your blog.Keep the stories coming. I enjoyed it!
Magnificent beat ! I would like to apprentice while you amend your web site, how could i subscribe for a blog web site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
Magnificent beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog web site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
Definitely believe that which you stated. Your favorite justification seemed to be on the web the easiest thing to be aware of. I say to you, I definitely get irked while people consider worries that they plainly do not know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side effect , people can take a signal. Will likely be back to get more. Thanks
We are a group of volunteers and opening a new scheme in our community. Your web site offered us with valuable information to work on. You’ve done an impressive job and our entire community will be thankful to you.
I just wanted to develop a brief message to say thanks to you for all the nice pointers you are writing on this website. My long internet investigation has finally been compensated with high-quality points to write about with my two friends. I would repeat that many of us readers are unquestionably fortunate to live in a remarkable site with so many outstanding people with very helpful suggestions. I feel pretty lucky to have come across the web page and look forward to many more fabulous minutes reading here. Thank you once again for a lot of things.
Great write-up, I¡¦m normal visitor of one¡¦s site, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
We’re a group of volunteers and opening a new scheme in our community. Your website provided us with valuable info to work on. You’ve done an impressive job and our entire community will be thankful to you.
Wow, wonderful blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your website is fantastic, as well as the content!
Good ¡V I should definitely pronounce, impressed with your website. I had no trouble navigating through all tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your customer to communicate. Excellent task..
Very nice post. I just stumbled upon your blog and wanted to say that I have really enjoyed surfing around your blog posts. After all I will be subscribing to your feed and I hope you write again very soon!
Hi there, just became alert to your blog through Google, and found that it is really informative. I am going to watch out for brussels. I will be grateful if you continue this in future. Numerous people will be benefited from your writing. Cheers!
I have been examinating out many of your stories and i can state pretty good stuff. I will definitely bookmark your site.
I simply wished to say thanks once more. I’m not certain the things I might have done without the entire solutions discussed by you directly on such a field. Completely was a very frustrating issue in my position, nevertheless observing this specialised approach you treated the issue forced me to weep for delight. Now i’m happy for the service and hope that you recognize what an amazing job you are always accomplishing training men and women using your websites. I know that you haven’t come across all of us.
Thanks for any other informative website. The place else may I am getting that kind of info written in such a perfect way? I have a mission that I am simply now working on, and I’ve been at the look out for such info.
Great amazing things here. I¡¦m very happy to look your article. Thank you so much and i am looking forward to contact you. Will you kindly drop me a mail?
I think this is among the most important information for me. And i’m glad reading your article. But want to remark on few general things, The site style is ideal, the articles is really nice : D. Good job, cheers
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
I am only writing to make you know what a terrific discovery my daughter went through visiting your webblog. She came to find some things, which include how it is like to have an awesome helping mood to make the others with ease know precisely specified problematic topics. You really surpassed people’s desires. Many thanks for coming up with those warm and friendly, trustworthy, informative and even fun guidance on the topic to Gloria.
Hello, Neat post. There’s an issue together with your website in internet explorer, would check this¡K IE nonetheless is the market chief and a big portion of people will miss your great writing due to this problem.
Thanks , I’ve just been looking for info about this topic for ages and yours is the best I’ve came upon so far. However, what in regards to the conclusion? Are you positive about the source?
Great beat ! I would like to apprentice while you amend your website, how can i subscribe for a blog web site? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear idea
It is suitable opportunity to create some schemes for the future. I’ve go through this article and if I could, I desire to recommend you some enlightening suggestions.
I was excited to find this site. I want to to thank you for your time for this wonderful read!! I definitely really liked every part of it and i also have you saved to fav to check out new things on your website.
I simply desire to inform you that I am new to writing and incredibly valued your site. Very possible I am likely to remember your blog post . You literally have fabulous article material. Be Grateful For it for sharing with us your internet site report
Truly enjoyable points you’ll have remarked, warm regards for writing.
I simply need to share it with you that I am new to online blogging and completely valued your write-up. Quite possibly I am most likely to save your blog post . You simply have superb article information. Appreciate it for swapping with us your very own url webpage
Greetings here, just turned out to be aware of your web page through The Big G, and have found that it is seriously helpful. I will like should you decide continue on this idea.
I think this is one of the most important information for me. And i’m glad reading your article. But should remark on some general things, The website style is perfect, the articles is really nice : D. Good job, cheers
I have not checked in here for a while since I thought it was getting boring, but the last several posts are good quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
Nice read, I just passed this onto a friend who was doing a little research on that. And he actually bought me lunch since I found it for him smile Therefore let me rephrase that: Thanks for lunch!
you are truly a just right webmaster. The website loading velocity is incredible. It kind of feels that you are doing any unique trick. In addition, The contents are masterpiece. you have done a magnificent task in this topic!
Keep functioning ,splendid job!
Hello. remarkable job. I did not expect this. This is a excellent story. Thanks!
Hi my family member! I wish to say that this post is amazing, great written and include approximately all important infos. I¡¦d like to look extra posts like this .
Thanks a bunch for sharing this with all of us you really recognize what you are speaking about! Bookmarked. Please also discuss with my website =). We can have a hyperlink alternate arrangement among us!
You made some good points there. I looked on the internet for the subject and found most persons will agree with your website.
I have recently started a web site, the information you offer on this website has helped me tremendously. Thanks for all of your time & work.
Thanks for your whole labor on this web page. My daughter really loves making time for research and it is simple to grasp why. My spouse and i know all relating to the lively medium you make very useful thoughts by means of your blog and in addition invigorate contribution from visitors on this situation and our favorite daughter has been studying so much. Take advantage of the rest of the year. You’re the one carrying out a very good job.
I precisely wanted to thank you so much again. I am not sure the things that I might have taken care of in the absence of the actual hints shared by you concerning my situation. This has been a horrifying issue in my position, but finding out this well-written manner you solved the issue made me to cry with contentment. Now i am thankful for this advice and as well , have high hopes you really know what an amazing job you’re carrying out training other individuals all through your blog post. I’m certain you haven’t come across any of us.
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I’ll be subscribing to your augment and even I achievement you access consistently quickly.
I got what you intend, regards for posting .Woh I am glad to find this website through google. “Success is dependent on effort.” by Sophocles.
Good ¡V I should certainly pronounce, impressed with your site. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or something, web site theme . a tones way for your client to communicate. Excellent task..
I¡¦ve been exploring for a little bit for any high quality articles or blog posts in this kind of area . Exploring in Yahoo I eventually stumbled upon this website. Reading this info So i am glad to convey that I have an incredibly excellent uncanny feeling I came upon just what I needed. I so much without a doubt will make certain to do not overlook this site and provides it a look regularly.
Super-Duper website! I am loving it!! Will come back again. I am taking your feeds also
Definitely believe that which you said. Your favorite justification seemed to be on the internet the simplest thing to be aware of. I say to you, I definitely get irked while people think about worries that they plainly don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people can take a signal. Will likely be back to get more. Thanks|
Excellent goods from you, man. I’ve understand your stuff previous to and you are just too excellent. I really like what you’ve acquired here, certainly like what you’re stating and the way in which you say it. You make it enjoyable and you still take care of to keep it smart. I can not wait to read much more from you. This is actually a wonderful website.
I like this site very much, Its a really nice billet to read and get information. “You can never learn less, you can only learn more.” by Richard Buckminster Fuller.
Hello.This post was really fascinating, particularly because I was looking for thoughts on this issue last Tuesday.
Excellent read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch as I found it for him smile Thus let me rephrase that: Thank you for lunch!
You could definitely see your expertise in the work you write. The arena hopes for even more passionate writers like you who aren’t afraid to mention how they believe. Always follow your heart. “There are only two industries that refer to their customers as users.” by Edward Tufte.
Great site. Plenty of useful info here. I’m sending it to several buddies ans also sharing in delicious. And certainly, thanks in your effort!
I have recently started a site, the information you provide on this web site has helped me tremendously. Thank you for all of your time & work.
I dugg some of you post as I cerebrated they were handy handy
This is very interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your great post. Also, I’ve shared your website in my social networks!
Hello There. I found your blog using msn. This is a very well written article. I’ll make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I’ll certainly return.
Normally I don’t learn post on blogs, however I wish to say that this write-up very compelled me to check out and do it! Your writing style has been amazed me. Thank you, quite nice post.
Wow! This can be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Actually Fantastic. I’m also a specialist in this topic therefore I can understand your effort.
I¡¦ll immediately grasp your rss as I can’t in finding your email subscription link or newsletter service. Do you’ve any? Kindly let me understand in order that I may just subscribe. Thanks.
I intended to put you the little observation so as to give many thanks over again for your personal breathtaking tips you’ve contributed on this page. This has been so unbelievably open-handed of people like you to provide easily all a lot of folks could have advertised for an ebook to get some money for themselves, precisely given that you might well have tried it if you decided. Those inspiring ideas in addition acted to be a easy way to know that other individuals have the identical eagerness the same as mine to know the truth a little more on the subject of this issue. I know there are many more enjoyable situations in the future for individuals that browse through your site.
Unquestionably believe that which you stated. Your favorite justification seemed to be on the web the simplest thing to be aware of. I say to you, I definitely get irked while people think about worries that they plainly don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people can take a signal. Will likely be back to get more. Thanks
Excellent blog here! Also your site loads up fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
Whats Taking place i’m new to this, I stumbled upon this I’ve found It positively helpful and it has helped me out loads. I am hoping to contribute & help other users like its aided me. Great job.
Well I truly enjoyed reading it. This post offered by you is very constructive for correct planning.
A lot of thanks for all of the labor on this web site. Debby delights in doing investigations and it’s really easy to understand why. All of us hear all about the dynamic mode you provide helpful thoughts via this blog and in addition improve response from visitors on this concept plus our own girl is certainly starting to learn a lot of things. Take advantage of the rest of the year. You have been performing a stunning job.
There is clearly a bunch to identify about this. I suppose you made certain nice points in features also.
I simply couldn’t go away your site before suggesting that I actually loved the usual info a person supply to your guests? Is gonna be again frequently to check out new posts
Pretty section of content. I just stumbled upon your website and in accession capital to assert that I acquire actually enjoyed account your blog posts. Anyway I will be subscribing to your feeds and even I achievement you access consistently quickly.
Great awesome issues here. I¡¦m very satisfied to see your post. Thanks a lot and i am taking a look forward to touch you. Will you kindly drop me a mail?
Bonjour ! Il n’y aurai pas des doublons ? Car je viens plusieurs fois les mêmes articles sur votre site !
Thanks, I have recently been looking for information about this topic for a long time and yours is the best I have discovered so far. However, what about the bottom line? Are you sure in regards to the supply?
I think you have mentioned some very interesting details , regards for the post.
We’re a group of volunteers and opening a new scheme in our community. Your web site provided us with valuable information to work on. You’ve done an impressive job and our whole community will be thankful to you.
I like the valuable info you provide in your articles. I will bookmark your blog and check again here regularly.
I am quite certain I’ll learn many new stuff right here!
Best of luck for the next!
Hi to all, how is all, I think every one is getting more from this web site, and your views are nice in favor of new viewers.
Normally I do not read post on blogs, but I wish to say that this write-up very forced me to check out and do so! Your writing style has been amazed me. Thanks, very nice article.
Hello. Great job. I did not imagine this. This is a splendid story. Thanks!
It is in reality a great and useful piece of info. I’m glad that you simply shared this useful info with us. Please stay us up to date like this. Thanks for sharing.
great issues altogether, you simply gained a new reader. What might you recommend in regards to your publish that you just made a few days in the past? Any certain?
I dugg some of you post as I thought they were extremely helpful extremely helpful
Enjoyed examining this, very good stuff, appreciate it. “The fox knows many things, but the hedgehog knows one big thing.” by Archilocus.
Wow, superb blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is fantastic, let alone the content!
I was extremely pleased to discover this site. I need to to thank you for ones time for this particularly fantastic read!! I definitely loved every part of it and i also have you saved to fav to check out new things on your web site.
obviously like your web-site but you need to take a look at the spelling on quite a few of your posts. Several of them are rife with spelling issues and I to find it very troublesome to tell the truth then again I will definitely come back again.
Some really prime articles on this website , bookmarked .
Terrific paintings! That is the kind of info that should be shared across the net. Disgrace on Google for not positioning this submit upper! Come on over and seek advice from my site . Thanks =)
I’ve been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all webmasters and bloggers made good content as you did, the net will be a lot more useful than ever before.
Whats Taking place i am new to this, I stumbled upon this I’ve found It positively helpful and it has helped me out loads. I hope to contribute & assist different users like its helped me. Good job.
of course like your web site but you need to take a look at the spelling on several of your posts. A number of them are rife with spelling issues and I to find it very troublesome to tell the reality on the other hand I¡¦ll certainly come back again.
I simply could not go away your website prior to suggesting that I extremely loved the usual info an individual provide in your guests? Is going to be again steadily in order to investigate cross-check new posts.
I was recommended this web site by my cousin. I am not sure whether this post is written by him as no one else know such detailed about my problem. You are amazing! Thanks!
I simply could not go away your website before suggesting that I extremely loved the usual information an individual provide in your visitors? Is going to be again ceaselessly in order to investigate cross-check new posts.
Great tremendous things here. I¡¦m very satisfied to see your post. Thanks so much and i’m taking a look ahead to touch you. Will you please drop me a e-mail?
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our local library but I think I learned more clear from this post. I am very glad to see such wonderful info being shared freely out there.
I have to get across my affection for your generosity for women who have the need for assistance with that concept. Your personal commitment to passing the solution up and down was amazingly effective and have continuously helped some individuals like me to realize their ambitions. Your new insightful tips and hints entails this much a person like me and far more to my office colleagues. Thank you; from all of us.
As a Newbie, I am always searching online for articles that can help me. Thank you
I just hope to advise you that I am new to online blogging and extremely loved your report. Very possible I am inclined to remember your blog post . You simply have superb article material. Like it for sharing with us your main web information
This is ideal occasion to produce some intentions for the longer term. I have study this write-up and if I can, I wish to encourage you few great pointers.
I’m still learning from you, as I’m making my way to the top as well. I absolutely liked reading all that is posted on your website.Keep the information coming. I loved it!
I was extremely pleased to uncover this site. I need to to thank you for ones time for this wonderful read!! I definitely really liked every bit of it and i also have you saved as a favorite to check out new stuff in your website.
Might be near unthinkable to see well-qualified users on this content, then again you come across as like you understand the things that you’re preaching about! Cheers
It certainly is practically not possible to encounter well-aware men or women on this subject, fortunately you appear like you understand exactly what you’re revealing! Thanks
Pretty absorbing highlights you have said, many thanks for setting up.
I just need to share it with you that I am new to blogging and certainly cherished your review. Probably I am inclined to store your blog post . You really have outstanding article materials. Value it for telling with us your site page
Very well written article. It will be supportive to anyone who employess it, including myself. Keep doing what you are doing – for sure i will check out more posts.
Hi there, just became alert to your blog through Google, and found that it is truly informative. I am going to watch out for brussels. I’ll appreciate if you continue this in future. Numerous people will be benefited from your writing. Cheers!
Thank you, I’ve just been searching for information approximately this subject for a long time and yours is the best I have discovered till now. But, what concerning the conclusion? Are you positive about the source?
Wow, awesome blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is wonderful, as well as the content!
Magnificent beat ! I wish to apprentice while you amend your website, how can i subscribe for a blog web site? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear idea
I¡¦ll right away grasp your rss feed as I can’t find your email subscription link or newsletter service. Do you have any? Kindly permit me understand so that I may just subscribe. Thanks.
I’m very happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this greatest doc.
Thank you so much for giving everyone an extremely marvellous possiblity to check tips from here. It is often so superb plus jam-packed with a lot of fun for me personally and my office friends to search the blog at the very least 3 times in 7 days to learn the fresh secrets you will have. And definitely, I am certainly fascinated concerning the fabulous pointers you serve. Selected 1 areas in this article are easily the best we’ve had.
How do I import Firefox bookmarks and other settings from one user account to another?
Bonjour ! Vraiment bien comme site!!!
Thank you for your article post.Really looking forward to read more. Much obliged.
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
I’m more than happy to find this great site. I want to to thank you for ones time for this fantastic read!! I definitely appreciated every part of it and i also have you bookmarked to see new things on your website.
It’s proper day to make some goals for the longer term. I have study this post and if I can, I desire to recommend you handful of entertaining recommendation.
I merely intend to show you that I am new to blogging and very much loved your article. Most likely I am most likely to remember your blog post . You absolutely have extraordinary article material. Be Thankful For it for expressing with us the best web webpage
Exceedingly alluring knowledge you’ll have mentioned, warm regards for submitting.
It certainly is almost impossible to find well-informed readers on this subject, still you look like you be aware of the things you’re preaching about! Excellent
I was more than happy to find this page. I want to to thank you for your time just for this fantastic read!! I definitely loved every bit of it and I have you book marked to check out new things in your blog.
I just wish to inform you you that I am new to blogging and totally adored your site. Very possible I am inclined to remember your blog post . You seriously have memorable article materials. Admire it for giving out with us your favorite site webpage
It is most suitable time to get some schedules for the long-term. I have digested this write-up and if I may, I wish to encourage you handful of fascinating ideas.
I merely desire to tell you that I am new to writing a blog and totally valued your work. Very likely I am prone to store your blog post . You undoubtedly have impressive article material. Appreciate it for sharing with us your current site page
Wonderful paintings! This is the kind of information that are supposed to be shared across the web. Disgrace on Google for not positioning this post upper! Come on over and seek advice from my web site . Thank you =)
Just want to say your article is as amazing. The clearness in your post is simply spectacular and i can assume you’re an expert on this subject. Well with your permission let me to grab your feed to keep up to date with forthcoming post. Thanks a million and please carry on the gratifying work.
It is actually nearly extremely difficult to encounter well-informed parties on this matter, nonetheless you appear like you understand what exactly you’re preaching about! Bless You
Great awesome issues here. I¡¦m very happy to peer your article. Thanks so much and i am taking a look forward to contact you. Will you please drop me a mail?
Very nice info and straight to the point. I am not sure if this is actually the best place to ask but do you guys have any ideea where to get some professional writers? Thx 🙂
Hey just wanted to give you a quick heads up and let you know a few of the images aren’t loading correctly. I’m not sure why but I think its a linking issue. I’ve tried it in two different browsers and both show the same outcome.|
I would like to thnkx for the efforts you’ve put in writing this blog. I am hoping the same high-grade website post from you in the upcoming as well. In fact your creative writing skills has inspired me to get my own site now. Really the blogging is spreading its wings fast. Your write up is a good example of it.
I was very happy to uncover this web site. I need to to thank you for ones time due to this wonderful read!! I definitely enjoyed every little bit of it and i also have you book marked to see new stuff in your website.
I simply wish to show you that I am new to online blogging and thoroughly adored your review. Quite possibly I am going to store your blog post . You undoubtedly have lovely article information. Like it for share-out with us your site webpage
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a bit, but other than that, this is excellent blog. A fantastic read. I’ll certainly be back.
There is noticeably a lot to know about this. I think you made certain nice points in features also.
Hello.This article was extremely remarkable, particularly because I was looking for thoughts on this topic last Tuesday.
Thanks for sharing superb informations. Your web-site is very cool. I’m impressed by the details that you have on this blog. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found simply the information I already searched all over the place and simply could not come across. What a great web-site.
Wow, amazing blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your website is great, as well as the content!
Nice blog here! Also your website loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my website loaded up as quickly as yours lol
Just want to say your article is as surprising. The clarity in your post is simply spectacular and i could assume you’re an expert on this subject. Well with your permission let me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please carry on the enjoyable work.
Excellent blog right here! Also your website so much up very fast! What host are you the usage of? Can I am getting your associate hyperlink on your host? I desire my website loaded up as quickly as yours lol
I was excited to uncover this site. I need to to thank you for your time for this particularly wonderful read!! I definitely really liked every part of it and i also have you book marked to see new information in your web site.
I merely have to advise you that I am new to posting and undeniably admired your information. Likely I am most likely to remember your blog post . You literally have great article material. Appreciate it for share-out with us the best url page
Thank you ever so for you post.Thanks Again. Fantastic.
I simply wish to inform you that I am new to blogging and totally liked your information. More than likely I am prone to bookmark your blog post . You indeed have outstanding article blog posts. Love it for share-out with us the best website post
Just stumble upon your blog from from time to time. nice article
For hottest news you have to visit web and on internet I found this site as
a finest site for latest updates.
Well I sincerely liked reading it. This subject procured by you is very effective for accurate planning.
I’m still learning from you, while I’m trying to achieve my goals. I absolutely love reading all that is posted on your blog.Keep the posts coming. I loved it!
I have been checking out a few of your articles and i can state pretty clever stuff. I will surely bookmark your site.
I simply wanted to appreciate you all over again. I’m not certain the things I would’ve tried without the type of methods provided by you relating to this situation. It became an absolute challenging case for me, but finding out a new skilled form you resolved the issue took me to leap over happiness. Extremely happy for your help and thus have high hopes you really know what a powerful job you have been getting into teaching the rest by way of a blog. Probably you’ve never met all of us.
Definitely, what a magnificent website and educative posts, I surely will bookmark your website.All the Best!
excellent post, very informative. I wonder why the opposite specialists of this sector do not realize this. You should proceed your writing. I am confident, you have a great readers’ base already!
Useful information. Lucky me I discovered your web
site by chance, and I’m surprised why this coincidence did not came about in advance!
I bookmarked it.
What’s up mates, pleasant article and nice arguments commented
here, I am in fact enjoying by these.
After I initially commented I seem to have clicked the -Notify
me when new comments are added- checkbox and now whenever
a comment is added I recieve 4 emails with the exact same comment.
Perhaps there is a way you are able to remove me from that service?
Thanks!
Good blog post. I certainly appreciate this
site. Keep it up!
Please let me know if you’re looking for a article writer for your site.
You have some really great posts and I believe I would be a good asset.
If you ever want to take some of the load off, I’d really like to write some content
for your blog in exchange for a link back to mine.
Please send me an e-mail if interested. Many thanks!
Hello! I just would like to offer you a huge thumbs up for your great info you’ve got right here on this post.
I will be coming back to your web site for more soon.
I would like to express my thanks to this writer just for bailing me out of this setting. As a result of browsing through the world-wide-web and seeing techniques which are not beneficial, I assumed my entire life was done. Living without the presence of answers to the problems you have solved by means of your good article content is a serious case, and ones that could have badly affected my career if I had not discovered your site. That mastery and kindness in handling the whole lot was tremendous. I don’t know what I would have done if I had not discovered such a subject like this. I’m able to now look ahead to my future. Thank you very much for this professional and effective help. I won’t hesitate to recommend your blog to anyone who desires care about this area.
Thank you a lot for providing individuals with remarkably breathtaking opportunity to read articles and blog posts from here. It can be very terrific plus full of amusement for me personally and my office peers to search your website at minimum thrice in a week to study the new stuff you have. And definitely, I’m just actually pleased with your mind-boggling pointers you serve. Selected 3 tips in this posting are indeed the most impressive I’ve ever had.
It is perfect time to make some plans for the future and it is time to be happy. I have read this post and if I could I wish to suggest you few interesting things or advice. Maybe you could write next articles referring to this article. I wish to read even more things about it!
Good write-up, I am regular visitor of one¡¦s website, maintain up the excellent operate, and It is going to be a regular visitor for a lengthy time.
I would like to thank you for the efforts you’ve put in writing this web site. I am hoping the same high-grade website post from you in the upcoming also. In fact your creative writing skills has encouraged me to get my own blog now. Really the blogging is spreading its wings fast. Your write up is a good example of it.
My spouse and i were quite joyous when John managed to complete his web research from your precious recommendations he gained through the blog. It’s not at all simplistic to simply happen to be handing out tips and tricks that other folks have been trying to sell. We really acknowledge we have the blog owner to thank for that. The main explanations you have made, the straightforward blog menu, the relationships you can aid to promote – it’s all superb, and it’s really aiding our son in addition to the family know that this topic is pleasurable, and that is exceptionally mandatory. Thank you for the whole lot!
Hi, i think that i saw you visited my web site thus i came to “return the favor”.I am attempting to find things to improve my site!I suppose its ok to use some of your ideas!!
Hi, Neat post. There’s a problem with your website in internet explorer, may check this¡K IE still is the market leader and a big component to other folks will leave out your excellent writing because of this problem.
Nice weblog right here! Additionally your web site a lot up fast! What host are you using? Can I get your affiliate link in your host? I want my web site loaded up as quickly as yours lol
Excellent post. I was checking constantly this blog and I’m impressed! Very useful info specially the last part 🙂 I care for such information a lot. I was looking for this certain info for a very long time. Thank you and best of luck.
Hi, i think that i saw you visited my weblog so i came to “return the favor”.I am trying to find things to improve my website!I suppose its ok to use a few of your ideas!!
Hello there! This post could not be written any better!
Reading through this post reminds me of my previous room mate!
He always kept talking about this. I will forward
this page to him. Fairly certain he will have a good read.
Many thanks for sharing!
You are my inhalation , I have few web logs and very sporadically run out from to post .I believe this internet site has got some rattling fantastic information for everyone. “The fewer the words, the better the prayer.” by Martin Luther.
Unquestionably imagine that that you stated.
Your favorite reason seemed to be at the net the simplest thing to take into accout of.
I say to you, I certainly get irked whilst people consider issues that they just do not recognise about.
You managed to hit the nail upon the top as neatly as
defined out the entire thing without having side-effects
, folks can take a signal. Will likely be back to get
more. Thanks
Nice post. I learn something new and challenging on blogs
I stumbleupon every day. It’s always interesting to read through articles from other writers and practice something from their websites.
Hi there, You have done an incredible job. I’ll definitely digg
it and personally suggest to my friends. I’m confident they will
be benefited from this website.
Hi! Do you know if they make any plugins to safeguard against
hackers? I’m kinda paranoid about losing everything I’ve worked hard on. Any suggestions?
I simply desired to thank you very much again. I’m not certain the things I could possibly have sorted out without those techniques provided by you concerning such a theme. This was a real fearsome difficulty for me, nevertheless being able to see the very specialised style you dealt with the issue took me to jump for contentment. Now i’m thankful for the information and have high hopes you are aware of an amazing job that you are getting into teaching men and women all through your web page. I’m certain you have never got to know all of us.
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but other than that, this is excellent blog. An excellent read. I’ll definitely be back.
I am constantly invstigating online for tips that can aid me. Thank you!
Pretty nice post. I just stumbled upon your weblog and wished to say that I’ve truly enjoyed browsing your blog posts. After all I will be subscribing to your feed and I hope you write again soon!
Hello.This post was really fascinating, particularly because I was investigating for thoughts on this issue last Tuesday.
You actually make it appear really easy with your presentation however I to find this topic to be actually one thing that I believe I might by no means understand. It kind of feels too complicated and extremely huge for me. I am having a look ahead for your next post, I¡¦ll attempt to get the dangle of it!
I¡¦ve been exploring for a little for any high-quality articles or blog posts on this kind of area . Exploring in Yahoo I eventually stumbled upon this site. Studying this info So i am satisfied to show that I have an incredibly excellent uncanny feeling I discovered just what I needed. I such a lot undoubtedly will make sure to do not put out of your mind this web site and give it a glance regularly.
Hi, i think that i saw you visited my web site thus i came to “return the favor”.I’m attempting to find things to enhance my site!I suppose its ok to use a few of your ideas!!
wonderful post, very informative. I’m wondering why the other specialists of this sector don’t notice this. You should continue your writing. I’m sure, you’ve a great readers’ base already!
I simply could not go away your website prior to suggesting that I extremely loved the usual info an individual provide for your visitors? Is gonna be again often in order to inspect new posts.
I think other web-site proprietors should take this site as an model, very clean and magnificent user genial style and design, as well as the content. You’re an expert in this topic!
Attractive section of content. I just stumbled upon your website and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I will be subscribing to your feeds and even I achievement you access consistently fast.
Hi my family member! I want to say that this article is awesome, nice written and include almost all important infos. I¡¦d like to look extra posts like this .
I¡¦ve recently started a blog, the information you offer on this web site has helped me greatly. Thanks for all of your time & work.
I really appreciate this post. I¡¦ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again
As a Newbie, I am constantly browsing online for articles that can be of assistance to me. Thank you
hey there and thank you for your information – I’ve definitely picked up something new from right here. I did however expertise some technical points using this web site, since I experienced to reload the web site many times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I am complaining, but slow loading instances times will very frequently affect your placement in google and could damage your high-quality score if advertising and marketing with Adwords. Anyway I’m adding this RSS to my e-mail and could look out for much more of your respective interesting content. Ensure that you update this again very soon..
I¡¦ve been exploring for a little bit for any high quality articles or weblog posts in this sort of house . Exploring in Yahoo I finally stumbled upon this website. Reading this info So i am satisfied to show that I’ve an incredibly good uncanny feeling I found out just what I needed. I so much unquestionably will make sure to do not disregard this site and provides it a look regularly.
I simply wished to appreciate you yet again. I’m not certain the things I could possibly have carried out without the methods shared by you about this industry. It actually was a real fearsome problem in my opinion, nevertheless coming across a skilled approach you treated the issue forced me to leap with joy. I’m happy for your support and thus trust you recognize what a powerful job you are putting in teaching many others with the aid of a blog. I’m certain you haven’t got to know any of us.
I’m still learning from you, as I’m improving myself. I definitely liked reading all that is written on your blog.Keep the tips coming. I loved it!
I am so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
I am regular visitor, how are you everybody? This piece of writing posted at this website
is really nice.
Hello! I’m at work browsing your blog from my new iphone 3gs!
Just wanted to say I love reading through your blog and look forward
to all your posts! Keep up the great work!
hi!,I really like your writing so so much! share we keep up a correspondence extra about your post on AOL? I require a specialist in this space to resolve my problem. Maybe that’s you! Looking ahead to peer you.
Very efficiently written story. It will be useful to everyone who employess it, as well as myself. Keep up the good work – i will definitely read more posts.
For the reason that the admin of this web
page is working, no uncertainty very quickly it will be well-known, due to its quality contents.
Valuable information. Lucky me I found your website accidentally, and I am surprised why this accident did not happened earlier! I bookmarked it.
You can definitely see your expertise in the work you write. The arena hopes for even more passionate writers such as you who are not afraid to say how they believe. Always go after your heart.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a bit, but other than that, this is magnificent blog. A great read. I will certainly be back.
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thank you again
I simply couldn’t go away your web site before suggesting that I extremely enjoyed the usual info a person provide for your guests? Is going to be again regularly in order to check out new posts.
Hi there friends, how is everything, and what you would like to say on the topic
of this piece of writing, in my view its truly remarkable
in favor of me.
I gotta bookmark this site it seems handy very beneficial
As soon as I detected this internet site I went on reddit to share some of the love with them.
I wish to voice my admiration for your kind-heartedness supporting men and women who must have guidance on this area of interest. Your special commitment to getting the solution up and down became extremely effective and have continually helped associates much like me to attain their targets. Your amazing insightful instruction means this much a person like me and especially to my office colleagues. Many thanks; from each one of us.
Hey there, You have done a great job. I will definitely digg it and personally recommend to my friends. I am confident they’ll be benefited from this site.
Heya i’m for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and aid others like you aided me.
I savour, cause I discovered just what I used to be taking a look for. You have ended my 4 day lengthy hunt! God Bless you man. Have a great day. Bye
Hi there, You’ve done a great job. I will definitely digg it and personally suggest to my
friends. I am confident they will be benefited from this website.
It¡¦s in reality a nice and helpful piece of info. I am happy that you shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
Whats Happening i am new to this, I stumbled upon this I have found It positively helpful and it has helped me out loads. I’m hoping to contribute & help other customers like its helped me. Good job.
There is clearly a bunch to identify about this. I believe you made certain good points in features also.
You made some good points there. I did a search on the issue and found most guys will agree with your site.
You could certainly see your expertise within the work you write. The sector hopes for even more passionate writers like you who aren’t afraid to mention how they believe. All the time go after your heart.
You have remarked very interesting points! ps decent website.
Real nice design and fantastic subject matter, very little else we require : D.
I view something really interesting about your website so I saved to favorites .
I’m not sure where you’re getting your info, but good topic. I needs to spend some time learning more or understanding more. Thanks for excellent info I was looking for this info for my mission.
Somebody necessarily help to make severely articles I might state. That is the first time I frequented your web page and so far? I amazed with the research you made to make this particular put up incredible. Excellent activity!
Great blog here! Also your web site lots up very fast! What web host are you using? Can I get your associate link for your host? I wish my website loaded up as fast as yours lol
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a bit, but other than that, this is magnificent blog. A great read. I’ll definitely be back.
Awsome site! I am loving it!! Will be back later to read some more. I am taking your feeds also
Somebody necessarily assist to make significantly articles I might state. That is the very first time I frequented your web page and thus far? I amazed with the research you made to make this particular put up extraordinary. Wonderful activity!
I’m not sure where you are getting your information, but great topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful info I was looking for this information for my mission.
What i do not realize is in fact how you are no longer actually much more smartly-appreciated than you may be now. You are so intelligent. You realize thus considerably relating to this matter, made me individually believe it from a lot of various angles. Its like men and women don’t seem to be interested except it is something to do with Lady gaga! Your own stuffs great. Always handle it up!
I loved as much as you will receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly very often inside case you shield this increase.
Wonderful site. Plenty of helpful information here. I¡¦m sending it to some buddies ans additionally sharing in delicious. And naturally, thank you on your effort!
I precisely desired to appreciate you once more. I am not sure what I might have made to happen without the actual solutions discussed by you directly on such a theme. It previously was the frustrating scenario in my view, nevertheless discovering this skilled technique you treated it forced me to weep over happiness. Extremely thankful for this advice and in addition hope that you are aware of a powerful job that you’re doing teaching many others thru your webblog. Most probably you’ve never got to know any of us.
As soon as I discovered this site I went on reddit to share some of the love with them.
I conceive you have observed some very interesting details , thankyou for the post.
Hi my loved one! I wish to say that this post is amazing, nice written and come with almost all important infos. I would like to see more posts like this.
Dead written content, Really enjoyed examining.
I like the valuable information you provide in your articles. I will bookmark your blog and check again here regularly. I’m quite sure I’ll learn many new stuff right here! Best of luck for the next!
Someone necessarily lend a hand to make seriously articles I would state. This is the first time I frequented your web page and to this point? I amazed with the research you made to make this actual submit amazing. Magnificent task!
I really like your writing style, excellent info , regards for posting : D.
I was just looking for this information for a while. After six hours of continuous Googleing, finally I got it in your site. I wonder what is the lack of Google strategy that do not rank this type of informative sites in top of the list. Generally the top websites are full of garbage.
I have been examinating out many of your posts and it’s pretty good stuff. I will definitely bookmark your website.
Hey There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and return to read more of your useful info. Thanks for the post. I will definitely comeback.
I savor, result in I discovered exactly what I used to be having a look for. You’ve ended my four day long hunt! God Bless you man. Have a nice day. Bye
I do accept as true with all the ideas you have offered on your post. They’re very convincing and will definitely work. Nonetheless, the posts are very short for newbies. Could you please extend them a bit from next time? Thank you for the post.
Excellent website. Lots of helpful info here. I am sending it to some buddies ans also sharing in delicious. And naturally, thank you in your sweat!
Normally I don’t learn post on blogs, however I would like to say that this write-up very pressured me to try and do it! Your writing style has been surprised me. Thank you, very nice post.
Very well written story. It will be supportive to anybody who usess it, including me. Keep doing what you are doing – for sure i will check out more posts.
Howdy! I could have sworn I’ve been to this web site before but after
looking at a few of the articles I realized it’s new to me.
Regardless, I’m definitely pleased I discovered it and I’ll be book-marking it and checking
back frequently!
I do accept as true with all the ideas you have offered for your post. They are very convincing and can definitely work. Nonetheless, the posts are very short for novices. May you please prolong them a bit from next time? Thank you for the post.
excellent submit, very informative. I ponder why the
other specialists of this sector do not notice this.
You should proceed your writing. I’m sure, you’ve a huge readers’ base already!
Good ¡V I should definitely pronounce, impressed with your website. I had no trouble navigating through all the tabs as well as related info ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your customer to communicate. Excellent task..
Some truly fantastic articles on this website , thankyou for contribution.
Hi, Neat post. There is a problem with your website in internet explorer, may check this¡K IE still is the marketplace leader and a huge section of people will miss your fantastic writing because of this problem.
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert that I get actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently rapidly.
Excellent read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch because I found it for him smile Thus let me rephrase that: Thanks for lunch!
Hello there, I discovered your website by the use of Google while searching for a comparable matter, your web site got here up, it seems great. I have bookmarked it in my google bookmarks.
I simply wanted to thank you so much all over again. I do not know what I would’ve created without the entire methods shared by you about my question. This was the fearsome scenario for me personally, but taking note of this expert form you solved it took me to weep over fulfillment. I’m just happier for your work and in addition believe you are aware of an amazing job you are accomplishing training people through a web site. More than likely you have never come across any of us.
Wow! This could be one particular of the most helpful blogs We have ever arrive across on this subject. Basically Wonderful. I am also an expert in this topic so I can understand your hard work.
I was reading through some of your posts on this website and I believe this website is very instructive! Keep posting.
Someone essentially help to make seriously posts I’d state. That is the first time I frequented your website page and to this point? I surprised with the analysis you made to make this particular submit extraordinary. Great process!
I really like your writing style, fantastic information, thankyou for posting : D.
Some genuinely wonderful articles on this site, regards for contribution. “My salad days, When I was green in judgment.” by William Shakespeare.
You are a very intelligent person!
Asking questions are in fact fastidious thing if you are not
understanding something totally, except this article offers fastidious understanding even.
There is perceptibly a bundle to identify about this. I assume you made some good points in features also.
I¡¦ll right away grasp your rss feed as I can’t find your e-mail subscription link or newsletter service. Do you’ve any? Please let me recognize so that I may just subscribe. Thanks.
F*ckin’ awesome things here. I am very satisfied to peer your article. Thanks a lot and i am having a look forward to contact you. Will you please drop me a e-mail?
I have been surfing online more than three hours today, yet I never found anything that grabbed my interest as much as this piece.
I loved as much as you will receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get bought an shakiness over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this increase.
You could certainly see your enthusiasm in the work you write. The arena hopes for more passionate writers like you who are not afraid to say how they believe. Always follow your heart. “The only way most people recognize their limits is by trespassing on them.” by Tom Morris.
Very interesting topic , thanks for posting . “To have a right to do a thing is not at all the same as to be right in doing it.” by G. K. Chesterton.
My coder is trying to convince me to move to .net from PHP. I have always disliked the idea because of the expenses. But he’s tryiong none the less. I’ve been using WordPress on numerous websites for about a year and am nervous about switching to another platform. I have heard great things about blogengine.net. Is there a way I can import all my wordpress posts into it? Any help would be really appreciated!
I saw a similar post on another website but the points were not as well articulated.
I like what you guys are up also. Such clever work and reporting! Keep up the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my web site 🙂
Valuable info. Fortunate me I found your web site accidentally, and I’m shocked why this accident did not took place in advance! I bookmarked it.
I will right away seize your rss feed as I can not in finding your e-mail subscription hyperlink or e-newsletter service. Do you have any? Kindly permit me recognize in order that I could subscribe. Thanks.
Hello There. I found your blog using msn. This is an extremely well written article. I’ll be sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll certainly return.
Wow! This can be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Great. I’m also a specialist in this topic so I can understand your effort.
We are a group of volunteers and opening a new scheme in our community. Your web site offered us with valuable info to work on. You’ve done a formidable job and our whole community will be thankful to you.
It’s a comprehensive, yet fast read.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a little bit, but instead of that, this is wonderful blog. A fantastic read. I will definitely be back.
Thank you so much for giving everyone remarkably nice chance to read from this blog. It really is so useful and as well , packed with a great time for me and my office friends to visit your website more than three times in a week to learn the latest stuff you will have. Not to mention, I’m just always astounded with the incredible suggestions served by you. Some two facts in this posting are without a doubt the most efficient we’ve ever had.
Good day very nice web site!! Guy .. Excellent .. Superb .. I’ll bookmark your site and take the feeds also…I’m satisfied to seek out numerous helpful information here in the submit, we’d like develop more strategies on this regard, thank you for sharing.
This is really interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your fantastic post. Also, I’ve shared your website in my social networks!
I have been browsing online more than 3 hours lately, but I by no means discovered any fascinating article like yours. It is lovely value enough for me. In my view, if all web owners and bloggers made good content as you probably did, the web shall be a lot more useful than ever before.
Thank you for the sensible critique. Me and my neighbor were just preparing to do some research on this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such fantastic info being shared freely out there.
My wife and i have been absolutely lucky Jordan managed to finish up his web research because of the precious recommendations he made out of your site. It is now and again perplexing to just happen to be giving away tips and hints which often people may have been making money from. So we already know we have the writer to give thanks to for that. The specific illustrations you’ve made, the straightforward web site navigation, the relationships you assist to engender – it’s mostly sensational, and it’s really facilitating our son and the family understand the theme is exciting, which is highly indispensable. Many thanks for all!
Helpful info. Lucky me I found your web site by chance, and I am stunned why this twist of fate didn’t came about earlier! I bookmarked it.
I get pleasure from, lead to I discovered just what I was having a look for. You have ended my four day long hunt! God Bless you man. Have a nice day. Bye
Hello very cool web site!! Guy .. Excellent .. Amazing .. I will bookmark your web site and take the feeds also…I am satisfied to seek out so many useful information right here in the publish, we need work out extra techniques in this regard, thanks for sharing.
Wow! This can be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Excellent. I’m also an expert in this topic so I can understand your effort.
Heya i am for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you helped me.
Its good as your other posts : D, appreciate it for posting . “Reason is the substance of the universe. The design of the world is absolutely rational.” by Georg Wilhelm Friedrich Hegel.
I am regular readervisitor, how are you everybody? This articlepostpiece of writingparagraph posted at this websiteweb sitesiteweb page is reallyactuallyin facttrulygenuinely nicepleasantgoodfastidious.
I genuinely enjoy examining on this internet site, it has wonderful content. “Don’t put too fine a point to your wit for fear it should get blunted.” by Miguel de Cervantes.
I have recently started a web site, the info you offer on this site has helped me tremendously. Thanks for all of your time & work.
Thanks for the suggestions you reveal through this blog. In addition, many young women that become pregnant will not even try and get medical insurance because they are full of fearfulness they wouldn’t qualify. Although many states now require that insurers supply coverage irrespective of the pre-existing conditions. Prices on these kinds of guaranteed programs are usually higher, but when thinking about the high cost of medical treatment it may be any safer strategy to use to protect your own financial potential.
I think other web site proprietors should take this website as an model, very clean and great user friendly style and design, as well as the content. You’re an expert in this topic!
I’ve been surfing on-line greater than 3 hours lately, yet I never discovered any fascinating article like yours. It¡¦s pretty price enough for me. In my opinion, if all webmasters and bloggers made just right content material as you probably did, the net can be a lot more helpful than ever before.
Hello there, I found your site by the use of Google even as looking for a related topic, your web site got here up, it appears great. I have bookmarked it in my google bookmarks.
Very nice post. I just stumbled upon your blog and wanted to say that I’ve truly enjoyed browsing your blog posts. After all I’ll be subscribing to your feed and I hope you write again very soon!
I¡¦ll right away grasp your rss as I can not in finding your email subscription hyperlink or newsletter service. Do you have any? Please permit me understand so that I may just subscribe. Thanks.
I would like to thnkx for the efforts you’ve put in writing this website. I’m hoping the same high-grade site post from you in the upcoming also. Actually your creative writing abilities has inspired me to get my own web site now. Actually the blogging is spreading its wings quickly. Your write up is a good example of it.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
hey there and thank you for your information – I’ve certainly picked up anything new from right here. I did however expertise some technical points using this web site, since I experienced to reload the web site a lot of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I am complaining, but slow loading instances times will often affect your placement in google and could damage your high quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my e-mail and can look out for much more of your respective intriguing content. Make sure you update this again soon..
Great blog here! Also your website loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
PrettyVery nice post. I just stumbled upon your blogweblog and wantedwished to say that I haveI’ve reallytruly enjoyed browsingsurfing around your blog posts. In any caseAfter all I’llI will be subscribing to your feedrss feed and I hope you write again soonvery soon!
great points altogether, you just won a brand new reader. What might you suggest about your submit that you just made some days ago? Any sure?
Thank you for any other informative web site. The place else may I am getting that kind of info written in such a perfect way? I have a undertaking that I am just now operating on, and I’ve been at the look out for such information.
Thanks , I have recently been looking for info about this subject for a while and yours is the greatest I have found out till now. But, what about the bottom line? Are you certain about the supply?
Nice post. I was checking continuously this blog and I am impressed! Very helpful information specifically the last part 🙂 I care for such info much. I was looking for this certain info for a long time. Thank you and best of luck.
Hi there, just became alert to your blog through Google, and found that it’s really informative. I’m going to watch out for brussels. I will be grateful if you continue this in future. Numerous people will be benefited from your writing. Cheers!
hello there and thank you for your info – I’ve definitely picked up anything new from right here. I did however expertise several technical points using this site, as I experienced to reload the site a lot of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I am complaining, but slow loading instances times will often affect your placement in google and can damage your high quality score if advertising and marketing with Adwords. Anyway I am adding this RSS to my e-mail and can look out for much more of your respective fascinating content. Make sure you update this again very soon..
Hello, i think that i saw you visited my site so i came to “return the favor”.I am attempting to find things to improve my website!I suppose its ok to use a few of your ideas!!
I was recommended this website by my cousin. I am not sure whether this post is written by him as nobody else know such detailed about my problem. You are wonderful! Thanks!
I would like toI mustI’d like toI have to thank you for the efforts you haveyou’ve put in writing thispenning this blogwebsitesite. I am hopingI’m hopingI really hope to seeto viewto check out the same high-grade blog postscontent from youby you in the futurelater on as well. In factIn truth, your creative writing abilities has inspiredmotivatedencouraged me to get my ownmy very ownmy own, personal blogwebsitesite now 😉
Hey, you used to write magnificent, but the last few posts have been kinda boring¡K I miss your tremendous writings. Past several posts are just a little out of track! come on!
I really wanted to compose a quick note in order to appreciate you for some of the splendid secrets you are giving out on this site. My rather long internet research has at the end of the day been paid with excellent suggestions to talk about with my family. I would mention that we website visitors actually are rather endowed to dwell in a remarkable network with so many awesome people with insightful suggestions. I feel somewhat privileged to have come across your webpages and look forward to really more exciting times reading here. Thank you once again for a lot of things.
Hi would you mind stating which blog platform you’re working with? I’m planning to start my own blog in the near future but I’m having a difficult time deciding between BlogEngine/Wordpress/B2evolution and Drupal. The reason I ask is because your design and style seems different then most blogs and I’m looking for something completely unique. P.S Sorry for being off-topic but I had to ask!
Merely a smiling visitant here to share the love (:, btw outstanding design and style .
I haven’t checked in here for a while since I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
Simply wanna admit that this is very helpful , Thanks for taking your time to write this.
I haven’t checked in here for a while as I thought it was getting boring, but the last several posts are great quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
Thanks , I’ve recently been looking for info about this topic for a while and yours is the best I’ve came upon till now. But, what concerning the bottom line? Are you positive concerning the source?
Heya i’mi am for the primarythe first time here. I came acrossfound this board and I in findingfindto find It trulyreally usefulhelpful & it helped me out a lotmuch. I am hopingI hopeI’m hoping to giveto offerto provideto present somethingone thing backagain and helpaid others like yousuch as you helpedaided me.
Hello, Neat post. There is a problem with your website in internet explorer, could test this¡K IE nonetheless is the marketplace chief and a huge part of other people will pass over your wonderful writing due to this problem.
I’m still learning from you, but I’m making my way to the top as well. I definitely love reading all that is posted on your website.Keep the information coming. I liked it!
You could definitely see your skills within the work you write. The sector hopes for more passionate writers such as you who aren’t afraid to mention how they believe. Always go after your heart.
Magnificent beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog site? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
As a Newbie, I am permanently browsing online for articles that can benefit me. Thank you
I have not checked in here for some time as I thought it was getting boring, but the last several posts are good quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
Hey, you used to write great, but the last few posts have been kinda boring… I miss your super writings. Past several posts are just a bit out of track! come on!
Hi, i think that i saw you visited my weblog thus i came to “return the favor”.I am attempting to find things to enhance my website!I suppose its ok to use a few of your ideas!!
As a Newbie, I am continuously browsing online for articles that can aid me. Thank you
Thanks a bunch for sharing this with all of us you actually know what you’re speaking approximately! Bookmarked. Please also seek advice from my web site =). We may have a link alternate contract among us!
Simply want to say your article is as amazing. The clarity in your post is simply excellent and i can assume you are an expert on this subject. Well with your permission let me to grab your feed to keep updated with forthcoming post. Thanks a million and please continue the rewarding work.
Wow, wonderful blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is wonderful, let alone the content!
I like the valuablehelpful informationinfo you provide in your articles. I willI’ll bookmark your weblogblog and check again here frequentlyregularly. I amI’m quite certainsure I willI’ll learn lots ofmanya lot ofplenty ofmany new stuff right here! Good luckBest of luck for the next!
you’re really a just right webmaster. The site loading velocity is amazing. It sort of feels that you’re doing any distinctive trick. Also, The contents are masterpiece. you have done a wonderful task on this topic!
I¡¦ve recently started a blog, the info you provide on this website has helped me greatly. Thanks for all of your time & work.
You could definitely see your enthusiasm in the paintings you write. The world hopes for even more passionate writers like you who are not afraid to say how they believe. Always follow your heart.
Hello There. I found your blog using msn. This is a really well written article. I’ll make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I’ll definitely return.
You can definitely see your skills within the paintings you write. The world hopes for more passionate writers such as you who aren’t afraid to mention how they believe. All the time follow your heart.
I have learn a few excellent stuff here. Definitely price bookmarking for revisiting. I surprise how so much attempt you place to make this kind of magnificent informative web site.
Only a smiling visitor here to share the love (:, btw outstanding style and design .
My wife and i were very satisfied that Raymond managed to do his web research by way of the precious recommendations he came across through your web page. It’s not at all simplistic to just happen to be giving freely hints which usually people today might have been selling. We keep in mind we need you to be grateful to because of that. Those illustrations you’ve made, the straightforward web site menu, the relationships you assist to promote – it’s got many superb, and it’s leading our son and our family do think this theme is entertaining, and that is pretty fundamental. Thanks for all!
I have been browsing online greater than 3 hours nowadays, yet I by no means found any fascinating article like yours. It is lovely price sufficient for me. In my view, if all website owners and bloggers made excellent content material as you probably did, the web might be a lot more useful than ever before.
Wow, amazing blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your web site is fantastic, as well as the content!
Excellent website. Plenty of useful information here. I¡¦m sending it to some pals ans also sharing in delicious. And of course, thanks in your effort!
I truly appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thx again!
I like the valuable info you provide in your articles. I’ll bookmark your blog and check again here regularly. I am quite sure I’ll learn many new stuff right here! Good luck for the next!
Hi thereHello, I enjoy reading all ofthrough your articlepostarticle post. I likewanted to write a little comment to support you.
Normally I don’t read article on blogs, but I wish to say that this write-up very forced me to check out and do so! Your writing style has been surprised me. Thanks, very nice article.
You made some nice points there. I looked on the internet for the issue and found most persons will agree with your site.
You made some clear points there. I looked on the internet for the subject and found most persons will go along with with your site.
Thank you for some other wonderful article. The place else could anybody get that type of information in such an ideal way of writing? I have a presentation subsequent week, and I’m at the look for such info.
I wanted to write down a quick comment in order to express gratitude to you for some of the nice guides you are posting here. My particularly long internet search has at the end been honored with professional details to go over with my friends and family. I ‘d repeat that most of us website visitors are rather blessed to live in a perfect place with very many outstanding professionals with good plans. I feel very privileged to have used your entire webpages and look forward to tons of more pleasurable times reading here. Thanks once more for all the details.
certainly like your website but you need to test the spelling on quite a few of your posts. A number of them are rife with spelling issues and I to find it very bothersome to inform the reality on the other hand I will definitely come again again.
I have not checked in here for some time because I thought it was getting boring, but the last few posts are good quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
I really appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thx again!
you’re really a good webmaster. The website loading speed is incredible. It seems that you’re doing any unique trick. Also, The contents are masterwork. you’ve done a fantastic process in this topic!
I’m not sure where you are getting your information, but great topic. I needs to spend some time learning much more or understanding more. Thanks for excellent info I was looking for this information for my mission.
I’ve been absent for a while, but now I remember why I used to love this web site. Thanks , I¡¦ll try and check back more frequently. How frequently you update your site?
Hi my family member! I want to say that this post is amazing, great written and include almost all significant infos. I would like to look more posts like this .
I’ve been browsing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the net will be much more useful than ever before.
I¡¦ve been exploring for a little bit for any high-quality articles or weblog posts in this sort of space . Exploring in Yahoo I finally stumbled upon this site. Reading this info So i am satisfied to express that I have a very good uncanny feeling I came upon just what I needed. I such a lot for sure will make sure to don¡¦t overlook this site and give it a glance regularly.
Definitely, what a fantastic blog and revealing posts, I definitely will bookmark your website.Have an awsome day!
I have been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the net will be much more useful than ever before.
Valuable information. Fortunate me I found your web site accidentally, and I’m stunned why this twist of fate did not took place earlier! I bookmarked it.
Just want to say your article is as surprising. The clearness in your post is just nice and i could assume you’re an expert on this subject. Fine with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please continue the enjoyable work.
This is my first time go to see at here and i am truly happy to read all at single place.
I carry on listening to the news talk about getting boundless online grant applications so I have been looking around for the top site to get one. Could you advise me please, where could i acquire some?
Hello, i think that i saw you visited my web site thus i came to “return the favor”.I am trying to find things to enhance my website!I suppose its ok to use some of your ideas!!
I don’t even know how I ended up here, but I thought this post was good. I do not know who you are but definitely you are going to a famous blogger if you are not already 😉 Cheers!
I want to express thanks to this writer for rescuing me from such a issue. After researching throughout the the web and meeting concepts which are not beneficial, I figured my entire life was well over. Living without the strategies to the problems you have resolved by means of your main write-up is a serious case, as well as ones that would have adversely affected my entire career if I hadn’t come across the blog. Your actual know-how and kindness in maneuvering a lot of things was priceless. I’m not sure what I would have done if I had not discovered such a step like this. I can also at this point look ahead to my future. Thanks for your time so much for your high quality and amazing guide. I won’t think twice to refer your web page to any individual who needs guide about this subject.
I dont think I’ve read anything like this before. So good to find somebody with some original thoughts on this subject. cheers for starting this up. This blog is something that is needed on the web, someone with a little originality.
Hello there, You have done an incredible job. I will certainly digg it and personally suggest to my friends. I’m sure they will be benefited from this web site.
A colleague in the field told me to check out your website.
Whats up very nice website!! Guy .. Beautiful .. Superb .. I’ll bookmark your site and take the feeds also…I’m happy to find so many helpful info here within the post, we need work out more techniques in this regard, thank you for sharing.
Great – I should certainly pronounce, impressed with your site. I had no trouble navigating through all the tabs and related info ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your client to communicate. Nice task.
Bonjour ! Pourquoi un site comme ca ? :p
Good write-up, I am regular visitor of one¡¦s site, maintain up the excellent operate, and It’s going to be a regular visitor for a long time.
I do trust all the ideas you have offered in your post. They’re very convincing and will definitely work. Nonetheless, the posts are very short for beginners. May just you please extend them a bit from subsequent time? Thanks for the post.
Well I definitely enjoyed studying it. This tip provided by you is very helpful for proper planning.
A person necessarily lend a hand to make severely posts I would state. This is the first time I frequented your website page and to this point? I surprised with the research you made to create this particular publish amazing. Excellent task!
My wife and i have been now peaceful Peter managed to complete his investigations from the ideas he obtained out of the web site. It is now and again perplexing just to choose to be giving freely tips and tricks which a number of people have been selling. And we all keep in mind we need the website owner to appreciate for this. All of the illustrations you’ve made, the straightforward blog menu, the friendships you help to promote – it’s all amazing, and it’s facilitating our son in addition to the family feel that this content is interesting, which is extraordinarily essential. Thank you for the whole thing!
Well I sincerely liked reading it. This article procured by you is very helpful for good planning.
Very nice post. I just stumbled upon your weblog and wished to say that I have really enjoyed browsing your blog posts. In any case I’ll be subscribing to your feed and I hope you write again very soon!
Hello.This post was really fascinating, particularly because I was browsing for thoughts on this subject last Thursday.
Pretty section of content. I just stumbled upon your blog and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I’ll be subscribing to your feeds and even I achievement you access consistently fast.
Wonderful work! That is the type of info that are meant to be shared across the web. Shame on the seek engines for now not positioning this put up upper! Come on over and talk over with my web site . Thank you =)
Very nice post. I just stumbled upon your weblog and wished to say that I’ve really enjoyed browsing your blog posts. After all I will be subscribing to your feed and I hope you write again soon!
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thank you again
I really enjoy reading on this website , it has fantastic articles . “One doesn’t discover new lands without consenting to lose sight of the shore for a very long time.” by Andre Gide.
I was just searching for this info for a while. After six hours of continuous Googleing, finally I got it in your web site. I wonder what’s the lack of Google strategy that don’t rank this type of informative web sites in top of the list. Generally the top sites are full of garbage.
I’m very happy to read this. This is the kind of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this best doc.
I am continually searching online for ideas that can assist me. Thanks!
Magnificent beat ! I would like to apprentice while you amend your website, how could i subscribe for a blog web site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
Great blog! Is your theme custom made or did you download it
from somewhere? A design like yours with a few simple adjustements
would really make my blog jump out. Please let me know where you got your theme.
Bless you
Stunning story there. What occurred after? Take care!
I like the helpful information you provide in your articles.
I will bookmark your weblog and check again here frequently.
I’m quite certain I will learn many new stuff right here!
Good luck for the next!
Woah! I’m really loving the template/theme of this site.
It’s simple, yet effective. A lot of times it’s difficult to get that “perfect balance” between user friendliness and
visual appeal. I must say you’ve done a very good job with this.
Also, the blog loads very fast for me on Firefox. Excellent Blog!
I¡¦ve recently started a blog, the info you offer on this site has helped me tremendously. Thanks for all of your time & work.
Definitely intriguing highlights you’ll have mentioned, thanks for setting up.
It truly is almost not possible to find well-qualified users on this area, fortunately you look like you fully grasp what exactly you’re writing on! Excellent
Fantastic goods from you, man. I have understand your stuff previous to and you’re just extremely wonderful. I actually like what you’ve acquired here, really like what you are saying and the way in which you say it. You make it enjoyable and you still take care of to keep it sensible. I can’t wait to read far more from you. This is really a great website.
whoah this blog is great i like reading your articles. Stay up the great paintings! You recognize, lots of individuals are searching round for this information, you can aid them greatly.
Pretty portion of content. I just stumbled upon your web site and in accession capital to claim that I get
actually loved account your blog posts. Anyway I’ll be subscribing to your feeds and
even I success you get entry to consistently quickly.
Easily, the post is really the greatest on this laudable topic. I concur with your conclusions and will thirstily look forward to your future updates. Saying thank will not just be sufficient, for the wonderful c lucidity in your writing. I will instantly grab your rss feed to stay privy of any updates. Solid work and much success in your business enterprise!
Good points – – it will make a difference with my parents.
What i do not understood is in truth how you’re not actually much more neatly-preferred than you may be right now. You are very intelligent. You understand therefore considerably relating to this topic, produced me in my view imagine it from so many numerous angles. Its like women and men don’t seem to be interested until it is something to accomplish with Lady gaga! Your own stuffs outstanding. At all times handle it up!
This will be helpful for my family.
I am actually delighted to read this web site posts which contains plenty of valuable data,
thanks for providing these kinds of information.
Seriously compelling information that you have stated, a big heads up for submitting.
It truly is almost close to impossible to encounter well-updated americans on this subject, however you come across as like you are familiar with what you’re writing about! Thanks
I like to spend my free time by scaning various internet recourses. Today I came across your site and I found it is as one of the best free resources available! Well done! Keep on this quality!
Social marketing I was recommended this web site by my cousin. I am not sure whether this post is written by him as no one else know such detailed about my difficulty. You’re incredible! Thanks!
You’ll find it almost close to impossible to encounter well-informed americans on this matter, however, you come across as like you understand the things that you’re writing about! Thank You
Good job for bringing something important to the internet!
It’s near unthinkable to come across well-qualified viewers on this niche, and yet you seem like you fully grasp whatever you’re preaching about! Excellent
Really appreciate you sharing this blog article.Really thank you! Great.
However, it is virtually all done with tongues rooted solidly in cheeks, and everyone has absolutely nothing but absolutely love for his or her friendly neighborhood scapegoat. The truth is, he is not just a pushover. He is basically that special variety of person strong enough to take all of that good natured ribbing for exactly what it is.
Exceedingly engaging elements that you have stated, thanks a lot for publishing.
I love the efforts you have put in this, regards for all the great posts.
I like this post, enjoyed this one thankyou for putting up.
I merely hope to tell you that I am new to wordpress blogging and pretty much cherished your page. More than likely I am likely to save your blog post . You undoubtedly have excellent article blog posts. Get Pleasure From it for giving out with us all of your blog write-up
I am very happy to read this. This is the type of manual that needs to be given and not the random misinformation that is at the other blogs. Appreciate your sharing this best doc.
Wow! This can be one particular of the most helpful blogs We’ve ever arrive across on this subject. Actually Excellent. I am also an expert in this topic so I can understand your effort.
You can definitely see your expertise in the paintings you write. The arena hopes for even more passionate writers like you who are not afraid to mention how they believe. Always go after your heart. “What power has law where only money rules.” by Gaius Petronius.
I appreciate, cause I found exactly what I used to be taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a great day. Bye
I really wish to tell you that I am new to blogging and utterly valued your article. More than likely I am going to save your blog post . You simply have impressive article information. Value it for giving out with us your current internet site post
Unbelievably entertaining points you’ll have stated, thank you so much for publishing.
I got what you intend, regards for putting up.Woh I am delighted to find this website through google. “If one does not know to which port one is sailing, no wind is favorable.” by Seneca.
You’ll find it almost not possible to find well-aware viewers on this niche, yet somehow you come across as like you understand the things you’re posting on! Gratitude
I would like to get across my love for your kind-heartedness in support of men and women that absolutely need help with the field. Your personal dedication to passing the solution across became extremely beneficial and have all the time permitted some individuals like me to reach their endeavors. Your own useful recommendations implies much to me and far more to my mates. Many thanks; from all of us.
Great write-up, I am regular visitor of one’s website, maintain up the excellent operate, and It’s going to be a regular visitor for a lengthy time.
Highly motivating points you’ll have mentioned, thanks a lot for posting.
It’s near unattainable to come across well-advised women and men on this matter, still you look like you are familiar with which you’re talking about! Regards
Really alluring data that you have mentioned, thanks so much for posting.
I just wish to tell you that I am new to blog posting and completely valued your webpage. More than likely I am prone to store your blog post . You truly have extraordinary article material. Be Thankful For it for share-out with us your own site document
It really is near impossible to come across well-qualified women and men on this area, regrettably you appear like you fully grasp what exactly you’re posting on! Thank You
Might be near close to impossible to encounter well-informed visitors on this matter, however you seem like you fully grasp those things you’re preaching about! Thanks A Lot
I like what you guys are up also. Such clever work and reporting! Keep up the excellent works guys I¡¦ve incorporated you guys to my blogroll. I think it will improve the value of my site 🙂
A person necessarily assist to make significantly posts I would state. That is the first time I frequented your website page and up to now? I surprised with the research you made to make this actual put up amazing. Wonderful job!
My relatives always say that I am killing my time here at net, but I know I am getting knowledge
daily by reading thes good articles.
Hello. Great job. I did not expect this. This is a remarkable story. Thanks!
A person essentially lend a hand to make seriously articles I might state. This is the very first time I frequented your web page and so far? I surprised with the analysis you made to create this particular put up incredible. Excellent task!
It’s the best time to make some plans for the future and it’s time to be happy. I’ve read this post and if I could I wish to suggest you some interesting things or tips. Perhaps you could write next articles referring to this article. I desire to read even more things about it!
My wife and i have been so joyous that Peter could do his researching with the ideas he discovered through the web page. It is now and again perplexing to simply possibly be releasing key points which most people might have been making money from. And we also grasp we’ve got the blog owner to appreciate because of that. The main explanations you made, the easy website menu, the friendships you will give support to engender – it’s everything sensational, and it’s leading our son and us reckon that this subject matter is amusing, and that is exceptionally fundamental. Many thanks for the whole thing!
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again
Keep up the excellent piece of work, I read few blog posts on this site and I believe that your blog is very interesting and has got lots of good information.
Remarkably engaging information you’ll have mentioned, thanks a lot for setting up.
I just wish to tell you that I am new to putting up a blog and thoroughly liked your post. Quite possibly I am probably to remember your blog post . You indeed have memorable article information. Be Grateful For it for telling with us all of your url document
Unquestionably believe that which you said. Your favorite justification seemed to be on the web the simplest thing to be aware of. I say to you, I definitely get irked while people think about worries that they plainly do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
I went over this web site and I think you have a lot of great info, saved to fav (:.
Hello.This article was really motivating, especially since I was looking for thoughts on this subject last Thursday.
I precisely wished to say thanks yet again. I do not know the things that I might have sorted out in the absence of those recommendations contributed by you over that theme. It became a frightful difficulty in my position, but noticing the very specialized style you processed the issue made me to jump over gladness. Now i am grateful for the assistance and then expect you know what an amazing job you’re putting in teaching most people by way of your webpage. I am sure you’ve never come across all of us.
I relish, lead to I found just what I was having a look for. You have ended my four day long hunt! God Bless you man. Have a nice day. Bye
I¡¦ve been exploring for a bit for any high quality articles or blog posts on this sort of space . Exploring in Yahoo I eventually stumbled upon this web site. Reading this info So i¡¦m glad to express that I’ve an incredibly just right uncanny feeling I discovered exactly what I needed. I most indubitably will make certain to do not overlook this website and provides it a glance regularly.
I’m not sure where you are getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for fantastic information I was looking for this info for my mission.
I in addition to my buddies have been taking note of the good secrets and techniques on the website and then instantly got an awful feeling I had not expressed respect to the web blog owner for those techniques. The young boys ended up very interested to read all of them and have in fact been taking advantage of those things. Thanks for indeed being quite helpful and also for getting varieties of high-quality tips millions of individuals are really wanting to know about. My personal honest regret for not saying thanks to you sooner.
I precisely needed to say thanks once more. I am not sure what I could possibly have gone through in the absence of the tips and hints discussed by you over my industry. It absolutely was an absolute frightening problem in my view, however , observing a new skilled strategy you resolved it took me to leap for joy. I’m happier for your work and wish you really know what a great job you’re doing teaching people by way of your website. I’m certain you’ve never got to know all of us.
I am really sure now is the time to investin Bitcoin. The swings in the Bitcoin market place have been quite extreme recently but the movement is decisively up. The projections give a clear sign that now is the time totransfer currency into Bitcoin. Signs are the same as when BTC was only a few dollars in value. Really different than the few thousand that it is at the moment. Don’t Get into Bitcoin now. Don’t be sorry later.
This is really interesting, You’re a very skilled blogger. I have joined your rss feed and look forward to seeking more of your magnificent post. Also, I have shared your site in my social networks!
Wow! This could be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Actually Magnificent. I’m also a specialist in this topic therefore I can understand your effort.
F*ckin’ tremendous things here. I’m very satisfied to see your article. Thanks a lot and i am taking a look ahead to touch you. Will you kindly drop me a e-mail?
But wanna input on few general things, The website design and style is perfect, the content material is very great. “Believe those who are seeking the truth. Doubt those who find it.” by Andre Gide.
greatwonderfulfantasticmagnificentexcellent issuespoints altogether, you justsimply wongainedreceived a logoemblembrand newa new reader. What maymightcouldwould you suggestrecommend in regards toabout your postsubmitpublishput up that youthat you simplythat you just made a fewsome days agoin the past? Any surepositivecertain?
Wow! This blog looks just like my old one! It’s on a completely different topic but it has pretty much the same layout and design. Excellent choice of colors!
obviously like your website however you need to check the spelling on quite a few of your posts. A number of them are rife with spelling issues and I find it very bothersome to tell the truth however I¡¦ll definitely come back again.
Hi my family member! I want to say that this article is amazing, great written and include approximately all important infos. I’d like to see more posts like this .
I have not checked in here for a while as I thought it was getting boring, but the last several posts are good quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
Dead written subject matter, thanks for information. “Necessity is the mother of taking chances.” by Mark Twain.
We’re a group of volunteers and opening a new scheme in our community. Your web site provided us with valuable information to work on. You have done a formidable job and our entire community will be grateful to you.
But wanna remark on few general things, The website layout is perfect, the content material is rattling good : D.
certainly like your web-site but you need to check the spelling on several of your posts. Many of them are rife with spelling problems and I find it very troublesome to inform the reality nevertheless I’ll surely come back again.
hello!,I like your writing so much! percentage we keep up a correspondence more approximately your post on AOL? I need an expert in this space to resolve my problem. May be that’s you! Looking ahead to look you.
As I web site possessor I believe the content material here is rattling wonderful , appreciate it for your efforts. You should keep it up forever! Best of luck.
Just want to say what a great blog you got here!I’ve been around for quite a lot of time, but finally decided to show my appreciation of your work!
Excellent weblog right here! Additionally your site a lot up very fast! What host are you the usage of? Can I am getting your associate hyperlink for your host? I wish my web site loaded up as fast as yours lol
I found your weblog website on google and examine a few of your early posts. Proceed to keep up the superb operate. I simply further up your RSS feed to my MSN Information Reader. Looking for ahead to studying extra from you afterward!…
Nice read, I just passed this onto a colleague who was doing a little research on that. And he just bought me lunch since I found it for him smile Therefore let me rephrase that: Thanks for lunch!
I simply had to say thanks once again. I am not sure the things I would have accomplished in the absence of those thoughts documented by you regarding that subject. This was a intimidating case in my position, but encountering the very skilled fashion you processed it forced me to weep with joy. I will be happy for this assistance and as well , sincerely hope you comprehend what a great job that you are accomplishing teaching other individuals via your blog. Most probably you have never met any of us.
I appreciate, result in I found exactly what I used to be having a look for. You’ve ended my 4 day lengthy hunt! God Bless you man. Have a great day. Bye
I truly enjoy looking through on this site, it holds excellent articles . “The great secret of power is never to will to do more than you can accomplish.” by Henrik Ibsen.
Very interesting subject, thank you for posting.
Merely wanna remark on few general things, The website design is perfect, the articles is really great. “The idea of God is the sole wrong for which I cannot forgive mankind.” by Marquis de Sade.
Enjoyed reading through this, very good stuff, thankyou . “It requires more courage to suffer than to die.” by Napoleon Bonaparte.
Great site! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
Great remarkable issues here. I¡¦m very happy to peer your post. Thanks so much and i am having a look forward to contact you. Will you kindly drop me a mail?
As I web site possessor I believe the content matter here is rattling fantastic , appreciate it for your efforts. You should keep it up forever! Good Luck.
Keep working ,terrific job!
Excellent read, I just passed this onto a colleague who was doing some research on that. And he just bought me lunch as I found it for him smile So let me rephrase that: Thanks for lunch!
I must express appreciation to you just for bailing me out of this type of incident. Just after surfing throughout the world-wide-web and coming across solutions that were not helpful, I believed my entire life was well over. Living without the approaches to the issues you’ve solved all through your entire short post is a crucial case, and ones which may have badly affected my career if I hadn’t encountered the website. Your knowledge and kindness in touching all the stuff was precious. I don’t know what I would’ve done if I had not discovered such a point like this. I am able to now relish my future. Thanks for your time very much for this expert and amazing help. I won’t hesitate to suggest your blog to anybody who wants and needs assistance about this topic.
Only a smiling visitor here to share the love (:, btw great layout. “Everything should be made as simple as possible, but not one bit simpler.” by Albert Einstein.
Wow, marvelous weblog layout! How long have you been running a blog for? you made blogging glance easy. The whole look of your web site is excellent, as well as the content material!
My wife and i have been very ecstatic Chris could deal with his research via the precious recommendations he acquired out of the weblog. It’s not at all simplistic to simply continually be giving away helpful hints which often others have been trying to sell. And we also take into account we need you to thank for that. All of the illustrations you have made, the simple site menu, the friendships your site give support to foster – it’s got all awesome, and it’s letting our son in addition to our family consider that that subject is enjoyable, which is certainly really serious. Thanks for the whole thing!
I am not sure where you’re getting your information, but good topic. I needs to spend some time learning more or understanding more. Thanks for fantastic information I was looking for this info for my mission.
fantastic points altogether, you just won a new reader. What might you recommend in regards to your post that you simply made a few days in the past? Any positive?
I am always invstigating online for articles that can aid me. Thx!
You are my inhalation , I possess few blogs and rarely run out from to brand.
I got what you mean , appreciate it for posting .Woh I am delighted to find this website through google. “Those who corrupt the public mind are just as evil as those who steal from the public.” by Theodor Wiesengrund Adorno.
I really like your writing style, great information, appreciate it for putting up :D. “Nothing sets a person so much out of the devil’s reach as humility.” by Johathan Edwards.
But wanna input that you have a very decent site, I like the design and style it actually stands out.
Very interesting details you have remarked, appreciate it for putting up. “Curiosity is the key to creativity.” by Akio Morita.
Hello there, You’ve done an excellent job. I’ll certainly digg it and personally recommend to my friends. I am sure they’ll be benefited from this web site.
Fantastic web site. Lots of helpful info here. I am sending it to a few friends ans also sharing in delicious. And naturally, thank you in your effort!
I was just searching for this information for a while. After six hours of continuous Googleing, finally I got it in your website. I wonder what is the lack of Google strategy that don’t rank this kind of informative sites in top of the list. Usually the top sites are full of garbage.
I don’t even know how I ended up here, but I thought this post was good. I do not know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
Whats Going down i’m new to this, I stumbled upon this I have found It positively helpful and it has helped me out loads. I’m hoping to give a contribution & help other customers like its aided me. Great job.
Thank you for all of your labor on this site. My mom enjoys engaging in investigation and it’s really easy to understand why. Most of us hear all relating to the compelling means you produce important ideas via this website and in addition recommend response from other individuals about this topic while my simple princess is actually starting to learn so much. Take pleasure in the rest of the new year. You are always carrying out a very good job.
Hello, Neat post. There is a problem along with your web site in web explorer, may check this¡K IE nonetheless is the market chief and a huge part of other folks will miss your fantastic writing due to this problem.
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
I together with my buddies have been studying the excellent points located on your web page then immediately got an awful feeling I had not expressed respect to the blog owner for those techniques. All of the women had been for that reason warmed to study them and have now honestly been taking pleasure in these things. We appreciate you really being indeed kind and then for finding varieties of useful guides millions of individuals are really desperate to be aware of. My sincere apologies for not saying thanks to earlier.
Do you mind if I quote a couplefew of your postsarticles as long as I provide credit and sources back to your webpagesitewebsiteweblogblog? My blog sitewebsiteblog is in the very sameexact same area of interestniche as yours and my visitorsusers would certainlydefinitelygenuinelytrulyreally benefit from a lot of thesome of the information you presentprovide here. Please let me know if this alrightokayok with you. RegardsThanks a lotAppreciate itCheersThank youMany thanksThanks!
I really appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thx again!
I’ve been browsing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all webmasters and bloggers made good content as you did, the net will be a lot more useful than ever before.
I like what you guys are up also. Such intelligent work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my site :).
I have been surfing on-line more than 3 hours today, but I never discovered any fascinating article like yours. It is lovely value enough for me. Personally, if all webmasters and bloggers made just right content as you did, the web shall be much more helpful than ever before. “Revolution is not a onetime event.” by Audre Lorde.
Super-Duper blog! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
I think other site proprietors should take this site as an model, very clean and fantastic user friendly style and design, let alone the content. You’re an expert in this topic!
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you are going to a famous blogger if you aren’t already 😉 Cheers!
I have read several good stuff here. Certainly worth bookmarking for revisiting. I surprise how a lot attempt you place to create such a fantastic informative website.
I’m not sure where you’re getting your information, but good topic. I needs to spend some time learning more or understanding more. Thanks for excellent information I was looking for this information for my mission.
Excellent post. I was checking continuously this blog and I am impressed! Extremely helpful information specially the last part 🙂 I care for such information much. I was seeking this particular info for a very long time. Thank you and good luck.
I do accept as true with all of the ideas you have introduced to your post. They are really convincing and can definitely work. Still, the posts are too short for newbies. Could you please lengthen them a little from next time? Thank you for the post.
Super-Duper site! I am loving it!! Will come back again. I am bookmarking your feeds also
Hello. remarkable job. I did not imagine this. This is a fantastic story. Thanks!
Hello.This article was extremely remarkable, particularly because I was looking for thoughts on this topic last Tuesday.
I have been reading out a few of your posts and it’s clever stuff. I will surely bookmark your blog.
Good ¡V I should certainly pronounce, impressed with your website. I had no trouble navigating through all the tabs as well as related information ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your customer to communicate. Nice task..
Wonderful web site. Lots of helpful info here. I’m sending it to some friends ans also sharing in delicious. And naturally, thanks in your sweat!
Heya i’m for the first time here. I came across this board and I find It really useful & it helped me out much. I hope to give something back and help others like you aided me.
Hey There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll definitely return.
I have learned newer and more effective things from your blog post. One other thing to I have seen is that in most cases, FSBO sellers will certainly reject you actually. Remember, they’d prefer to not ever use your services. But if anyone maintain a stable, professional partnership, offering guide and being in contact for four to five weeks, you will usually manage to win a discussion. From there, a listing follows. Thanks
I like the helpful information you provide in your articles. I will bookmark your blog and check again here regularly. I’m quite certain I will learn many new stuff right here! Best of luck for the next!
Hello. Great job. I did not expect this. This is a remarkable story. Thanks!
I would like to thnkx for the efforts you’ve put in writing this website. I’m hoping the same high-grade website post from you in the upcoming as well. Actually your creative writing skills has inspired me to get my own site now. Actually the blogging is spreading its wings quickly. Your write up is a great example of it.
There is apparently a lot to realize about this. I assume you made various nice points in features also.
Definitely, what a fantastic website and educative posts, I will bookmark your site.All the Best!
I am only commenting to let you be aware of what a brilliant experience my child gained checking your web site. She came to understand plenty of things, which included what it is like to possess an ideal helping style to have other individuals with no trouble gain knowledge of several tricky topics. You undoubtedly did more than visitors’ expectations. Many thanks for churning out the necessary, dependable, informative and in addition easy tips about your topic to Kate.
Thank you for all of your efforts on this web site. Ellie loves getting into internet research and it’s simple to grasp why. Many of us know all relating to the dynamic means you create very helpful tips and tricks by means of this blog and even encourage contribution from other people about this idea plus our favorite child is now being taught a lot of things. Take pleasure in the rest of the year. Your doing a glorious job.
It’s hard to find well-informed people on this subject, but you sound like you know what you’re talking about! Thanks
You can certainly see your enthusiasm in the paintings you write. The world hopes for even more passionate writers like you who are not afraid to say how they believe. Always go after your heart. “Every man serves a useful purpose A miser, for example, makes a wonderful ancestor.” by Laurence J. Peter.
I savour, cause I discovered just what I was taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
Well I definitely liked reading it. This post offered by you is very helpful for proper planning.
Wonderful work! That is the kind of info that are supposed to be shared across the net. Disgrace on Google for not positioning this submit upper! Come on over and consult with my website . Thanks =)
I will immediately seize your rss as I can’t find your e-mail subscription link or e-newsletter service. Do you have any? Kindly let me recognise in order that I may subscribe. Thanks.
I truly appreciate this blog.
Some really choice content on this internet site , bookmarked .
Wow! This could be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Basically Fantastic. I’m also a specialist in this topic therefore I can understand your effort.
Hey, you used to write great, but the last few posts have been kinda boring… I miss your super writings. Past few posts are just a little bit out of track! come on!
I dugg some of you post as I thought they were extremely helpful very useful
I see something truly interesting about your weblog so I saved to fav.
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get bought an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly a lot often inside case you shield this hike.
You have brought up a very great details , regards for the post.
Some genuinely prize posts on this site, saved to fav.
whoah this blog is fantastic i like reading your articles. Stay up the good work! You understand, lots of individuals are looking around for this info, you could help them greatly.
Hello, i think that i saw you visited my weblog so i came to “return the favorâ€.I am trying to find things to enhance my website!I suppose its ok to use a few of your ideas!!
Hello. excellent job. I did not anticipate this. This is a remarkable story. Thanks!
wonderful submit, very informative. I wonder why the opposite experts of this sector don’t understand this. You should continue your writing. I’m confident, you have a huge readers’ base already!
I’m not sure where you are getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for excellent info I was looking for this info for my mission.
I have been browsing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my opinion, if all site owners and bloggers made good content as you did, the net will be much more useful than ever before.
This is very interesting, You’re a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your magnificent post. Also, I’ve shared your website in my social networks!
Heya i am for the first time here. I found this board and I find It really useful & it helped me out much. I hope to give something back and aid others like you helped me.
I dugg some of you post as I cerebrated they were very useful handy
Hi, I do believe this is an excellent web site. I stumbledupon it 😉 I’m going to revisit once again since I bookmarked it. Money and freedom is the best way to change, may you be rich and continue to help other people.
Wow! This could be one particular of the most useful blogs We have ever arrive across on this subject. Actually Excellent. I am also a specialist in this topic so I can understand your effort.
Hello. fantastic job. I did not anticipate this. This is a remarkable story. Thanks!
I really appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thank you again!
Wonderful web site. A lot of useful info here. I’m sending it to a few friends ans additionally sharing in delicious. And naturally, thanks in your sweat!
I simply could not leave your website prior to suggesting that I extremely loved the standard information an individual provide to your guests? Is going to be back continuously in order to inspect new posts
There is obviously a lot to know about this. I believe you made certain good points in features also.
I have been surfing online more than 3 hours as of late, yet I by no means discovered any attention-grabbing article like yours. It¡¦s beautiful price enough for me. Personally, if all site owners and bloggers made good content as you probably did, the web will be much more useful than ever before.
I really like your writing style, good information, thankyou for putting up : D.
great issues altogether, you simply won a new reader. What may you suggest about your put up that you simply made a few days in the past? Any certain?
Hi my loved one! I want to say that this post is amazing, great written and come with approximately all important infos. I¡¦d like to see more posts like this .
Way cool! Some extremely valid points! I appreciate you writing this write-up and also the rest of the website is extremely good.
Thanks for any other excellent post. The place else could anyone get that kind of info in such a perfect means of writing? I’ve a presentation subsequent week, and I’m at the search for such information.
Whats Taking place i am new to this, I stumbled upon this I’ve found It absolutely useful and it has aided me out loads. I hope to give a contribution & help different users like its helped me. Good job.
Lovely site! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
It is in point of fact a nice and useful piece of info. I¡¦m glad that you shared this useful information with us. Please keep us up to date like this. Thank you for sharing.
Awsome article and straight to the point. I don’t know if this is in fact the best place to ask but do you folks have any thoughts on where to hire some professional writers? Thx 🙂
How often will Facebook check for a new LiveJournal blog post to import to my notes?
I simply wished to thank you very much once again. I am not sure the things that I could possibly have taken care of without the entire aspects shown by you directly on such situation. It became a very daunting crisis in my position, but observing a new well-written way you treated that forced me to jump for gladness. Now i’m happier for the advice and thus believe you really know what a powerful job you’re doing instructing some other people thru your website. I’m certain you haven’t encountered all of us.
I think you have remarked some very interesting points , regards for the post.
Wow! Thank you! I constantly needed to write on my blog something like that. Can I include a part of your post to my website?
Hi, i think that i saw you visited my web site thus i came to “return the favor”.I’m attempting to find things to enhance my site!I suppose its ok to use a few of your ideas!!
I would like to thank you for the efforts you’ve put in writing this site. I’m hoping the same high-grade blog post from you in the upcoming also. In fact your creative writing abilities has encouraged me to get my own blog now. Actually the blogging is spreading its wings quickly. Your write up is a great example of it.
hello there and thank you for your info – I have certainly picked up anything new from right here. I did however expertise some technical issues using this site, as I experienced to reload the website a lot of times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I’m complaining, but slow loading instances times will very frequently affect your placement in google and could damage your high-quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my e-mail and could look out for a lot more of your respective intriguing content. Make sure you update this again soon..
It is perfect time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you some interesting things or suggestions. Perhaps you can write next articles referring to this article. I wish to read even more things about it!
Thanks for sharing excellent informations. Your site is very cool. I am impressed by the details that you have on this blog. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for more articles. You, my friend, ROCK! I found simply the information I already searched everywhere and simply could not come across. What a perfect web-site.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly very often inside case you shield this hike.
Thanks a lot for your post. I’d like to say that the tariff of car insurance differs a lot from one plan to another, due to the fact there are so many different facets which give rise to the overall cost. By way of example, the brand name of the motor vehicle will have an enormous bearing on the price tag. A reliable ancient family vehicle will have a less expensive premium than a flashy sports car.
Fantastic goods from you, man. I have understand your stuff previous to and you are just extremely wonderful. I actually like what you have acquired here, really like what you’re stating and the way in which you say it. You make it entertaining and you still take care of to keep it sensible. I can’t wait to read much more from you. This is actually a wonderful web site.
I want to show my respect for your generosity in support of those people that need help on that niche. Your special commitment to getting the message all through came to be certainly useful and has in every case helped others just like me to get to their goals. Your own important hints and tips denotes a great deal to me and additionally to my peers. Regards; from everyone of us.
I’m extremely impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you modify it yourself? Anyway keep up the nice quality writing, it’s rare to see a great blog like this one nowadays..
Hi, i think that i saw you visited my web site thus i came to “return the favor”.I am trying to find things to improve my site!I suppose its ok to use some of your ideas!!
Great blog here! Also your site loads up fast! What web host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
I have been absent for a while, but now I remember why I used to love this blog. Thank you, I will try and check back more often. How frequently you update your site?
I think this is among the most vital information for me. And i’m glad reading your article. But should remark on some general things, The site style is perfect, the articles is really excellent : D. Good job, cheers
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Anyway I’ll be subscribing to your feeds and even I achievement you access consistently fast.
Well I definitely enjoyed reading it. This post procured by you is very effective for accurate planning.
I just want to mention I am newbie to blogging and site-building and actually loved your web blog. Almost certainly I’m likely to bookmark your website . You really have superb stories. Regards for sharing with us your web-site.
Terrific work! This is the type of information that are meant to be shared around the internet. Shame on the seek engines for no longer positioning this publish higher! Come on over and seek advice from my web site . Thank you =)
Very well written post. It will be helpful to anybody who usess it, including yours truly :). Keep doing what you are doing – i will definitely read more posts.
Excellent site. Plenty of useful information here. I am sending it to a few pals ans additionally sharing in delicious. And certainly, thank you in your sweat!
Wow! Thank you! I continuously needed to write on my site something like that. Can I take a part of your post to my blog?
This is very interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your great post. Also, I have shared your website in my social networks!
Attractive section of content. I just stumbled upon your weblog and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently quickly.
Super-Duper site! I am loving it!! Will come back again. I am bookmarking your feeds also
I don’t even know how I ended up here, but I thought this post was great. I don’t know who you are but certainly you’re going to a famous blogger if you aren’t already 😉 Cheers!
hey there and thank you for your info – I’ve certainly picked up something new from right here. I did however expertise some technical points using this web site, as I experienced to reload the site many times previous to I could get it to load properly. I had been wondering if your web host is OK? Not that I am complaining, but sluggish loading instances times will sometimes affect your placement in google and could damage your high-quality score if advertising and marketing with Adwords. Well I am adding this RSS to my e-mail and could look out for much more of your respective intriguing content. Ensure that you update this again soon..
I have recently started a blog, the information you offer on this site has helped me tremendously. Thank you for all of your time & work.
Undeniably believe that which you said. Your favorite reason appeared to be on the net the easiest thing to be aware of. I say to you, I definitely get irked while people think about worries that they just don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people can take a signal. Will probably be back to get more. Thanks
Useful information. Lucky me I discovered your website unintentionally, and I’m shocked why this coincidence did not came about earlier! I bookmarked it.
Wow! Thank you! I constantly wanted to write on my blog something like that. Can I implement a part of your post to my website?
I am always invstigating online for tips that can benefit me. Thx!
Thanks for sharing superb informations. Your web site is very cool. I’m impressed by the details that you¡¦ve on this web site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my friend, ROCK! I found just the info I already searched everywhere and just couldn’t come across. What an ideal website.
Hello.This post was extremely fascinating, particularly since I was looking for thoughts on this issue last Wednesday.
I have been absent for some time, but now I remember why I used to love this site. Thanks , I will try and check back more often. How frequently you update your website?
Hello, i think that i saw you visited my website thus i came to “return the favor”.I’m trying to find things to improve my site!I suppose its ok to use some of your ideas!!
Hi, I do believe this is a great web site.I stumbledupon it 😉 I may revisit once again since i have savedas a favorite it. Money and freedom is the greatest way to change, may you berich and continue to guide others.
Great – I should definitely pronounce, impressed with your web site. I had no trouble navigating through all the tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your customer to communicate. Excellent task.
What i do not understood is if truth be told how you’re not really much more neatly-appreciated than you may be now. You’re so intelligent. You understand thus considerably on the subject of this matter, made me in my view believe it from a lot of various angles. Its like men and women are not interested except it¡¦s one thing to accomplish with Lady gaga! Your personal stuffs outstanding. Always maintain it up!
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such magnificent info being shared freely out there.
Excellent blog here! Also your web site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
Excellent weblog here! Also your web site so much up very fast! What web host are you the use of? Can I am getting your associate link on your host? I wish my site loaded up as fast as yours lol
Enjoyed studying this, very good stuff, regards . “If it was an overnight success, it was one long, hard, sleepless night.” by Dicky Barrett.
I truly enjoy reading through on this internet site , it holds superb content . “I have a new philosophy. I’m only going to dread one day at a time.” by Charles M. Schulz.
Can you tell us more about thisI’d like to find out moreDo you have any video of that? I’d carelikelovewant to find out more detailssome additional information.
It really is convenient opportunity to make some preparations for the foreseeable future. I’ve scan this blog entry and if I have the ability to, I desire to suggest to you you a few great suggestions.
You really make it appear so easy with your presentation however I in finding this matter to be really one thing which I believe I might by no means understand. It sort of feels too complicated and extremely huge for me. I am looking ahead on your subsequent submit, I will try to get the grasp of it!
I have not checked in here for some time because I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
I’m also commenting to let you know what a great encounter my cousin’s princess encountered reading your web page. She discovered numerous pieces, which included what it is like to possess a wonderful coaching nature to get many more with no trouble learn about chosen advanced matters. You really surpassed her desires. I appreciate you for providing these effective, safe, educational and in addition unique tips about this topic to Emily.
Great weblog right here! Additionally your site loads up fast! What web host are you the use of? Can I get your affiliate hyperlink in your host? I desire my website loaded up as fast as yours lol
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
I’ve been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my view, if all website owners and bloggers made good content as you did, the internet will be much more useful than ever before.
I like the helpful information you provide in your articles. I’ll bookmark your blog and check again here frequently. I am quite certain I’ll learn many new stuff right here! Best of luck for the next!
Hey there! Would you mind if I share your blog with my myspace group? There’s a lot of people that I think would really appreciate your content. Please let me know. Many thanks
Thanks so much for the blog article.Much thanks again. Fantastic.
Thanks-a-mundo for the blog post.Much thanks again. Cool.
I have been absent for some time, but now I remember why I used to love this blog. Thanks , I¡¦ll try and check back more often. How frequently you update your site?
You made some good points there. I looked on the internet for the issue and found most guys will go along with with your blog.
Useful information. Lucky me I discovered your web site by chance, and I am stunned why this coincidence didn’t happened earlier! I bookmarked it.
Howdy very nice web site!! Guy .. Excellent .. Amazing .. I’ll bookmark your website and take the feeds additionally¡KI am glad to seek out a lot of useful information here in the submit, we’d like work out more techniques in this regard, thanks for sharing. . . . . .
This is one awesome article.Much thanks again. Will read on…
The next time I read a blog, Hopefully it does not fail me as much as this particular one. After all, I know it was my choice to read through, nonetheless I genuinely thought you’d have something useful to talk about. All I hear is a bunch of crying about something you could fix if you weren’t too busy searching for attention.
Helpful info. Lucky me I discovered your web site accidentally, and I am shocked why this coincidence didn’t happened earlier! I bookmarked it.
Thanks for helping out, good information.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how could we communicate?
I was just seeking this info for some time. After 6 hours of continuous Googleing, at last I got it in your web site. I wonder what is the lack of Google strategy that do not rank this kind of informative sites in top of the list. Generally the top websites are full of garbage.
I haven’t checked in here for some time because I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
Magnificent goods from you, man. I have understand your stuff previous to and you are just extremely excellent. I really like what you’ve acquired here, really like what you are saying and the way in which you say it. You make it enjoyable and you still care for to keep it smart. I can not wait to read far more from you. This is really a wonderful website.
I¡¦ve recently started a site, the info you provide on this web site has helped me tremendously. Thanks for all of your time & work.
Thank you a lot for giving everyone such a remarkable chance to discover important secrets from here. It is usually very useful and stuffed with a good time for me and my office mates to search the blog more than 3 times weekly to see the new stuff you have got. Not to mention, I’m just at all times motivated with your fabulous ideas served by you. Selected 3 facts in this post are undeniably the finest we have had.
Hi, Neat post. There is a problem with your web site in internet explorer, could test this¡K IE nonetheless is the market leader and a good section of other folks will miss your great writing because of this problem.
With havin so much written content do you ever run into any problems of plagorism or copyright violation? My site has a lot of unique content I’ve either written myself or outsourced but it seems a lot of it is popping it up all over the web without my authorization. Do you know any ways to help protect against content from being ripped off? I’d definitely appreciate it.
Wow, incredible blog layout! How lengthy have you been blogging for? you make running a blog glance easy. The total glance of your website is wonderful, as smartly as the content!
You can definitely see your expertise within the work you write. The arena hopes for more passionate writers like you who aren’t afraid to mention how they believe. Always follow your heart.
Heya i am for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you helped me.
Thank you, I have just been searching for information approximately this subject for a long time and yours is the best I have came upon till now. However, what about the conclusion? Are you sure concerning the source?
But wanna admit that this is very beneficial , Thanks for taking your time to write this.
I simply could not go away your web site prior to suggesting that I actually loved the standard information an individual provide on your guests? Is gonna be again steadily in order to check out new posts.
Very interesting topic , regards for putting up. “Stranger in a strange country.” by Sophocles.
I would like to thnkx for the efforts you’ve put in writing this site. I am hoping the same high-grade website post from you in the upcoming also. In fact your creative writing abilities has inspired me to get my own blog now. Actually the blogging is spreading its wings fast. Your write up is a great example of it.
Hi there very nice web site!! Man .. Excellent .. Wonderful .. I’ll bookmark your blog and take the feeds also¡KI am glad to find numerous helpful info right here in the post, we need work out extra techniques on this regard, thanks for sharing. . . . . .
Hi there, just became alert to your blog through Google, and found that it’s truly informative. I am gonna watch out for brussels. I will be grateful if you continue this in future. Numerous people will be benefited from your writing. Cheers!
I haven¡¦t checked in here for some time since I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
Very interesting information!Perfect just what I was searching for! “He who spares the wicked injures the good.” by Seneca.
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored subject matter stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly a lot often inside case you shield this increase.
Hi, Neat post. There’s a problem with your website in internet explorer, would check this… IE still is the market leader and a good portion of people will miss your magnificent writing because of this problem.
Greetings! Quite educational guidance inside of this unique short article! It’s the minor modifications that will generate the largest modifications. Numerous due for sharing!
I absolutely love your website.. Pleasant colors & theme. Did you develop this site yourself? Please reply back as I’m attempting to create my very own site and would like to know where you got this from or what the theme is called. Cheers!
I would like to thnkx for the efforts you’ve put in writing this website. I am hoping the same high-grade web site post from you in the upcoming as well. Actually your creative writing abilities has encouraged me to get my own blog now. Actually the blogging is spreading its wings rapidly. Your write up is a great example of it.
Hello! I simply wish to give you a big thumbs up for your excellent info you have got right here on this post. I am coming back to your site for more soon.
Greetings, I think your web site might be having browser compatibility issues. When I look at your website in Safari, it looks fine but when opening in IE, it’s got some overlapping issues. I just wanted to provide you with a quick heads up! Other than that, great website!
I am not sure where you are getting your info, but good topic. I needs to spend some time learning more or understanding more. Thanks for great info I was looking for this info for my mission.
Thank you for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more from this post. I am very glad to see such magnificent information being shared freely out there.
Hey There. I found your blog using msn. This is a really well written article. I will make sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll certainly comeback.
My brother suggested I might like this blog. He was entirely right. This post actually made my day. You cann’t imagine just how much time I had spent for this information! Thanks!
Excellent web site. Lots of helpful information here. I¡¦m sending it to several friends ans also sharing in delicious. And obviously, thanks to your effort!
Great website. A lot of helpful information here. I am sending it to a few pals ans additionally sharing in delicious. And certainly, thanks for your effort!
I not to mention my friends were actually checking the great recommendations from your site and so at once developed an awful suspicion I never expressed respect to the site owner for those strategies. All the women were definitely consequently thrilled to learn them and now have actually been tapping into these things. Appreciate your turning out to be well accommodating and for deciding upon this form of terrific information millions of individuals are really eager to be informed on. My sincere apologies for not expressing appreciation to you earlier.
I like the efforts you have put in this, regards for all the great content.
I just could not depart your web site prior to suggesting that I actually loved the usual info a person provide on your guests? Is gonna be again ceaselessly to check up on new posts
Heya i am for the first time here. I came across this board and I find It really useful & it helped me out much. I hope to give something back and aid others like you helped me.
I conceive you have observed some very interesting details , thankyou for the post.
Its excellent as your other content : D, regards for posting . “Before borrowing money from a friend it’s best to decide which you need most.” by Joe Moore.
I’m extremely impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you customize it yourself? Either way keep up the nice quality writing, it is rare to see a nice blog like this one these days..
F*ckin’ awesome issues here. I am very glad to peer your article. Thank you so much and i am having a look ahead to touch you. Will you kindly drop me a e-mail?
I simply couldn’t depart your website before suggesting that I really enjoyed the usual information a person supply for your visitors? Is going to be again incessantly to check out new posts
I like the helpful information you provide in your articles. I will bookmark your weblog and check again here frequently. I am quite certain I will learn plenty of new stuff right here! Best of luck for the next!
Normally I do not read post on blogs, however I would like to say that this write-up very pressured me to try and do it! Your writing taste has been surprised me. Thanks, very great post.
I’m so happy to read this. This is the kind of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this best doc.
But wanna remark on few general things, The website layout is perfect, the subject matter is real fantastic : D.
Keep up the fantastic work , I read few posts on this site and I believe that your web blog is really interesting and contains bands of fantastic info .
I simply couldn’t go away your website prior to suggesting that I really loved the standard info a person supply in your guests? Is going to be again ceaselessly in order to investigate cross-check new posts.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how could we communicate?
You are my intake, I have few blogs and rarely run out from post :). “Fiat justitia et pereat mundus.Let justice be done, though the world perish.” by Ferdinand I.
I¡¦ve read a few good stuff here. Definitely price bookmarking for revisiting. I surprise how a lot effort you put to create the sort of wonderful informative website.
I am not sure the place you are getting your information, however good topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful information I was looking for this info for my mission.
I gotta bookmark this site it seems extremely helpful invaluable
Useful information. Lucky me I found your web site unintentionally, and I am stunned why this twist of fate did not happened earlier! I bookmarked it.
Well I really enjoyed reading it. This article provided by you is very helpful for good planning.
I’ve recently started a site, the info you provide on this site has helped me greatly. Thanks for all of your time & work. “Money is power, freedom, a cushion, the root of al evil, the sum of all blessings.” by Carl Sandburg.
I have been absent for a while, but now I remember why I used to love this web site. Thanks , I will try and check back more frequently. How frequently you update your web site?
You have brought up a very good details , thankyou for the post.
Thank you a lot for sharing this with all people you really recognise what you are speaking approximately! Bookmarked. Kindly also consult with my web site =). We could have a link exchange contract between us!
I simply wanted to make a small word in order to express gratitude to you for those splendid tips and hints you are posting on this website. My prolonged internet research has at the end of the day been rewarded with extremely good points to go over with my best friends. I ‘d point out that most of us site visitors actually are unequivocally blessed to be in a decent network with so many marvellous individuals with great techniques. I feel rather blessed to have encountered the site and look forward to tons of more amazing moments reading here. Thanks once more for everything.
Hiya, I am really glad I have found this info. Nowadays bloggers publish only about gossips and internet and this is really frustrating. A good web site with exciting content, this is what I need. Thank you for keeping this web-site, I’ll be visiting it. Do you do newsletters? Can’t find it.
Nice read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch as I found it for him smile Thus let me rephrase that: Thanks for lunch! “Procrastination is the thief of time.” by Edward Young.
Hi there, I discovered your blog by way of Google whilst searching for a related topic, your web site got here up, it looks great. I have bookmarked it in my google bookmarks.
I’ve recently started a web site, the info you offer on this site has helped me tremendously. Thank you for all of your time & work.
Great remarkable issues here. I¡¦m very happy to see your post. Thanks so much and i’m looking ahead to touch you. Will you kindly drop me a e-mail?
This seems exciting. I’d including toward attain upgrades by means of electronic mail make sure you.
I think you have observed some very interesting points , thanks for the post.
I genuinely enjoy studying on this site, it has got excellent posts . “Words are, of course, the most powerful drug used by mankind.” by Rudyard Kipling.
Excellent blog here! Also your web site loads up fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as quickly as yours lol
I am glad for writing to make you be aware of of the nice experience our child had reading through the blog. She came to find plenty of pieces, with the inclusion of what it is like to have an amazing teaching nature to have many others really easily know precisely specified impossible subject matter. You really surpassed my desires. Many thanks for showing such beneficial, dependable, educational not to mention cool tips about your topic to Jane.
hi!,I love your writing so much! proportion we be in contact more approximately your article on AOL? I require a specialist on this house to solve my problem. May be that’s you! Taking a look ahead to see you.
Hi, i think that i saw you visited my web site so i came to “return the favor”.I’m attempting to find things to enhance my web site!I suppose its ok to use some of your ideas!!
You are my intake , I own few web logs and rarely run out from to brand.
Good – I should certainly pronounce, impressed with your web site. I had no trouble navigating through all the tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, web site theme . a tones way for your customer to communicate. Excellent task.
It is my belief that mesothelioma is definitely the most fatal cancer. It’s got unusual attributes. The more I look at it a lot more I am confident it does not conduct itself like a real solid tissues cancer. If perhaps mesothelioma is a rogue virus-like infection, hence there is the probability of developing a vaccine along with offering vaccination to asbestos open people who are at high risk with developing long run asbestos associated malignancies. Thanks for discussing your ideas for this important ailment.
Wow that was odd. I just wrote an really long comment but after I clicked submit my comment didn’t appear. Grrrr… well I’m not writing all that over again. Regardless, just wanted to say great blog!
You actually make it seem so easy with your presentation but I find this matter to be actually something which I think I would never understand. It seems too complex and very broad for me. I am looking forward for your next post, I will try to get the hang of it!
Great website! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Excellent. I am also an expert in this topic so I can understand your hard work.
Hello. splendid job. I did not imagine this. This is a excellent story. Thanks!
This is really attention-grabbing, You are an overly skilled blogger. I have joined your feed and look ahead to in search of more of your fantastic post. Also, I’ve shared your web site in my social networks!
I am commenting to let you understand of the fantastic experience my friend’s girl gained going through your web page. She figured out many issues, most notably how it is like to have an incredible helping spirit to let most people very easily know precisely specific hard to do topics. You really surpassed her desires. Thank you for giving those invaluable, trusted, edifying as well as unique tips about the topic to Tanya.
What i don’t understood is if truth be told how you are no longer actually much more neatly-favored than you might be right now. You’re very intelligent. You recognize thus considerably with regards to this subject, made me for my part consider it from so many numerous angles. Its like men and women don’t seem to be interested until it is something to do with Girl gaga! Your personal stuffs great. All the time deal with it up!
Thank you for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such fantastic info being shared freely out there.
I think this is one of the most important information for me. And i am glad reading your article. But should remark on some general things, The website style is perfect, the articles is really excellent : D. Good job, cheers
you are in reality a just right webmaster. The site loading pace is incredible. It seems that you are doing any unique trick. Also, The contents are masterwork. you have done a wonderful task on this matter!
I do not even know how I ended up here, but I thought this post was good. I don’t know who you are but definitely you’re going to a famous blogger if you aren’t already 😉 Cheers!
whoah this blog is fantastic i love reading your posts. Keep up the good work! You know, a lot of people are hunting around for this info, you could help them greatly.
Thank you for sharing excellent informations. Your site is so cool. I’m impressed by the details that you’ve on this web site. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for more articles. You, my friend, ROCK! I found just the info I already searched all over the place and just couldn’t come across. What a perfect web site.
Howdy! I’m at work surfing around your blog from my new iphone! Just wanted to say I love reading through your blog and look forward to all your posts! Carry on the outstanding work!
I do agree with all of the ideas you’ve presented in your post. They’re really convincing and will certainly work. Still, the posts are very short for beginners. Could you please extend them a little from next time? Thanks for the post.
I in addition to my buddies were actually checking the excellent tricks from your web blog and all of the sudden came up with a horrible feeling I had not thanked the web site owner for those secrets. Those women ended up for this reason glad to learn them and have in effect surely been having fun with these things. I appreciate you for being very thoughtful and also for getting this kind of superior subject areas millions of individuals are really desirous to understand about. My very own honest apologies for not saying thanks to earlier.
Thanks so much for the article.Really looking forward to read more. Great.
Very good post. Will read on…
I¡¦ll immediately take hold of your rss feed as I can not to find your e-mail subscription link or newsletter service. Do you have any? Kindly permit me recognize so that I may subscribe. Thanks.
I have been absent for some time, but now I remember why I used to love this site. Thank you, I¡¦ll try and check back more often. How frequently you update your website?
Thanks for sharing this information. I found this information very useful. That’s a good blog post. I will return to read more posts.
It is actually a nice and useful piece of info. I¡¦m glad that you simply shared this useful information with us. Please stay us up to date like this. Thanks for sharing.
Hi there, just became aware of your blog through Google, and found that it’s truly informative. It’s important to cover these trends.
Great blog here! Also your web site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my website loaded up as quickly as yours lol
Wow, amazing blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is magnificent, let alone the content!
I enjoy what you guys are usually up too. This sort of clever work and coverage! Keep up the wonderful works guys I’ve added you guys to my blogroll.
It is truly a nice and helpful piece of info. I¡¦m glad that you just shared this helpful information with us. Please stay us informed like this. Thanks for sharing.
I’m partial to blogs and i actually respect your content. The article has actually peaks my interest. I am going to bookmark your site and preserve checking for new information.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how could we communicate?
wonderful post, very informative. I wonder why the opposite specialists of this sector do not realize this. You must continue your writing. I am sure, you’ve a great readers’ base already!
I¡¦m now not positive the place you’re getting your info, but great topic. I must spend some time studying more or figuring out more. Thank you for excellent info I used to be on the lookout for this info for my mission.
Hey, you used to write magnificent, but the last several posts have been kinda boring¡K I miss your great writings. Past several posts are just a little out of track! come on!
Simply desire to say your article is as astounding. The clearness in your post is simply great and i can assume you are an expert on this subject. Well with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please carry on the enjoyable work.
Pretty nice post. I just stumbled upon your blog and wanted to say that I’ve truly enjoyed browsing your blog posts. After all I will be subscribing to your feed and I hope you write again soon!
My brother recommended I might like this web site. He was totally right. This post truly made my day. You cann’t imagine simply how much time I had spent for this info! Thanks!
In accordance with my research, after a the foreclosure home is sold at an auction, it is common for that borrower to be able to still have the remaining balance on the loan. There are many creditors who try and have all service fees and liens cleared by the up coming buyer. Nevertheless, depending on specific programs, rules, and state laws and regulations there may be a number of loans that are not easily fixed through the shift of financial products. Therefore, the obligation still remains on the debtor that has obtained his or her property in foreclosure. Thank you sharing your thinking on this site.
This design is wicked! You obviously know how to keep a reader amused. Between your wit and your videos, I was almost moved to start my own blog (well, almost…HaHa!) Fantastic job. I really enjoyed what you had to say, and more than that, how you presented it. Too cool!
As I website possessor I believe the content material here is rattling excellent , appreciate it for your hard work. You should keep it up forever! Best of luck.
Great write-up, I am normal visitor of one’s site, maintain up the excellent operate, and It’s going to be a regular visitor for a lengthy time.
I have noticed that smart real estate agents everywhere are starting to warm up to FSBO Advertising and marketing. They are realizing that it’s more than simply placing a poster in the front property. It’s really concerning building relationships with these dealers who one of these days will become purchasers. So, when you give your time and effort to assisting these dealers go it alone – the “Law connected with Reciprocity” kicks in. Great blog post.
You should participate in a contest for among the best blogs on the web. I will advocate this website!
Hello my friend! I wish to say that this article is awesome, nice written and come with almost all significant infos. I¡¦d like to see more posts like this .
What i do not understood is in reality how you’re not actually a lot more smartly-favored than you may be now. You’re so intelligent. You realize therefore significantly with regards to this subject, produced me personally consider it from numerous numerous angles. Its like men and women aren’t fascinated except it is something to do with Girl gaga! Your personal stuffs great. Always handle it up!
Hi my friend! I want to say that this post is awesome, great written and include approximately all significant infos. I would like to see extra posts like this .
Great resources and tips for families here.
Glad to be one of many visitants on this amazing site : D.
I¡¦ve read several just right stuff here. Certainly worth bookmarking for revisiting. I wonder how much attempt you place to create any such great informative web site.
Your new valuable key points imply much a person like me and extremely more to my office workers. With thanks; from everyone of us.
Oh my goodness! an amazing article. Great work.
Those guidelines additionally worked to become a good way to recognize that other people online have the identical fervor like mine to grasp great deal more around this condition.
This is a great blog. Thank you for the very informative post.
My brother suggested I might like this web site. He was entirely right. This post actually made my day. You can not imagine simply how much time I had spent for this info! Thanks!
Thank you for sharing this very good post. Very interesting ideas! (as always, btw)
Great post. I was checking constantly this blog and I’m impressed! Very useful info specifically the last part 🙂 I care for such info much. I was looking for this certain information for a very long time. Thank you and good luck.
Great blog right here! You seem to put a significant amount of material on the site rather quickly.
I saw a similar post on another website but the points were not as well articulated.
Dude.. I am not much into reading, but somehow I got to read lots of articles on your blog. Its amazing how interesting it is for me to visit you very often. –
This is something that will need all of our combined efforts to address.
Having read this I thought it wasI believed it was veryreallyextremelyrather informativeenlightening. I appreciate you taking the timefinding the timespending some time and effortand energy to put this articlethis short articlethis informative articlethis informationthis content together. I once again find myselfmyself personally spending way too mucha significant amount ofa lot of time both reading and commentingleaving commentsposting comments. But so what, it was still worth itworthwhile!
Surprisingly good post. I really found your primary webpage and additionally wanted to suggest that have essentially enjoyed searching your website blog posts. Whatever the case I’ll always be subscribing to your entire supply and I hope you jot down ever again soon!
Regards for helping out, great information.
I just couldn’t leave your website before suggesting that I really enjoyed the usual information an individual supply on your visitors? Is gonna be back often in order to investigate cross-check new posts
With internet full of dupe articles it is nice to find original content like yours thank you so very much.
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my blog that automatically tweet my newest twitter updates. I’ve been looking for a plug-in like this for quite some time and was hoping maybe you would have some experience with something like this. Please let me know if you run into anything. I truly enjoy reading your blog and I look forward to your new updates.
I am really enjoying the theme/design of your site. Do you ever run into any internet browser compatibility problems? A number of my blog audience have complained about my blog not working correctly in Explorer but looks great in Chrome. Do you have any ideas to help fix this issue?
Yes I’m sure those multicultists would be made most welcome by the inhabitants of these new beginnings zones, if they chose to sell their homes and move there.I mean, those new beginnings zones are so cool and tolerant, why don’t those reports choose to live there?Why is that?
You are my inspiration , I possess few web logs and very sporadically run out from to brand 🙁
Thankyou for helping out, fantastic information.
I read this articlepostpiece of writingparagraph fullycompletely regardingconcerningabouton the topic of the comparisonresemblancedifference of latestnewestmost recentmost up-to-datehottest and previousprecedingearlier technologies, it’s awesomeremarkableamazing article.
Amazing content on your website.
Merely wanna remark that you have a very nice site, I love the style it actually stands out.
Needed to compose you a very little word to thank you yet again regarding the nice suggestions you’ve contributed here.
Great post, keep up the good work, I hope you don’t mind but I’ve added on my blog roll.
A cool post there mate ! Thank you for posting.
This is definitely a wonderful webpage, thanks a lot..
I appreciate, cause I found just what I was looking for. You’ve ended my four day long hunt! God Bless you man. Have a great day. Bye -.
I like to spend my free time by scaning various internet recourses. Today I came across your site and I found it is as one of the best free resources available! Well done! Keep on this quality!
Loving the info on this website , you have done outstanding job on the blog posts.
I cannot thank you more than enough for the blogposts on your website. I know you set a lot of time and energy into these and truly hope you know how deeply I appreciate it. I hope I’ll do a similar thing person sooner or later.
Thanks a lot for the high caliber and results-oriented assistance. I won’t think twice to endorse your blog post to anyone who wants and needs support about this area.
Appreciating the persistence which you place into your site and thorough information you provide.
Hello! This is my first visit to your site! We are a team of volunteers and beginning a brand new initiative in a community in precisely the same niche. Your blog supplied us helpful information to work on. You have done an outstanding job. {
Nice read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch since I found it for him smile Thus let me rephrase that: Thanks for lunch!
Hi, Neat post. There’s an issue along with your site in web explorer, could check this… IE nonetheless is the market leader and a big part of other folks will miss your excellent writing due to this problem.
I just want to tell you that I am very new to blogging and site-building and really liked this website. Most likely I’m planning to bookmark your blog . You surely have perfect articles and reviews. Kudos for sharing your website.
Woh I enjoy your content , saved to bookmarks!
You ma’am have a way with words. Thank you very much!
Those guidelines additionally worked to become a good way to recognize that other people online have the identical fervor like mine to grasp great deal more around this condition.
Needed to compose you a very little word to thank you yet again regarding the nice suggestions you’ve contributed here.